Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more
New Trellix Detection Rules: Get the Full Story of a Lateral Movement Attack
By Grant McDonald · August 11, 2025
Ever had a pest problem in your home? You probably didn’t know you had a problem until little indicators of a growing, hidden presence happened. The pests were likely already inside your environment for a time but they avoided being seen. Lateral movement attacks are similar in that they aim to hide inside your security walls. Lateral movement happens inside your network with attackers blending in, exploiting a foothold and using subtle tactics to avoid being seen.
Our researchers are not only looking for new tactics, they are also creating new detections, rules and informing our analytics to halt attacks like lateral movement before attackers gain a foothold.
A recent blog post by our research team details some of their latest findings and how these attacks can be visualized. While the post explores three use cases, I'll focus on the first two for those less familiar with threat detection engineering or research.
Specifically, we'll examine a lateral movement attack involving remote service session hijacking and another where an attacker abuses Microsoft Excel to gain unauthorized access.
Gaining a unified view of an attack story
In the first example, the attack begins with the adversary exploiting vulnerabilities and using social engineering tactics to gain initial access.
Next, the attacker executes a command to list all active and disconnected user sessions. This gives them names, user data, session IDs, and additional information to identify a target to hijack. After connecting to the target session, they create a new service that gives them control without authentication prompts or alerts being issued.
To combat these attacks, Trellix Helix Connect combines logs and telemetry data from endpoint and network defenses. As the attack unfolds, all alerts generated by the detection rules for this use case are listed at each stage. This provides an early warning at the first sign of malicious activity.
To simplify the process for analysts, Trellix Helix Connect consolidates related alerts into a single correlated alert, offering a unified view of the attack story instead of requiring analysts to piece together individual alerts.
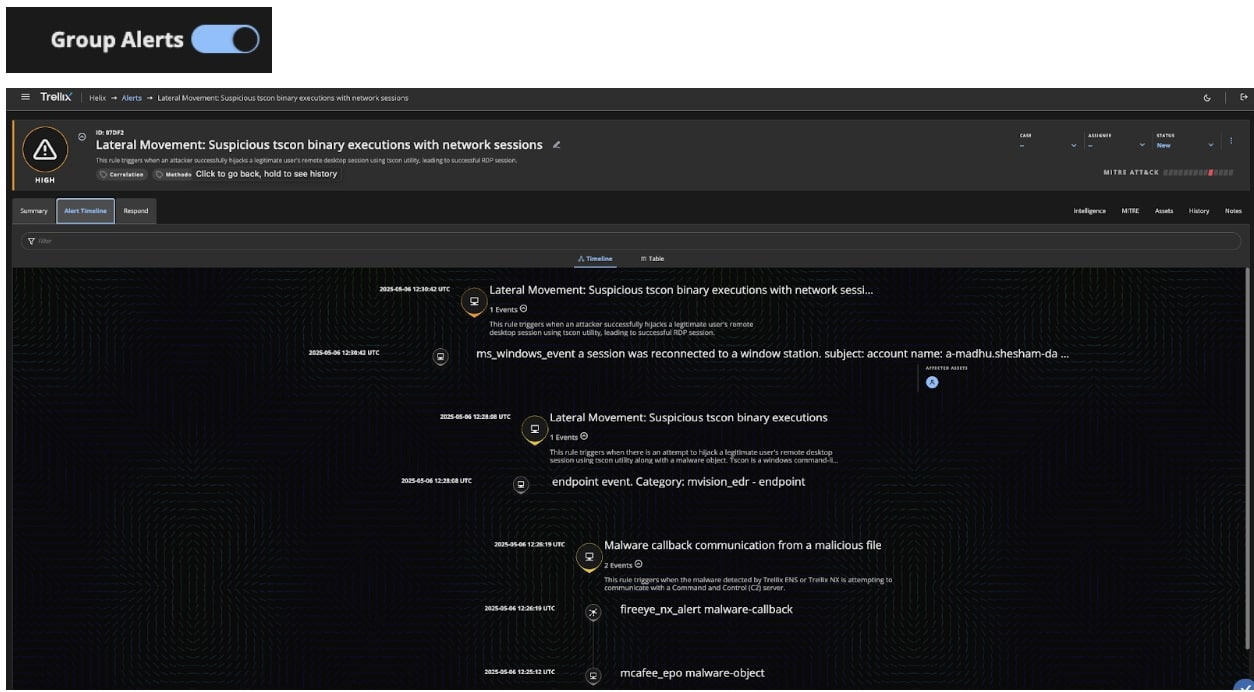
With this grouped view, analysts can see the endpoint where the attack began, the attacker’s IP address, and the host systems involved, enabling them to quickly see what responses to take. In this case, that consists of containing the affected systems, blocking network traffic to the attacker, resetting passwords of compromised accounts, and quarantining the attacker-modified registry keys.
In the second example, the attack begins with the execution of a malicious file, then leverages exploits to harvest a user’s credentials. From there, the attacker transfers a suspicious file to a network share and performs a lateral movement to another system.
