Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more
How A Simple Misconfiguration Can Fuel Offline Attacker Tools
By Grant McDonald · April 9, 2026
It’s no secret that misconfigurations are a gateway for attackers. But that doesn’t mean misconfigurations won’t happen or that attackers won’t attempt to exploit them.
In the latest research from our team of analysts, Adithya Chandra and Maulik Meheta found a new trick using a common attack path. This time, a single script allows a compromise without authentication credentials.
How it works
It’s a familiar story at first - an attacker steals credentials from an endpoint. Then they download malicious tools that look for accounts with a particular misconfiguration. In this case, accounts that don’t require Microsoft Active Directory to preauthenticate them. From there, the attack focuses on sending requests to a service that will respond with encrypted material from user passwords.
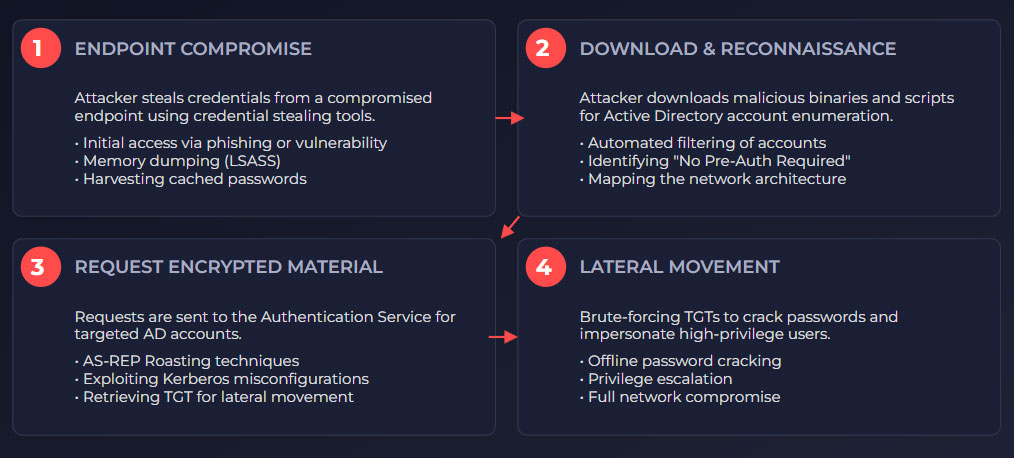
You might think encrypted data would be safe in this scenario, but as always, attackers find ways to reach their goals. Using offline tools designed to break encryption, they can obtain credentials that allow them to impersonate valid users or keep moving around your network to do more harm.
Network security tools may alert to some of this activity, but will your team be able to respond to the full scope of the attack before the attacker can abscond with your data? You need to be able to detect not just one action but a behavioral pattern of malicious activity across multiple layers.
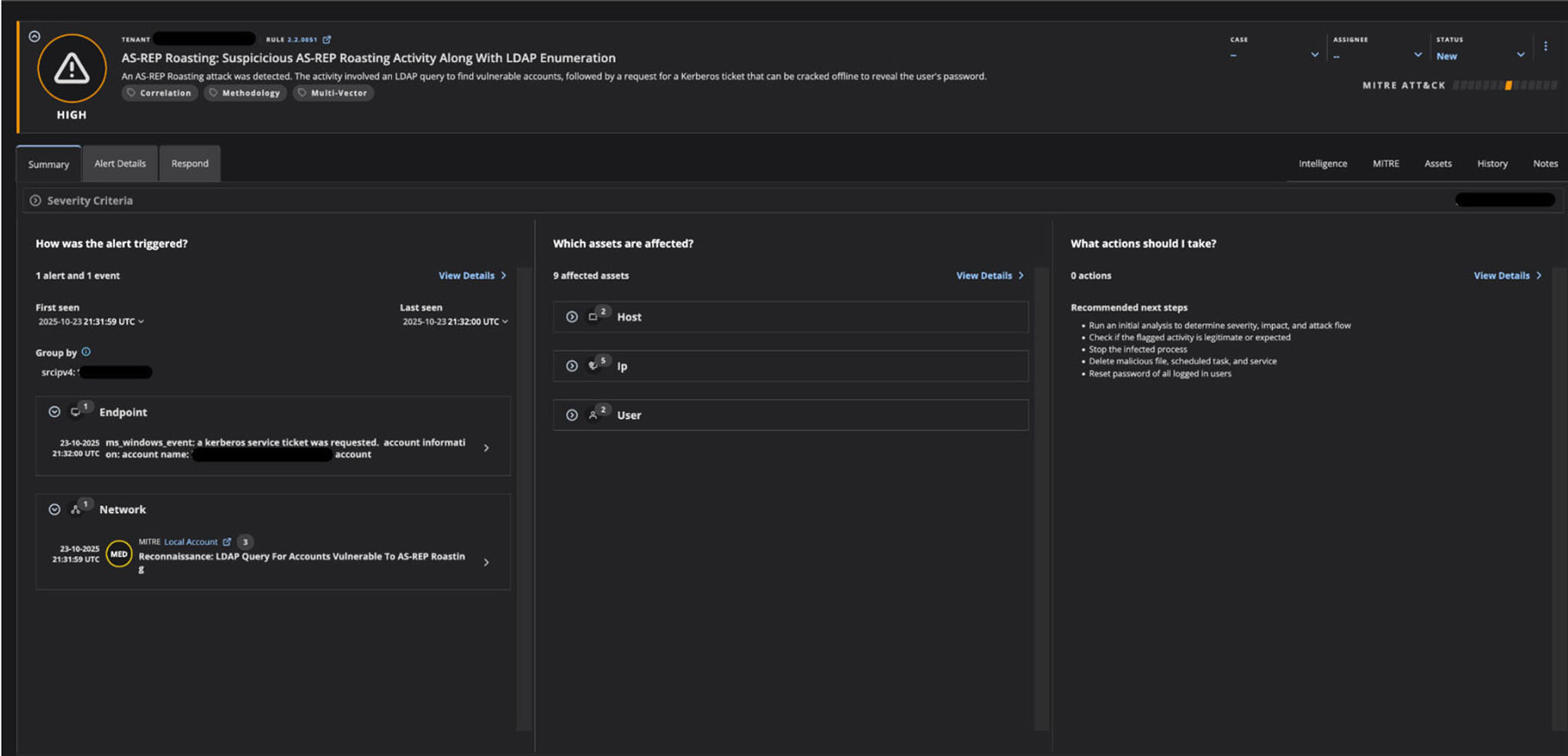
How to detect the pattern
