Cyber Readiness in Europe: France, Germany & the United Kingdom
By Trellix · April 14, 2022
Concerns over cyber-warfare activity in Ukraine has rekindled discussion of the cyber readiness of government agencies and critical infrastructure in Europe. The commencement of hostilities raised the specter of wiper malware in the form of WhisperGate and the more recent HermeticWiper.
Even before the hostilities commenced in Ukraine, countries such as Germany, the United Kingdom and France have for some time been increasingly facing sophisticated attacks on government agencies and organizations providing critical infrastructure services:
- In 2018, the United Kingdom’s National Cyber Security Centre (NCSC) announced that that Russian hackers had successfully penetrated the computer networks of the country's energy grids, and, in August 2021, the United Kingdom’s Department of Transport reported nine attacks on the country’s transportation sector.
- In December 2021, France’s ANSSI (short for Agence Nationale de la Sécurité des Systèmes d'Information) announced that the threat actor behind last the SolarWinds attacks had also been targeting French organizations since February 2021.
- Last month, Europol reported a series of cyber-attacks on port oil depots in Germany, the Netherlands and Belgium—a particularly frightening revelation given Germany’s reliance on energy imports.
This blog focuses on the survey results of the Trellix Cyber Readiness Report conducted by Vanson Bourne in late 2021. Two hundred cybersecurity professionals from government agencies and critical infrastructure providers with 500 or more employees were surveyed in Germany, the United Kingdom, and France.
The government survey subjects included a mix of national and regional agencies. Critical infrastructure providers (CIPs) included traditional utilities providing electricity, water, oil and gas providers. They also included telecommunications and network service providers (traditional phone, IT network and internet services, broadcast services, etc.), public and private healthcare providers (hospitals, medical clinics, urgent care centers, etc.), transportation and distribution providers, state and local government service providers (including first responders and emergency services), and manufacturers of transportation, healthcare (pharmaceutical, etc.) and chemical products.
What emerges is a snapshot of the state of these countries’ cyber readiness in areas such as software supply chain risk and challenges, barriers to implementation of new cybersecurity solutions, the impact and legacy of the COVID-19 pandemic on cybersecurity postures, and the current and potential role of government in strengthening cybersecurity for these organizations.
Barriers to New Cyber Defenses
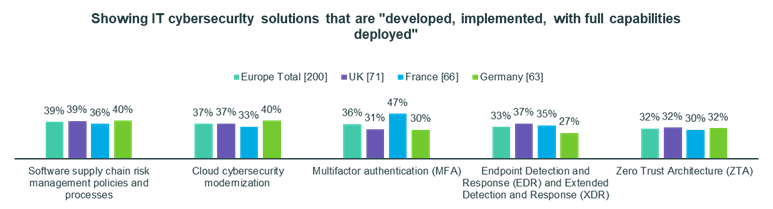
Maturity of Advanced Cyber Defenses. The survey gauged the priorities, difficulties and progress of their implementations of new cyber defense technologies such as cloud cybersecurity modernization, endpoint detection and response and extended detection and response (EDR-XDR), multifactor authentication (MFA) and zero trust architecture (ZTA).
Forty percent of German respondents claim to have fully implemented cloud cybersecurity modernization and only 32% appear to have fully implemented zero trust. The cyber defense technologies lagging furthest behind in Germany appear to be MFA (only 30%) and EDR-XDR (only 27%).
Among United Kingdom respondents, EDR-XDR and cloud cybersecurity modernization were the most mature new cyber defense solutions, with 37% of respondents claiming full deployment in each area. Zero trust was close behind with 32% claiming full deployment, and MFA appears to be furthest behind at 31%.
Forty-seven percent of French respondents reported having fully deployed MFA, apparently placing the French furthest ahead in this area compared to their UK and German peers. Thirty-five percent reported fully implementing EDR-XDR. Cloud cybersecurity modernization and zero trust appear to be behind with only 33% and 30% fully implemented respectively.
