Protecting Sensitive Data in the Age of AI
Empower secure AI adoption while reducing data risks
Evaluate your organization's readiness to manage AI-related data risks | Take the Assessment
AI and data challenges
Organizations face increasing data challenges in the age of AI, including complex infrastructure, resource restrictions, and sophisticated threat actors. Protecting sensitive data requires a solution that addresses key AI data risks.
Did you know ...
Data protection is at risk
1. McKinsey, The state of AI in 2025: Agents, innovation, and transformation
2. Accenture, State of Cybersecurity Resilience, 2025
3. IBM, Cost of a Data Breach Report, 2025
Protect sensitive data and accelerate secure AI adoption with Trellix
Trellix Professional Services
Align with global regulations and enterprise AI use policies. Support training for security teams and end users. Fine-tune security controls and optimize technology solutions.
Trellix Data Loss Prevention
Monitor and block potential data leaks, and track sensitive data sharing across 400+ GenAI tools in real-time from a central dashboard. Address risky user behavior and take advantage of built-in compliance tools.
Trellix Database Security
Protect critical data stores and repositories that feed your AI models from compromise, theft, or poisoning. Secure databases without downtime and block potential SQL injection attacks.
Trellix Data Encryption
Secure data from AI scraping tools and autonomous agents. Keep data encrypted to prevent proprietary information from being inadvertently ingested or used for unauthorized model training.
Trellix Data Security Suite
Comprehensive protection across the data ecosystem with advanced features, such as Optical Character Recognition (OCR). Include Database Security for the most complete protection.
Frequently asked questions
Enterprises face critical data exposure through several key exposure points, including native AI in productivity suites, built-in agents in SaaS platforms, third-party URL-based tools, specialized business apps, and vendor/supplier AI systems. Data can be lost through activities such as active sharing (e.g., copying code or uploading files), passive sharing via insecure APIs, and external threats such as prompt-injection attacks designed to extract sensitive information from AI models.
Shadow AI refers to the use of unsanctioned AI tools by employees outside of IT visibility. This creates significant security gaps, as proprietary data or source code can be ingested by public models without oversight. According to recent data, this inaction can add an average of $670,000 to the cost of a data breach. The Trellix DLP AI Data Risk Dashboard helps mitigate this risk by providing visibility into over 400 predefined URL-based AI tools, allowing you to track authorized and unauthorized usage.
If sensitive information is visible to an AI tool, it can be ingested for model training. This occurs through active user sharing—such as uploading files or copying and pasting code—as well as through passive data sharing via insecure interfaces or tools that grant excessive access to enterprise data. Trellix Data Encryption establishes a rigorous boundary by rendering sensitive files unreadable to both authorized and unauthorized AI scraping tools as as well as autonomous agents, ensuring your IP remains protected even if it is inadvertently accessed.
Maintaining the integrity of data stores is critical for accurate AI outcomes. Trellix Database Security monitors for anomalous transfers and unauthorized access by AI agents, enabling the instant termination of suspicious sessions. It also detects and blocks sophisticated, AI-automated SQL injection attacks. This ensures your proprietary data is not manipulated or poisoned while keeping your critical databases patched and secure without requiring downtime.
Related resources

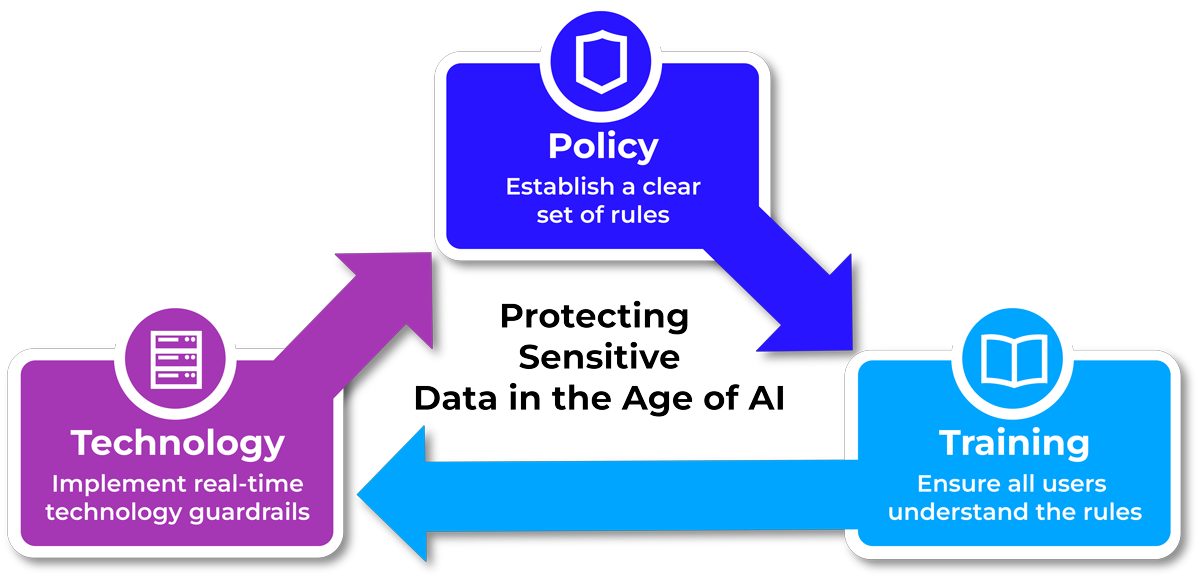
The Trellix solution accelerates secure AI adoption through a holistic approach that prioritizes protecting sensitive data.

Learn how the AI Data Risk Dashboard empowers organizations to securely adopt AI by identifying potential sensitive data leakage.

The AI data risk tipping point has arrived. Learn how to transform AI from a potential data risk into a secure productivity engine.