Protect against stealthy threats
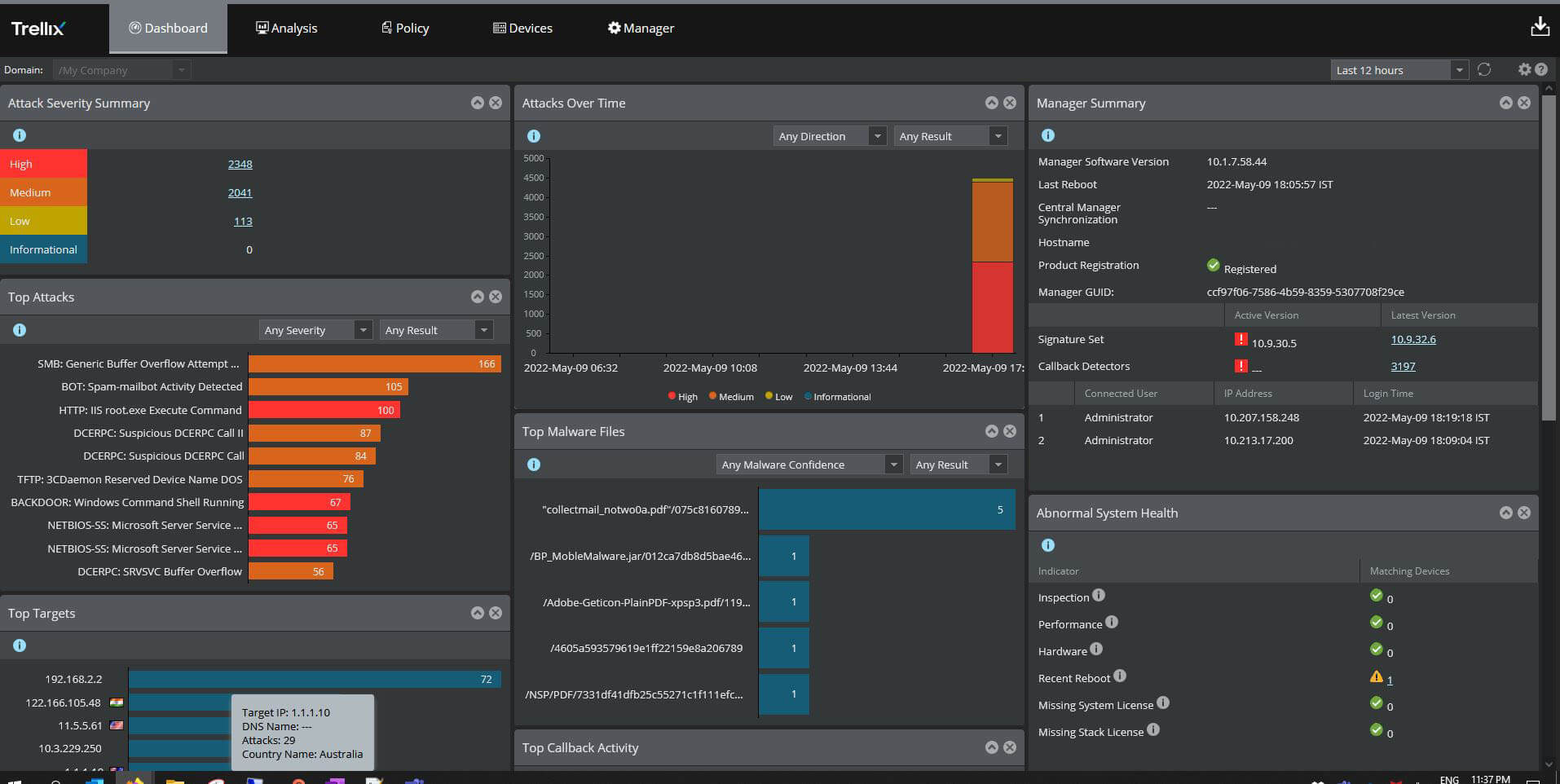
Trellix Intrusion Prevention System (IPS) is an NDR-ready, next-generation IPS that detects and blocks sophisticated malware threats across the network. It uses advanced detection and emulation techniques, moving beyond traditional pattern matching to defend against stealthy attacks with a high degree of accuracy and performance.
Did you know ...
Trellix Data Security statistics
000+
File formats supported by Trellix Data Loss Prevention
00M+
Drives protected worldwide by Trellix Data Encryption
000+
Patch protections delivered by Trellix Database Security
Why Trellix IPS?
Superior Detection
Combines multiple signature and signature-less detection capabilities into a single solution.
Seamless Protection
Scalable IPS architecture designed for hybrid networks from on-prem, virtual, to cloud environments.
High Performance
Provides automatic scaling for elastic workloads and on-prem appliances up to 100 Gbps.
Product features
Trellix Intrusion Prevention System products
Deploy in the cloud and on-prem.
Trellix IPS+ for AWS
- Protects assets for known and unknown exploits.
- Employs Trellix IVX to detect exploits before they enter the network.
- Integrates with AWS Gateway Load Balancer for automatic scaling.
Trellix IPS for On-Premises
- Identifies and blocks threats across the network.
- Uses advanced detection and emulation techniques.
- Defend against stealthy attacks with accuracy, speed, and scale.
Trellix Virtual IPS+
- Protection for private and public clouds (AWS, Azure, and OCI).
- Auto-scaling with Cloud Gateway Load Balancer support for AWS and Azure.
- NDR ready for AI-driven analysis and ML threat detections and investigation
Complementary services to accelerate your success
Installation and Configuration
Integration and Training
Monitoring and Optimization
Industry recognition
Trellix is recognized as an industry leader by key analyst firms
Frequently asked questions
Security awareness
What is Network Security
A combination of technologies, policies, and practices to protect computer networks and data's confidentiality, availability, and integrity.
Read MoreWhat is NDR?
NDR goes beyond essential intrusion detection to continuously monitor your network traffic for suspicious activity.
Read MoreIDS vs. IPS: Key Differences Explained
IDS and IPS are vital network security tools used to identify cyberattacks. While both aim to protect enterprise networks, their core functions and methods differ.
Read MoreRelated resources

Despite its reputation as a mature, commodity, technology, IPS (Intrusion Prevention Systems) are still an essential part of network security strategy.

In this blog post, we'll explore how the integration of Trellix vIPS with GWLB can bolster customers’ infrastructure's capabilities.
Trellix IPS+ provides signature-based detection that protects vulnerable assets from exploit, and can stop DDoS, C2 callbacks, and more.