Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more
Go Jump in the Lake: Trellix Leverages Amazon Security Lake for its Extended Detection and Response (XDR)
By Christopher Unick · May 30, 2023
Data Lakes have been around for a decade, usually to quickly solve any discussions you may have about how your business is storing and utilizing its data. Simply by saying “Hey, let’s create a data lake” to solve your organization’s data issues, you are swiftly rewarded as a forward thinker and who leverages technology on the cutting edge. But it’s much easier said than done. How do you realistically take every piece of relevant data your company creates, utilize it in a timely manner and incorporate it into your ever - evolving security landscape? It sounds daunting, and it can be. So, why jump into such a project? Not to worry. Amazon Web Services and Trellix are here to help you jump into the best data lake for your security needs.
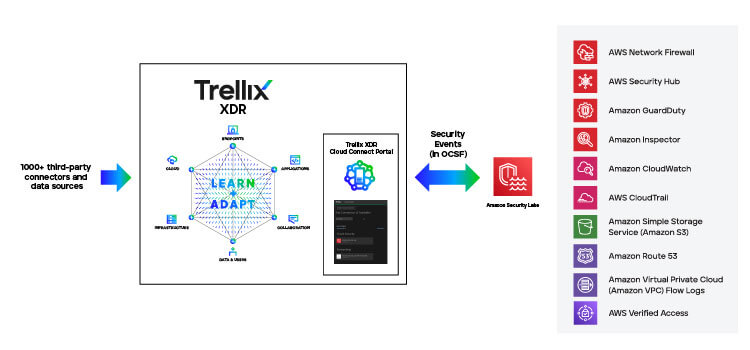
As customers try to keep pace with dynamic attacks and ensure greater peace of mind, they are on the lookout for more centralized visibility and quick resolution of their security issues. Trellix is at the forefront of the XDR revolution—pioneering a brand-new way to bring detection, response, and remediation together in a single living security solution. The Trellix XDR platform seamlessly integrates with our broad portfolio of endpoint, email, network, cloud, and other security products. Providing industry-leading integrations with an additional 1000+ security and business applications, we equip customers with intelligent threat sensing, analytics, and automated response.
Today, Trellix is collaborating with AWS to make it easier for customers to store and analyze their event data by integrating with Amazon Security Lake, a data lake for a customer’s entire security telemetry, that directly integrates to Trellix Helix. Trellix’s new extended capability enables customers to consolidate their security alerts into Amazon Security Lake, making it easier for security teams to have greater control and visibility across their security environment.
What is Amazon Security Lake?
Amazon Security Lake is a data lake for security logs, built in the customer’s account. It’s backed by an Amazon Simple Storage Service (Amazon S3) bucket and organizes data as a set of Lake Formation tables. Amazon Security Lake is designed to optimize the cost of storing and querying massive security log sources, while maintaining good query performance and compatibility with a wide variety of analytic infrastructure. Security Lake customers retain low-level ownership of their data. Security Lake also delivers a set of core AWS- native security logs, minimizing costs and maximizing performance.
What data can be leveraged between Amazon Security Lake and Trellix Helix?
Pretty much anything! Trellix leverages the new Open Cybersecurity Schema Framework (OCSF) in parquet format to get data from Security Lake. OCSF includes an open specification for the normalization of security telemetry across a wide range of security products and services, as well as open-source tools that support and accelerate the use of the OCSF schema. Any data that makes it into this new data lake is instantly analyzed, along with over 650 data sources that already exists in Trellix Helix. All this data ingested into Trellix Helix is then correlated with other security risks, providing customers with the necessary playbooks to respond to a risk in a timely manner. The OCSF framework greatly benefits our partners, who can package their data needs into an easily consumable format that can be leveraged in Helix rapidly. This levels the data playing field and allows us to focus on what we do best, finding and responding to threats. Anyone can participate in the evolution of the specification and tooling at https://github.com/ocsf.
Benefits of Leveraging Amazon Security Lake with Trellix Helix
This integration benefits customers in two unique ways: lower operational overhead and better control of your data with the ability to run analytics off your security data. By leveraging Amazon Security Lake, customers simplify their operations for ingesting and processing data by having a single data lake that can be used for all their security data. Customers no longer have to set up multiple paths/destinations which removes a step to allow customers to see and respond to their data faster. They no longer need to maintain custom integrations and simplify their delivery of data to Trellix Helix, and now they can consolidate their Trellix security findings back into Amazon Security Lake. This allows Trellix to focus on finding and responding to threats while customers maintain better control of their security data, and it abides by their privacy policies.
There has never been a better time to go jump in a lake! Start leveraging the speed and efficiency available between Amazon Security Lake and Trellix to respond to security issues today. Please reach out to aws@Trellix.com to learn more and to start a free trial of Trellix Helix today!
RECENT NEWS
-
May 19, 2026
Trellix Appoints Joe Chen as Chief Technology Officer
-
Apr 08, 2026
Trellix prevents enterprise data exposure in sanctioned and shadow AI
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.