Behavioral pattern analysis and correlation across multiple sources of telemetry data are key to stopping these forms of attack. When authentication requests that target accounts with preauthentication disabled (note: we recommend changing this setting; see our full list of recommended actions here) are analyzed alongside data from endpoint and network detections, the pattern emerges. Vulnerable accounts, configurations, compromised systems, and unusual network behaviors are correlated into a story with a high-severity alert issued for incident responders. This multi-source, behavioral approach is also a consistent way to ensure attacks are surfaced, even if the tools or methods used change.
Trellix Helix not only detects these types of attacks, but it also chronologically links attack events, providing analysts with the complete kill chain. This temporal perspective is essential for understanding adversary progression across multiple security data sources. Helix lists the endpoints, accounts, and network addresses involved, making it easy to prioritize containment and remediation of any impacted assets.
To learn more about this attack technique and get guidance on remediation check out the full blog by our research team. To see Trellix Helix in action check out our product tour or request a demo.
Discover the latest cybersecurity research from the Trellix Advanced Research Center: https://www.trellix.com/advanced-research-center/
RECENT NEWS
-
Apr 08, 2026
Trellix prevents enterprise data exposure in sanctioned and shadow AI
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
-
Dec 11, 2025
Trellix Finds 97% of CISOs Agree Hybrid Infrastructure Provides Greater Resilience
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.
