Vulnerability Research and Red Team
The Vulnerability Research team includes skilled security researchers and analysts. They uncover and report hardware and software vulnerabilities to improve the security of products and services used globally. We deliver these insights and research ahead of the market and advise organizations around the world.
The people behind these efforts are widely sought-after experts who support classified investigations, speak at industry events, and educate influencers across media, academia, and the public sector. Our Red team is composed of ethical hackers conducting tests to strengthen Trellix's security defenses.

Research Spotlight
CVE-2023-23397: The Notification Sound You Don’t Want to Hear
During "Patch Tuesday", a new Outlook security vulnerability was revealed as being exploited in the wild. We discuss how it works, the risks, and mitigations.
Read MoreTrellix Advanced Research Center Discovers a New Privilege Escalation Bug Class on macOS and iOS
The Trellix Advanced Research Center vulnerability team has discovered a large new class of bugs that allow bypassing code signing to execute arbitrary code in the context of several platform applications, leading to escalation of privileges and sandbox escape on both macOS and iOS.
Read MoreTrellix Advanced Research Center Patches 61,000 Vulnerable Open-Source Projects
Late last year, the Trellix Advanced Research Center team uncovered a vulnerability in Python’s tarfile module. As we dug in, we realized this was CVE-2007-4559 – a 15-year-old path traversal vulnerability with potential to allow an attacker to overwrite arbitrary files. We’re excited to share an update on this work.
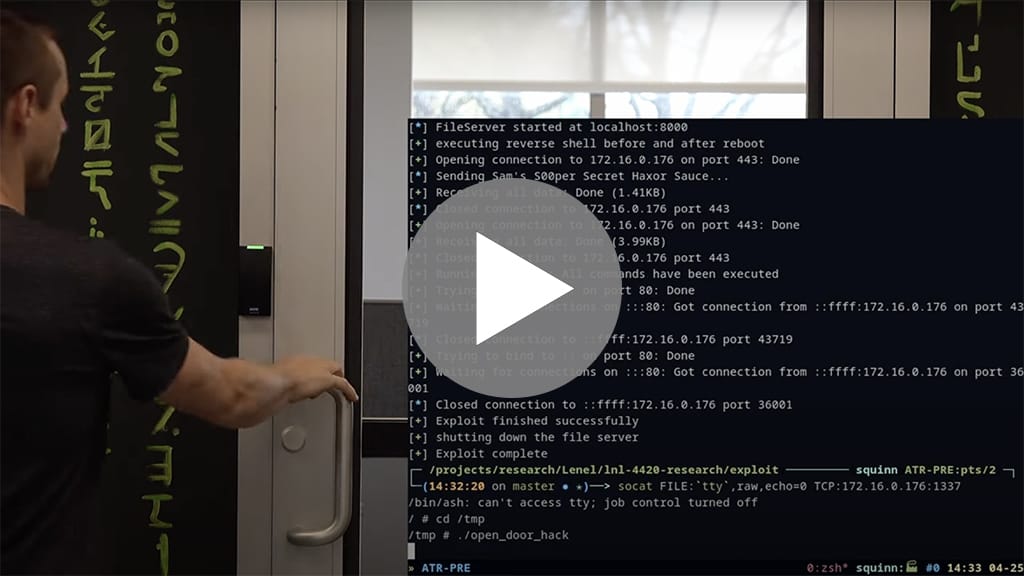
Read MoreTrellix Threat Labs Uncovers Critical Flaws in Widely Used Building Access Control System
Vulnerabilities in an industrial control system used to grant physical access to privileged facilities and integrate with more building automation deployments.
Read MoreThe OpenSSL Who Cried “Severity: High
This blog will dive into CVE-2023-0286, a type confusion vulnerability that is exercised when OpenSSL processes X.509 GeneralNames containing X.400 addresses.
Read MoreOpen-Source Intelligence to Understand the Scope of N-Day Vulnerabilities
The zero-day is the holy grail for cybercriminals; however, N-day vulnerabilities can pose problems even years after discovery. They continuously find their way into new projects as well perpetuating their danger. Unfortunately, open-source software (OSS) can also suffer from unpatched N-days.
Read MoreTrellix HAX 2023:
Annual Capture the Flag
Trellix’s Advanced Research Center launched on February the Trellix HAX 2023, our third annual capture the flag (CTF) competition! With 12 new challenges of varying skill levels to test participants mettle against and a SANS course as the first-place prize
See the Results!
Trellix HAX 2022:
Annual Capture the Flag –
Catmen San Fransisco
The Advanced Threat Research team announced our second annual Capture the Flag contest featuring 12 new challenges of varying skill levels, and a Discord server to facilitate competitive collaboration. For this contest, we decided to add a bit of story – so put on your 90’s nostalgia hats, as you assist our heroine, Catmen Sanfrancisco (clearly no relation to Carmen Sandiego).
Read the Story