Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more
Beyond the Cloud – Trellix Earns 2026 OT Security Certification
By Sanjay Raja · March 16, 2026
In the world of operational technology (OT), "connected" isn't always a good thing. For the critical systems that keep our lights on and water flowing, the "air-gap"—physical and internet isolation—is a crucial line of defense for these sensitive infrastructures. However, attackers are finding ways across that gap via removable media, insider threats, and increasing requirements for some cloud/internet connectivity. In general, how do you protect a system that shouldn’t frequently "phone home" to the cloud for the latest updates, signatures, and analytics?
We are proud to announce that Trellix Endpoint Security (ENS) has officially earned the AV-Comparatives 2026 Operational Technology Protection Certification.
The toughest test in security
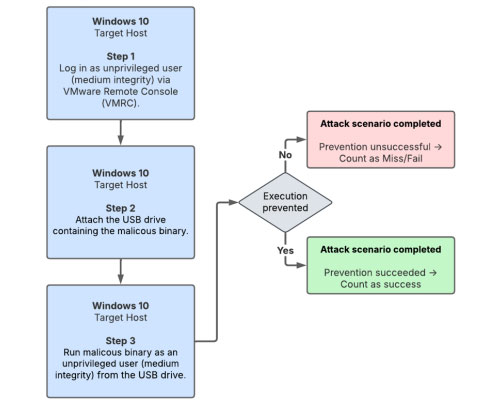
The AV-Comparatives OT Certification isn't your standard malware test. It assumes the worst-case scenario: a "post-breach" environment where an attacker already has local access to a system. The systems are Windows 10 workstations operating in 100% offline conditions. No cloud. No internet. No external reputation services.
LAST REVISION: 16TH FEBRUARY 2026 WWW.AV-COMPARATIVES.ORG
Proven performance against advanced TTPs
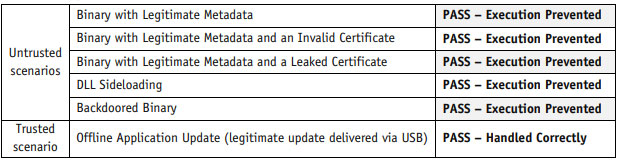
Trellix was subjected to a gauntlet of execution-based attacks using techniques frequently seen in nation-state and industrial espionage campaigns. Trellix ENS successfully prevented every single malicious scenario, including:
LAST REVISION: 16TH FEBRUARY 2026 WWW.AV-COMPARATIVES.ORG
Security that doesn't stop production
One of the biggest fears in OT is a "false positive"—security software blocking a critical update and causing a multi-million dollar outage. A key component of our certification was the Application Update Test. Trellix correctly distinguished between a malicious file and a legitimate signed installer delivered via USB, allowing the update to complete without disruption while maintaining a hardened security posture.
| Details | Details / Results |
| Product tested | Trellix Endpoint Security (ENS) |
| Certification | AV-Comparatives 2026 Operational Technology Protection |
| Test environment | 100% Offline Windows 10 Workstations (No Cloud/Internet) |
| Attack scenarios | Execution-based attacks, nation-state, and industrial espionage TTPs |
| Prevention rate | 100% of malicious scenarios prevented |
| False positive test | Successfully distinguished between malicious files and signed legitimate updates |
| Key technologies | Adaptive Threat Protection (ATP) and ML Protect (localized machine learning) |
| Outcome | Hardened security posture without sacrificing operational uptime |
AI at the edge
How did we do it without the cloud? The answer lies in our Adaptive Threat Protection (ATP) module and ML Protect. By using localized machine learning and behavioral classification, Trellix ENS identifies "maliciousness" based on action and intent, not just a list of known bad files.
For organizations managing critical infrastructure, the message is clear: You don't have to sacrifice advanced protection for operational isolation. With Trellix, your most sensitive environments remain secure, compliant, and—most importantly—operational.
[Read the full AV-Comparatives report here:
https://www.av-comparatives.org/wp-content/uploads/2026/02/avc_OT-cert_trellix_2026.pdf]
To learn more about Trellix Endpoint Security Solutions please visit:
https://www.trellix.com/platform/endpoint-security/
RECENT NEWS
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
-
Dec 11, 2025
Trellix Finds 97% of CISOs Agree Hybrid Infrastructure Provides Greater Resilience
-
Oct 29, 2025
Trellix Announces No-Code Security Workflows for Faster Investigation and Response
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.
