Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more
Preparing for the AI Tidal Wave: Securing Critical Enterprise Data
By Laurie Robb · April 8, 2026
The rapid expansion of Generative AI has transformed the enterprise landscape in record time. While AI tools offer unprecedented workflow optimization and productivity gains, they have also introduced evolving security challenges, especially for those organizations with complex data ecosystems and significant compliance requirements. For many, the shift from attempting to block AI tools to securely adopting them is both necessary and risky.
The AI data risk tipping point has arrived
As of late 2025, 88% of businesses reported officially implementing AI in at least one business function. However, official adoption is only half the story. The emergence of "Shadow AI"—the use of unsanctioned or unapproved AI tools by employees—is creating significant, unmanaged risks. And even with approved AI tools, users may not always adhere to the established guidelines for acceptable use.
The stakes are high when you consider the expansion of AI into the enterprise. Organizations are under increasing pressure from several key challenges.
- Data exposure: Sensitive data is increasingly vulnerable to leakage because it serves as both an input and an output in generative AI tools.
- Costly breaches: Security incidents involving Shadow AI add an average of $670,000 to the cost of a data breach.
- Sophisticated attacks: Bad actors are now utilizing AI-driven tactics, such as prompt injections, to manipulate AI models and bypass traditional security controls.
- Governance concerns: Data privacy and security (73%), legal compliance (50%), and governance oversight (46%) are the primary AI-related risks for security and business leaders.
Enterprise hot spots for AI data risk
Today’s enterprise faces several critical AI exposure points where sensitive information can be compromised. As AI capabilities are integrated into everyday tools and specialized AI software promises greater efficiency, organizations face increasing risks of data loss and compromise across their infrastructure. Some of the most likely exposure points include:
- Productivity suites: Modern daily workflows now revolve around native AI integrations in email, document editors, and spreadsheets—such as Microsoft Copilot and Google Gemini—which can process and store vast amounts of internal communication and proprietary data.
- Embedded SaaS applications: Many core business platforms, including Customer Relationship Management (CRM), Human Resources Information Systems (HRIS), and Enterprise Resource Planning (ERP) systems, now feature built-in AI agents that have access to confidential customer records and organizational intelligence.
- URL-based and third-party web tools: Some of the most popular GenAI interfaces are browser-based, including ChatGPT, Google Gemini, Claude, and Grok. They can be used to brainstorm ideas, create content, analyze proprietary designs, draft product plans, or debug internal code, often unknowingly feeding sensitive corporate IP into external models.
- Function-specific specialized tools: High-risk data exposure can also occur within specialized applications tailored to technical roles, such as AI-driven coding assistants for developers or automated financial reporting tools, which are increasingly spreading across the enterprise.
