Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more
Trellix HAX 2023 Capture the Flag Results!
By Mark Bereza · March 17, 2023
This story was also written by Jesse Chick.
All good things must come to an end, and our annual CTF is unfortunately no exception. When this competition began, we asked each of you to try your hand at 12 new challenges – whether you were a CTF veteran or a fresh-faced newb. We asked each of you to talk shop with fellow contestants and engage with us directly in our Discord server. We asked each of you to immerse yourselves in this year’s narrative, set in a post-apocalyptic U.S. ravaged by nuclear fallout and on the brink of a cyber civil war between the East and West coasts. We are pleased to announce that you’ve done that and so much more!

With the top-scoring teams vetted and solutions posted, it’s time to finally announce the winners, discuss some analytics, and decide once and for all which coast is Best Coast™.
The Winners
1st
2nd
3rd
4th
5th
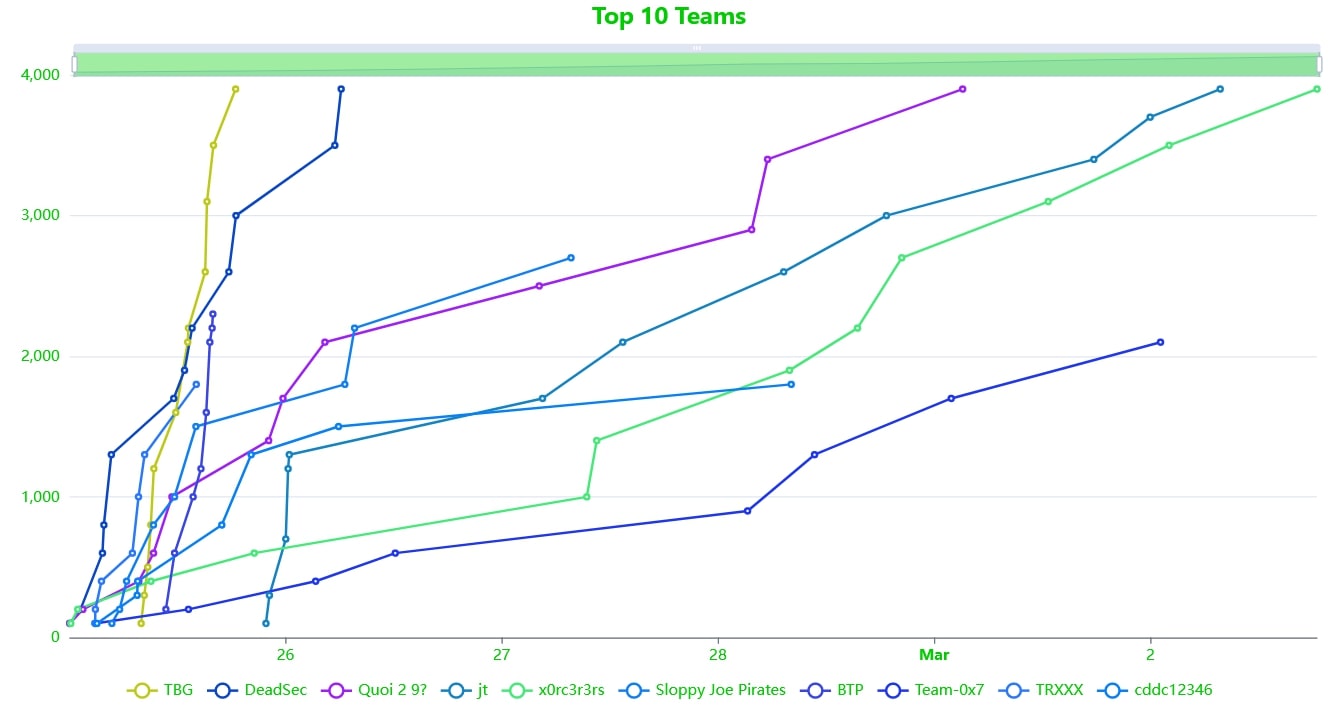
First off, we’d like to congratulate this year’s winning teams for each achieving a perfect score of 3900 and doing so within the first week of the competition!
