Trellix Data Loss Prevention
Protects sensitive information across top threat vectors
Exceptional visibility and comprehensive controls
Trellix Data Loss Prevention (DLP) delivers unprecedented protection for sensitive and proprietary information from the keyboard to the cloud. Get industry-leading discovery and classification, deploy policies across top threat vectors, respond to events in real-time, coach users, and generate reports.
Did you know ...
Trellix Data Security statistics
000+
File formats supported by Trellix Data Loss Prevention
00M+
Drives protected worldwide by Trellix Data Encryption
000+
Patch protections delivered by Trellix Database Security
Why Trellix Data Loss Prevention?
Protect Against Insider Risk
Prevent data exfiltration. Coach end users attempting to violate policy.
Quickly Demonstrate Compliance
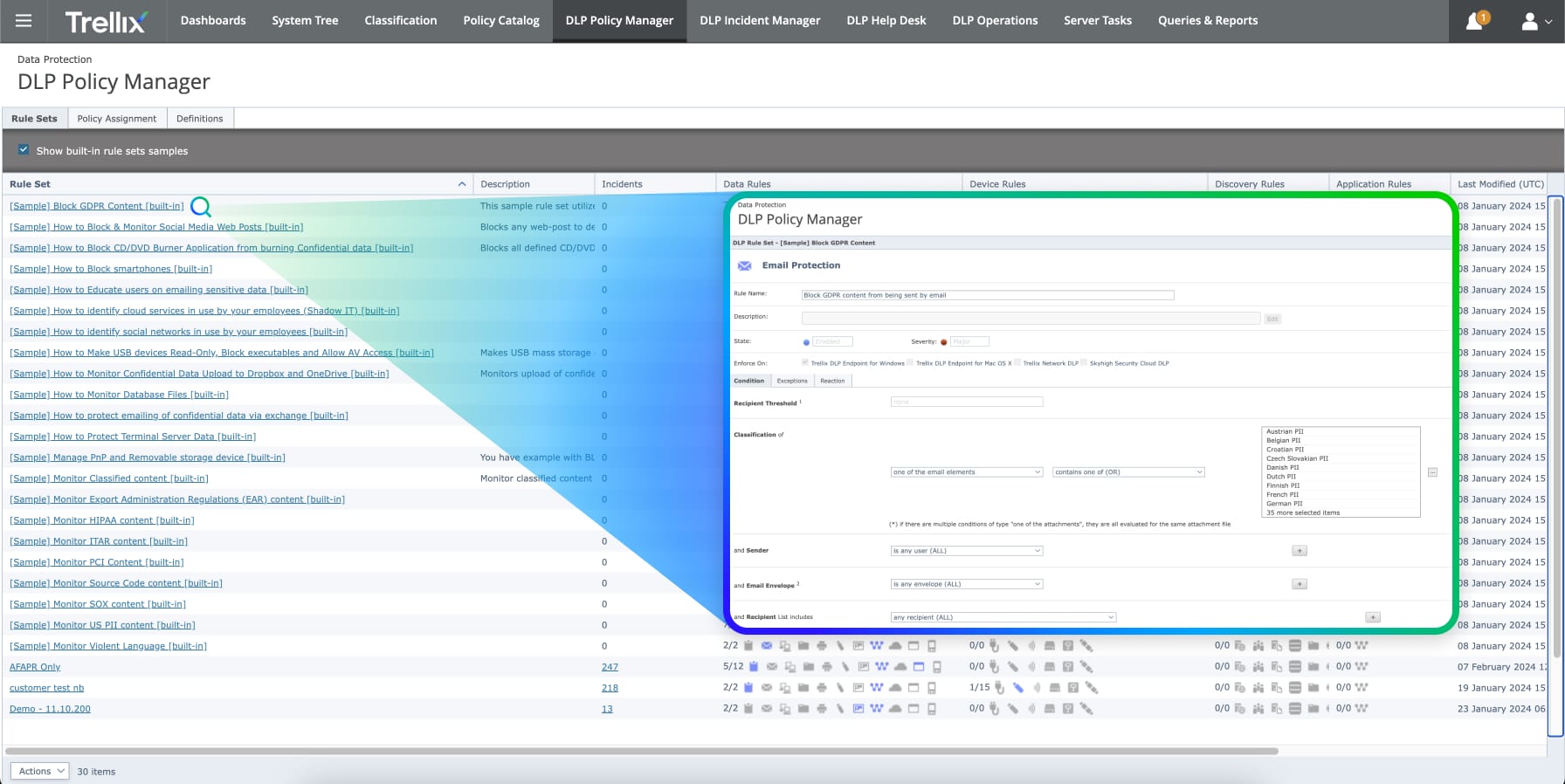
Out-of-the-box rules and reporting aligned with key regulatory frameworks.
Manage Information Footprint
Find, classify, and protect the data that matters to your organization.
Product features
Trellix Data Loss Prevention products
Trellix Data Loss Prevention Endpoint Complete
Includes Trellix Device Control, available on-premisis and via SaaS
- Find and classify data on Windows and macOS workstations and servers
- Coach end-users and request justifications for policy exceptions
- Get out-of-the-box compliance features, including reporting
Trellix Device Control
Protect Windows and macOS workstations and servers on-premises or via SaaS
- Prevent unauthorized device installation
- Deploy policies for content-based monitoring, filtering, and blocking
- Available as a stand-alone or included in Trellix DLP Endpoint Complete
Trellix Data Loss Prevention Discover
Inventory senstive data across networks, storage and database locations.
- Find and classify sensitive data across more than 400 file types
- Capture and retain data to aid forensics and investigations, add on for OCR
- Support compliance activities and reporting out of the box
Trellix Data Loss Prevention Network Monitor
Visibility for sensitive data shared across networks.
- Scan, analyze, and detect network data events in real time
- Collect information to speed investigations , add on for OCR
- Support compliance activities and reporting out of the box
Trellix Data Loss Prevention Network Prevent
Prevent users from sharing unauthorized information across networks.
- Integrates policies with email and web gateways to protect sensitive information
- Captures information to support investigations, forensics, add-on for OCR
- Support compliance activities and reporting out of the box
Data Sheet
Trellix Data Loss Prevention AI Data Risk Dashboard
Identify risks and accelerate secure AI adoption. Learn how the Trellix DLP AI Data Risk Dashboard helps you support compliance objectives and enforce AI usage policies across the enterprise.
Read the Data SheetComplementary services to accelerate your success
Installation and Configuration
Integration and Training
Monitoring and Optimization
Industry recognition
Trellix is recognized as an industry leader by key analyst firms
Related resources

Data exfiltration is a primary goal of ransomware attackers. Learn how to protect your data with Trellix Data Loss Prevention.

What problems does Data Security solve, and what capabilities should your solution include? Take a look at the future of Data Security.

Learn how Trellix DLP extends protection to content in Google Chrome Enterprise, Microsoft Edge for Business, Firefox, and Island.

AI services like ChatGPT can present risks for your organization's data. Learn to take a proactive approach and prevent sensitive data leakage.