They do this by exploiting a process in the Excel application that allows them to start a new process, disguising it as a legitimate one. They are then able to execute processes remotely as if they are happening within the victim’s environment to evade network defenses.
Once again, using Trellix Helix Connect, we are able to pull together this story for clearer, more straightforward context of the who, what, why, and when of the attack.
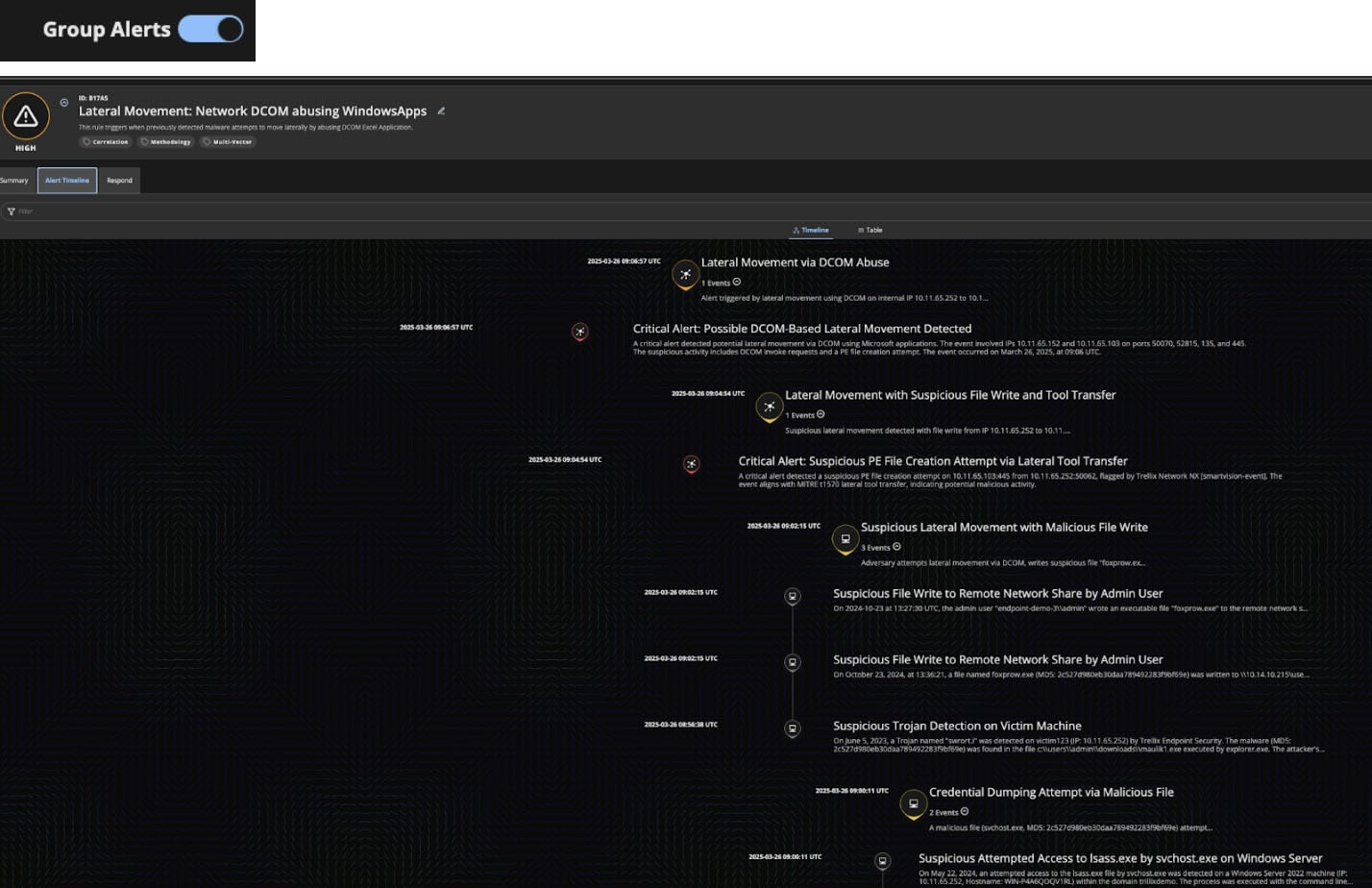
Instead of just telling us that indicators of lateral movement were detected, in Figure 2 we see the summary at the top indicating that the attacker’s intended goal was to exploit DCOM in Microsoft Excel, followed by the timeline of events. Separately, a Network Administrator may have investigated one alert and an Endpoint Administrator another. With this combined, summarized view, both administrators can see how their work to remediate and put preventative measures in place is intertwined.
These are just two examples of how our research teams are actively discovering new attacks and developing detections for them using Helix Connect within the Trellix Security Platform. Stay tuned as we will continue to unveil new use cases in the weeks and months ahead as we make them available to our customers!
In the meantime, learn more about Trellix Helix Connect.
RECENT NEWS
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
-
Dec 11, 2025
Trellix Finds 97% of CISOs Agree Hybrid Infrastructure Provides Greater Resilience
-
Oct 29, 2025
Trellix Announces No-Code Security Workflows for Faster Investigation and Response
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.