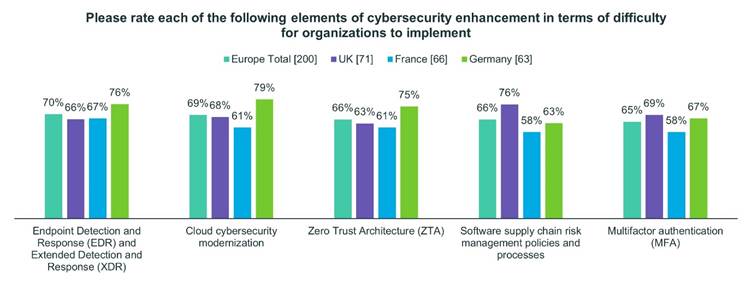
Among British respondents, 69% appeared to identify MFA as a highly or extremely difficult cybersecurity technology to implement, compared to cloud cybersecurity modernization (68%), EDR-XDR (66%) and zero trust (63%).
Cloud cybersecurity modernization appeared to be a difficult technology to implement among German respondents, with 79% identifying it as difficult. This was more prominent an issue than EDR-XDR (76%), zero trust (75%) and MFA (67%).
Sixty-seven percent of French respondents identified EDR-XDR as difficult to implement, compared to cloud cybersecurity modernization (61%), zero trust (61%) and MFA (58%).
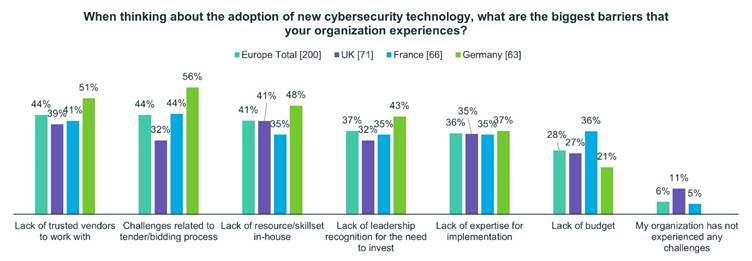
Forty-one percent of U.K. respondents identified lack of staff resources as one of the biggest barriers to implementing new cybersecurity solutions. Thirty-nine percent of respondents identified a lack of trusted partner vendors to assist with implementation and 35% identified their own lack of implementation expertise.
Forty-four percent of French respondents identified challenges related to the tender bidding process as a barrier. These respondents also identified other barriers in the lack of trusted partner vendors (41%), lack of sufficient budget (36%), lack of leadership recognition for the need to invest (35%) and lack of staff resources in-house (35%).
Fifty-six percent of German respondents identified challenges related to the tender bidding process as one of their biggest barriers. Other prominent barriers included the lack of trusted partner vendors (51%), lack of staff resources in-house (48%), lack of leadership recognition for the need to invest (43%), and lack of their own implementation expertise (37%).
Software Supply Chain Risk
The software supply chain attacks on SolarWinds and Microsoft in 2020 and 2021 forced organizations to realize the seriousness of software supply chain cyber threats and how complicated it is to protect against them. They also realize that their governments can play a significant role in their defense.
Seventy-six percent of U.K. respondents identified software supply chain risk management policies and processes as extremely or highly difficult to implement, and only 39% claim to have fully implemented such practices.
Sixty-three percent of German respondents and 58% of French respondents identified these policies and processes as difficult to implement. Only 40% of German respondents and 36% of French respondents acknowledge fully implementing such measures.
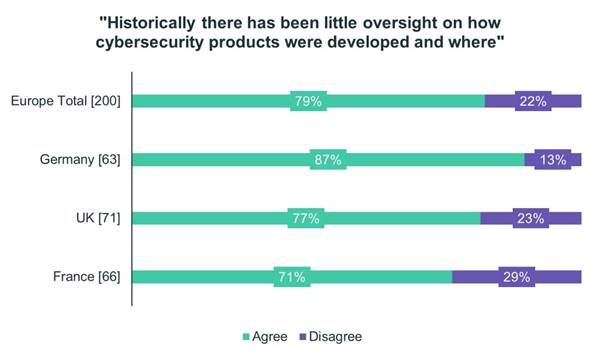
Eighty-seven percent of German respondents, 77% of U.K. respondents and 71% of French respondents voice concerns that there has historically been little oversight over how cybersecurity products themselves were developed and where.