- Vendor and supplier AI interdependencies: Security risks extend beyond your perimeter to include the AI applications used by third-party partners and suppliers granted access to your sensitive data as part of the supply chain.
A framework for secure AI adoption
To transform AI from a potential data risk into a secure productivity engine, Trellix recommends a holistic, three-phase framework.
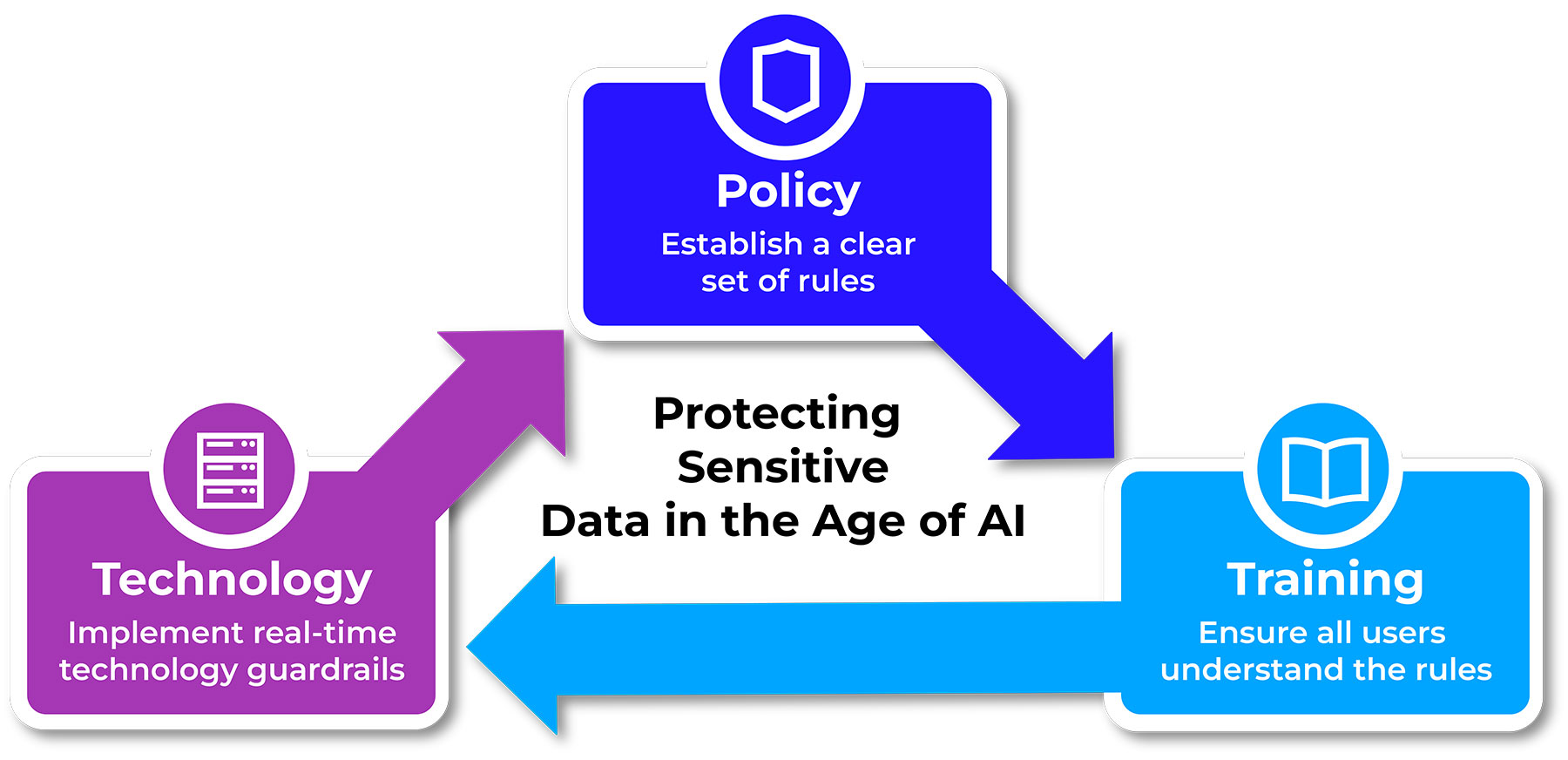
Policy: Establish clear expectations
Establish clear, actionable guidance that aligns with corporate standards and emerging global regulations. Organizations must create understandable policies that designate authorized uses, identify approved tools, and define protocols for handling sensitive content. Policies will need to be updated regularly because AI risks are rapidly evolving.
Training: Ongoing education
The human element of risk is substantial, and because AI technologies are changing so fast, it’s critical to deliver ongoing training and “in the moment” coaching for everyone with access to enterprise data. Education should focus on acceptable use, reinforced by real-time notifications for policy violations, and creating a culture of AI awareness.
Technology: Gain visibility and control
Technology can enforce enterprise policies and reinforce user training. Modern Data Security technology can help defend against the risk of data loss and compromise by:
- Blocking exfiltration: Prevent sensitive data from being copied or uploaded into AI tools and models.
- Educating in real time: Notify users who attempt to violate information sharing policies and provide “in the moment” education on acceptable use.
- Identifying Shadow AI: Monitor the transfer of sensitive data to find when information is shared with unauthorized applications.
- Defending databases: Detect and block large transfers of unauthorized information and stop prompt injection attacks, while ensuring databases are secured from vulnerabilities
- Safeguarding critical data: Use encryption to render files unreadable to unauthorized AI "scraping" or ingestion.
Secure the future of AI adoption
The integration of AI into the enterprise is occurring more rapidly than many anticipated when the first generative AI tools leapt onto the technology stage just a few short years ago. This present-day reality demands a multi-layered response. While the rapid expansion of AI across productivity suites, SaaS platforms, and specialized tools offers immense potential for growth, it also broadens the surface area for data exposure and potential for sophisticated cyberattacks.
Protecting your organization’s most sensitive information requires more than just a collection of security tools; it requires a proactive framework that balances clear policy, continuous user education, and robust technology programs. Most organizations are already struggling to keep up with these demands. Trellix offers a comprehensive suite of Data Security solutions and a global team of experts that can support all aspects of the secure AI adoption framework. Trellix is making protecting sensitive data in the age of AI a priority solution for our customers and partners.
Take the next step
RECENT NEWS
-
Apr 08, 2026
Trellix prevents enterprise data exposure in sanctioned and shadow AI
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
-
Dec 11, 2025
Trellix Finds 97% of CISOs Agree Hybrid Infrastructure Provides Greater Resilience
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.