As promised, every member of these top five teams has earned an exclusive Trellix HAX 2023 challenge coin designed by us. If nothing else, organizing this competition has been an enlightening foray into the intricacies of international shipping. We just hope the glow in the dark effect is still visible next to minds so bright 😉.
We’d also like to give special kudos to TheBadGod, captain and sole member of the first-place team TBD, and winner of this year’s grand prize: a SANS course. Although we’ve received consistent feedback stating that this year’s challenges were our hardest yet, they proved no match for TheBadGod, who managed to perform a clean sweep less than 18 hours after the CTF launched. TheBadGod didn’t rest on their laurels, however, and remained active on the Discord server throughout the remainder of the competition – providing us with valuable feedback and other players with some helpful nudges in the right direction. Once the radioactive dust had settled, TheBadGod went on to post write-ups for multiple challenges in the Discord server, giving some insight into the methods of a top-tier hacker.
In that same vein, we’d like to give a shoutout to green-panda999, captain of the fifth-place team, who posted in-depth write-ups for over half the challenges on their website. They were another active participant in our Discord server and always a joy to interact with.
Analytics
As organizers, this is the part we’re most excited about: engagement. We’re thrilled to say that we’ve managed to reach our widest audience yet, with almost five times the participation across the board when compared to last year:
We were also pleased to learn that our choice of narrative being U.S.-centric did not seem to discourage international players, as we had contestants from over 100 different countries! I suppose shipping a dozen coins internationally is a small price to pay if it means that kind of cosmopolitan engagement.
On the subject of challenges, we’re happy to say that we achieved our goal of covering a wide range of difficulties, with our 100-point challenge “We Need to Break Free” proving particularly accessible with over 250 solves, while our harder 400- and 500-point challenges had less than 10.
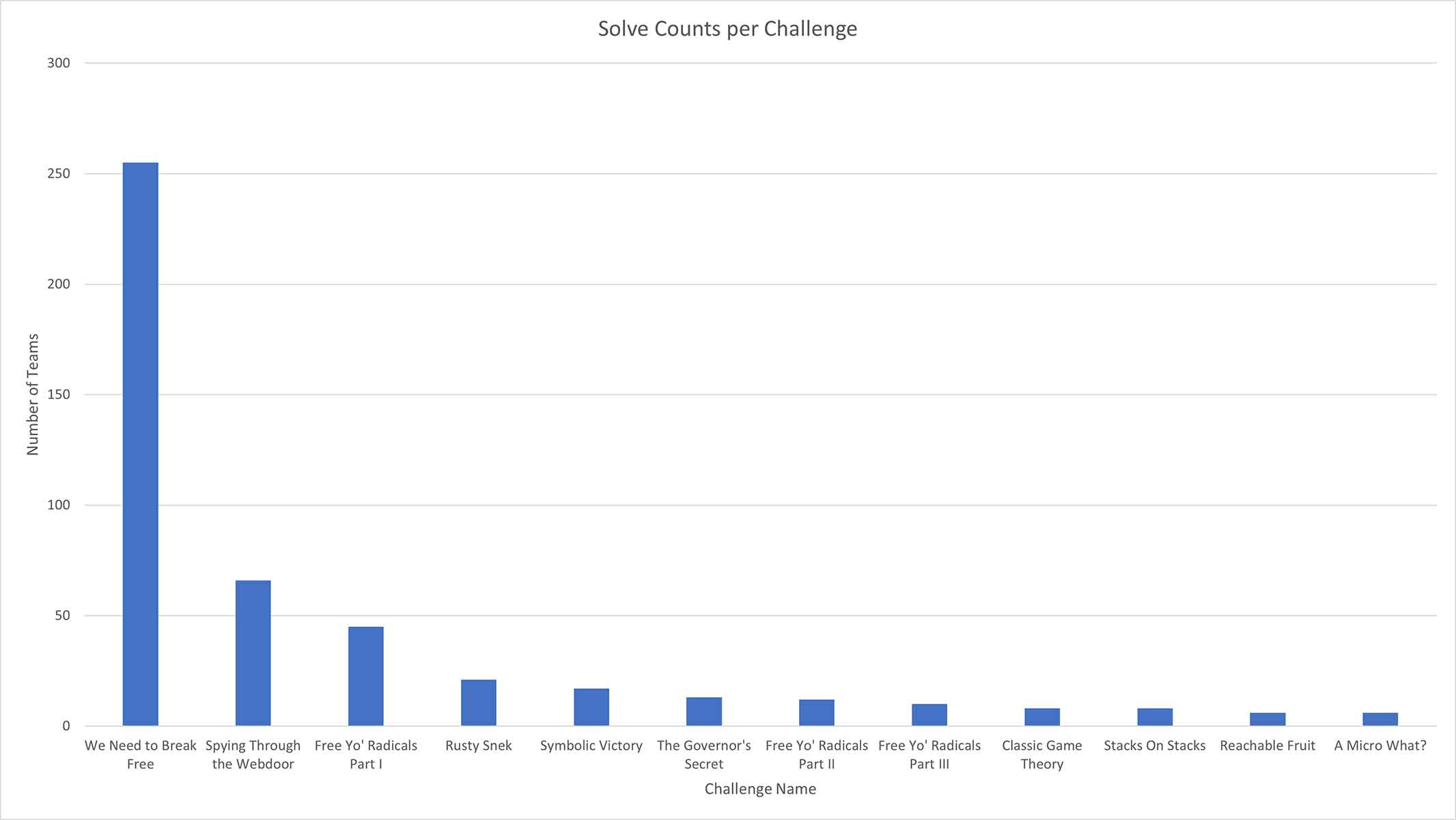
Interestingly, the challenges with the fewest solves were actually “Reachable Fruit” and “A Micro What?” – both 400-point challenges. Perhaps we should spend more time tuning the scores for next year?
While capping winners at the top five teams is typically an arbitrary threshold, we feel a bit vindicated in that decision knowing that the top five teams were the only ones to achieve the maximum possible score of 3900, with sixth place coming in at 2700. For those curious where they placed, we’ve posted the final scoreboard here.