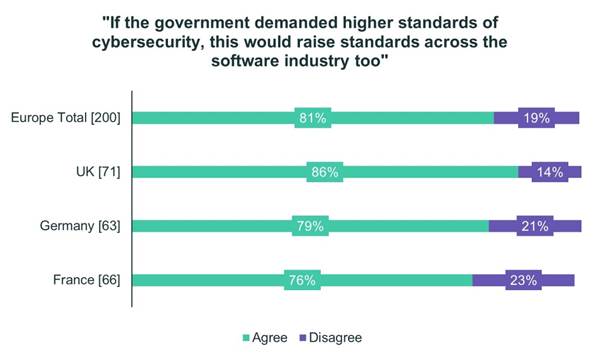
Respondents from U.K., Germany and France agree by wide margins that if governments prescribe higher software cybersecurity standards, this would raise such standards across the entire software industry.
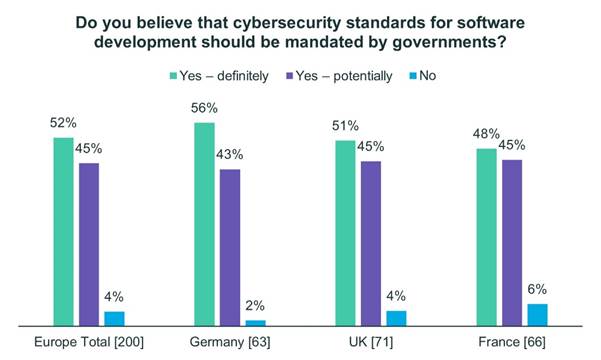
Fifty-six percent of German respondents, 51% of U.K. respondents and 48% of French respondents support government mandates demanding cybersecurity standards for software.
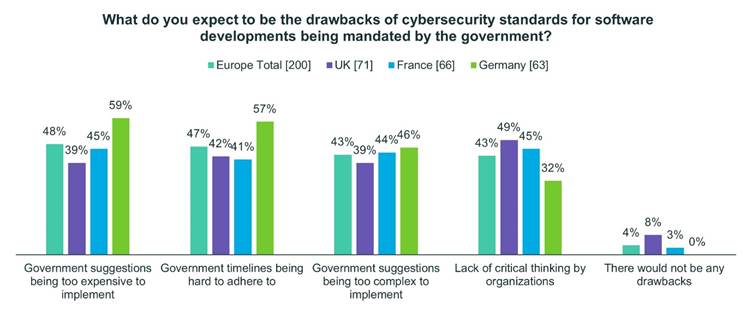
That said, respondents from all three countries have concerns that there could be drawbacks to such standards. Fifty-nine percent of German respondents believe such mandates could result in government suggestions that are ultimately too expensive to realistically implement. Fifty-seven percent believe government timelines will be difficult to meet, and 46% believe government suggestions will be too complex to implement.
Around half of British respondents believe government software security mandates will result in a lack of critical thinking among organizations forced to comply. Forty-two percent believe government timelines will be difficult to meet and slightly less believe the mandates will be too complex (39%) and expensive (39%) to implement.
Forty-five percent of French respondents were concerned with standards impacting critical thinking, with the same proportion worried about implementation costs, 44% feared complexity of implementation, and 41% were concerned with meeting government timelines.
Role of National Governments
Beyond the software supply chain issues, the survey found a number of areas where respondents believe their national governments should be playing a stronger role in strengthening their cybersecurity posture.
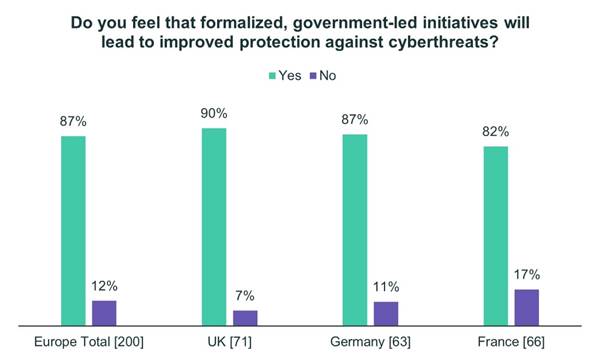
Ninety percent of British respondents, 87% of German respondents and 82% of French respondents believe that formalized, government-led initiatives will lead to improved protection against cyberthreats. Ninety-five percent of German and French respondents and 86% of British respondents believe there is room for improvement in terms of the level of partnership between their national governments and organizations based in their country in terms of overcoming cyberthreats.
Fifty-two percent of British respondents favored a combination of incident notification and liability protection to facilitate sharing of cyber-attack data between impacted organizations, government partners and industry audiences. Forty-one percent supported tighter cooperation on cyber incident management while attacks are in progress, improved guidance on best practices, and tighter cooperation on the investigation of attacks following their discovery. Only 25% favored more regulations.
Forty-six percent of Germans supported a combination of incident notification and liability protection to facilitate sharing of cyber-attack data between impacted organizations, government partners and industry audiences. Forty-four percent favored tighter cooperation on cyber incident management while attacks are in progress, 41% supported greater consequences when malicious actors are caught, and 40% favored improved national government funding of their cybersecurity and improved guidance on best practices. Thirty-eight percent favored tighter cooperation on the investigation of attacks following their discovery, 21% supported fewer regulations and 17% support more.
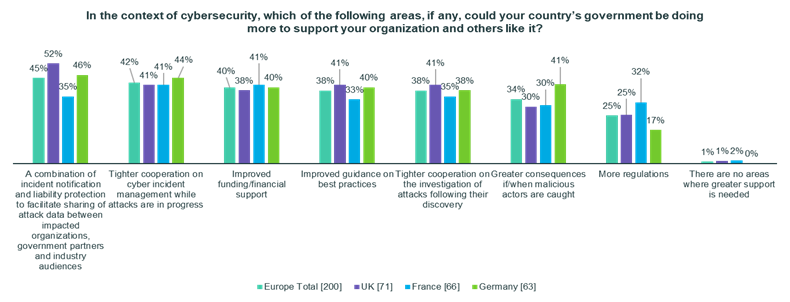
Forty-one percent of French respondents supported tighter cooperation on cyber incident management while attacks are in progress and improved financial support for their cybersecurity from the national government. Thirty-five percent supported tighter cooperation on the investigation of attacks following their discovery and a combination of incident notification and liability protection to facilitate sharing of cyber-attack data between impacted organizations, government partners and industry audiences. Around a third (33%) supported improved guidance on best practices, more government regulations (32%) and greater consequences when malicious actors are caught (30%).
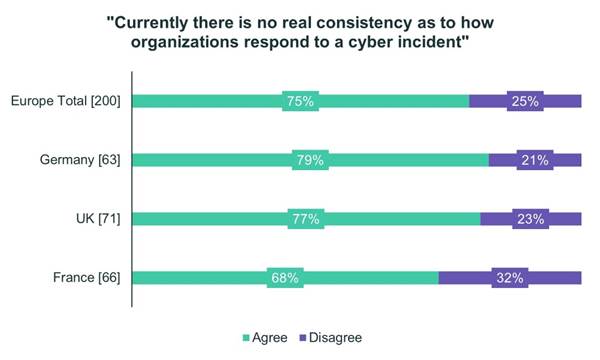
In the area of critical incident response best practices, there is evidence that governments could play a bigger role in providing standardized guidance on how organizations respond to cyber incidents. Seventy-nine percent of Germans, 77% of British respondents and 68% percent of the French agree there currently is no real consistency as to how organizations respond in these circumstances.
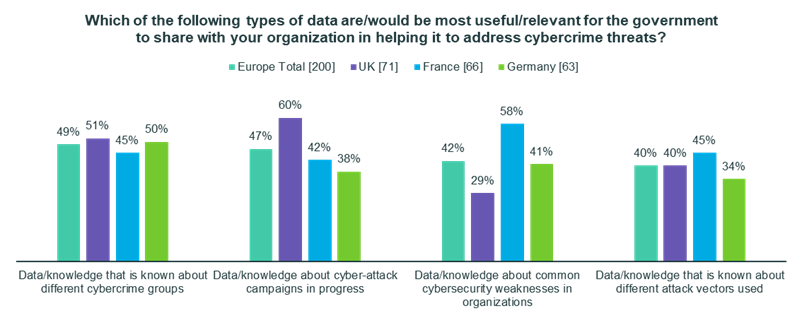
In terms of types of data that would be most useful for their government to share with their organization to help address cybercrime threats, British respondents said the quality of data being shared and the speed of data being shared were the areas that needed improvement most. Nearly two thirds (60%) appeared to value data about common cyber-attack campaigns in progress above other data. Fifty-one percent valued data on particular cybercrime groups, 40% valued data on known attack vectors and only 29% valued data on common cybersecurity vulnerabilities in organizations.