Moving onto the burning question of East vs. West, we were somewhat surprised to see the East clean up in just about every metric (full disclosure: the authors of this blog are both West coasters). Besides the first-place team repping the East coast colors, the East represented four of the top five teams, and the cumulative total for East-aligned teams was almost double that of the West-aligned ones.
While the West was certainly the underdog in this war, having far fewer teams to its name, the East teams performed well both individually and in aggregate, achieving a higher average score per team. We hate to admit it, but the East coast is undoubtedly the Best Coast™ this time around.
Narrative Epilogue
After a lengthy campaign of espionage, reconnaissance, and good old-fashioned hacking, the East's advantage in numbers and expertise proved decisive. Having recognized the monolithic nature of the West's ad hoc state-run computer systems, and the means to strike at its heart, the East prepared its final payloads. Over the course of twenty-four hours, Eastern hackers gained access to the West's core computing infrastructure, encrypted drives, deleted master boot records, and rendered nearly seventy percent of the centralized system unusable. On behalf of the millions in the West reliant on continued state support and logistics simply to survive, the head of government in the West agreed to unconditional surrender. The digital chokehold was loosened, humanitarian operations resumed, and the nation of two coasts were once again united under one flag. With the civil conflict put to rest, efforts on both sides returned to ensuring that that flag could not be so easily captured from abroad…
Closing Thoughts
In our years of hosting CTF competitions, we’ve learned that there’s inevitably going to be some things that don’t go according to plan. This time around, we had a challenge that granted those exploiting it a little too much control and, inevitably, hackers did what hackers do.
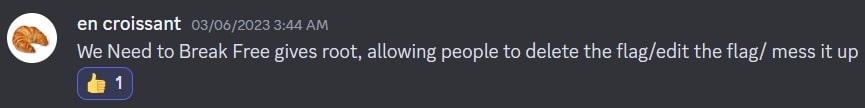
Fortunately, our contestants were great sports about the whole thing and made sure to notify us whenever something broke, ensuring that the show could go on. For our part, we plan to learn from these hiccups and continue to improve our CTFs moving forward, in the same way we continually strive to improve our research and learn from our peers in the cybersecurity community.
Until next year, thanks again and don’t forget to 【HACK THE PLANET】!
RECENT NEWS
-
May 19, 2026
Trellix Appoints Joe Chen as Chief Technology Officer
-
Apr 08, 2026
Trellix prevents enterprise data exposure in sanctioned and shadow AI
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.