French respondents valued quality of data share (45%), ease of accessing data (45%) and relevance of data (41%) fairly evenly. Fifty-eight percent say that data on common cybersecurity vulnerabilities in organizations would be preferred above other data types. Forty-five percent valued data on known attack vectors and cybercrime groups, and slightly less (42%) valued data cyber-attack campaigns in progress.
German respondents ranked the ease of accessing data significantly ahead of the other concerns. As many as half prioritized data on particular cybercrime groups above other data types. Forty-one percent valued data on common cybersecurity vulnerabilities in organizations, followed by data on cyber-attacks in progress (38%) and data on different attack vectors (34%).
Finally, 76% of German respondents, 73% of British respondents and 68% of French respondents agree that there are gaps between regulators’ hopes and aims and real-world realities, and that they are often misaligned.
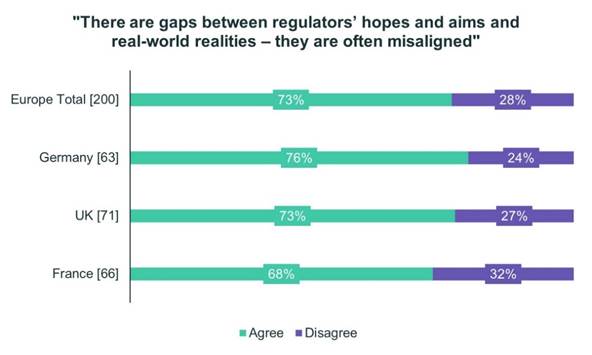
This final finding reminds us that the policies governments must formulate in cybersecurity must be realistic, make the right investments, define the proper public-private roles, set right priorities and establish the right objectives and timelines. Public and private partners must be fully aligned and working together. Only then can nations hope to succeed in better protecting themselves from cyber threats targeting their government agencies and critical infrastructure.
COVID-19 & Cybersecurity
After two years of the COVID-19 pandemic, respondents were asked how significant the challenge of protecting a remote workforce became in the overall cybersecurity posture of their organization. Ninety percent of Germans, 88% of French respondents and 87% of British respondents believe securing remote access to corporate facilities became somewhat more important to far more important as a result of the pandemic.
Respondents were also asked whether they believed the hybrid-remote work model of the pandemic would remain permanent, phase out entirely or whether it would be a case of seeing whether it works for organizations long-term.
Forty-five percent of British respondents said they believed the hybrid-remote work model would be a part of their organizations permanent work environment. Forty-five percent said they believed it would be a case of seeing whether the model continues to work long-term. Only 10% believe the pandemic hybrid-remote work models will phase out and workplaces will fully return to normal.
Fifty percent of French respondents said the hybrid-remote work model of the pandemic might phase out and that it would depend on how well it works for organizations long-term. Forty-seven percent believe the hybrid-remote work model will not phase out and will always be a part of their organizations’ working environments. Only 3% believe it will phase out completely and workplaces will fully return to normal.
Forty-eight percent of German respondents said the hybrid-remote work model will not phase out and will become permanent for their organizations. Forty-one percent believe it might phase out and will be a case of how well it works long-term. Only 11% believe it will phase out and that a full-time return to the office is on the horizon.
For more information, please see the full Trellix Cyber Readiness Report, the Asia Pacific Results Summary blog and other supporting blogs providing greater detail and insight on the report’s findings, here.
RECENT NEWS
-
May 19, 2026
Trellix Appoints Joe Chen as Chief Technology Officer
-
Apr 08, 2026
Trellix prevents enterprise data exposure in sanctioned and shadow AI
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.