Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more
Getting Roasted? Trellix Helix sees through AS-REP Attack
By Adithya Chandra and Maulik Maheta · March 17, 2026
Executive summary
Threat actors regularly target Active Directory environments, continuously refining their toolsets and modifying attack frameworks to bypass security controls. However, the foundational attack methodologies they use remain essentially unchanged. The Trellix research team recently examined GetNPUsers.py, a popular Impacket-based utility that adversaries leverage to execute AS-REP Roasting operations. Kerberos Ticket Granting Tickets (TGTs) are then extracted from domain accounts and configured without mandatory preauthentication.
Building upon our earlier research into AS-REP Roasting threats, this blog demonstrates how Trellix Helix's Advanced Correlation Engine (ACE) identifies AS-REP Roasting attacks based on behavioral patterns and technique fingerprints rather than tool-specific indicators. By examining a live attack scenario using GetNPUsers.py, we will illustrate how Helix's correlation capabilities leverage technique-centric detection logic, MITRE ATT&CK intelligence integration, and sophisticated event correlation to surface threats.
Understanding AS-REP roasting with GetNPUsers.py
This attack methodology exploits a specific Active Directory weakness where user accounts are configured to bypass Kerberos preauthentication requirements. The GetNPUsers.py script automates the exploitation process through several phases.
First, the script queries the domain to enumerate accounts where the "DONT_REQ_PREAUTH" attribute is enabled. Next, it generates Authentication Service Requests (AS-REQ) for these accounts. The domain controller responds with Authentication Service Replies (AS-REP) containing encrypted material derived from user passwords. Finally, adversaries extract this encrypted data for offline cryptanalytic attacks using platforms like Hashcat or John the Ripper, completely avoiding account lockout mechanisms and real-time detection systems.
Attack scenario: End-to-end AS-REP roasting execution
Figure 1 shows the complete AS-REP Roasting attack chain when executed through GetNPUsers.py. The diagram traces the adversary's path from initial account discovery through Kerberos ticket acquisition to offline password recovery operations. This workflow illustrates how a single Python script enables domain compromise without requiring any prior authentication credentials.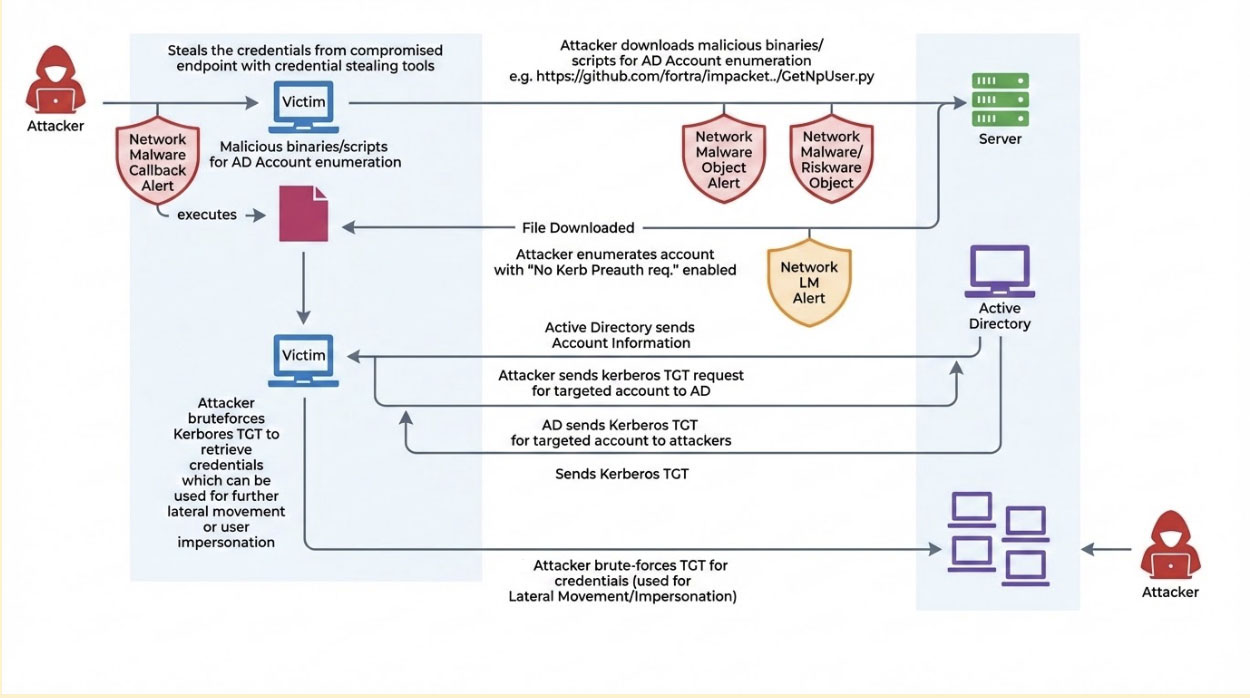
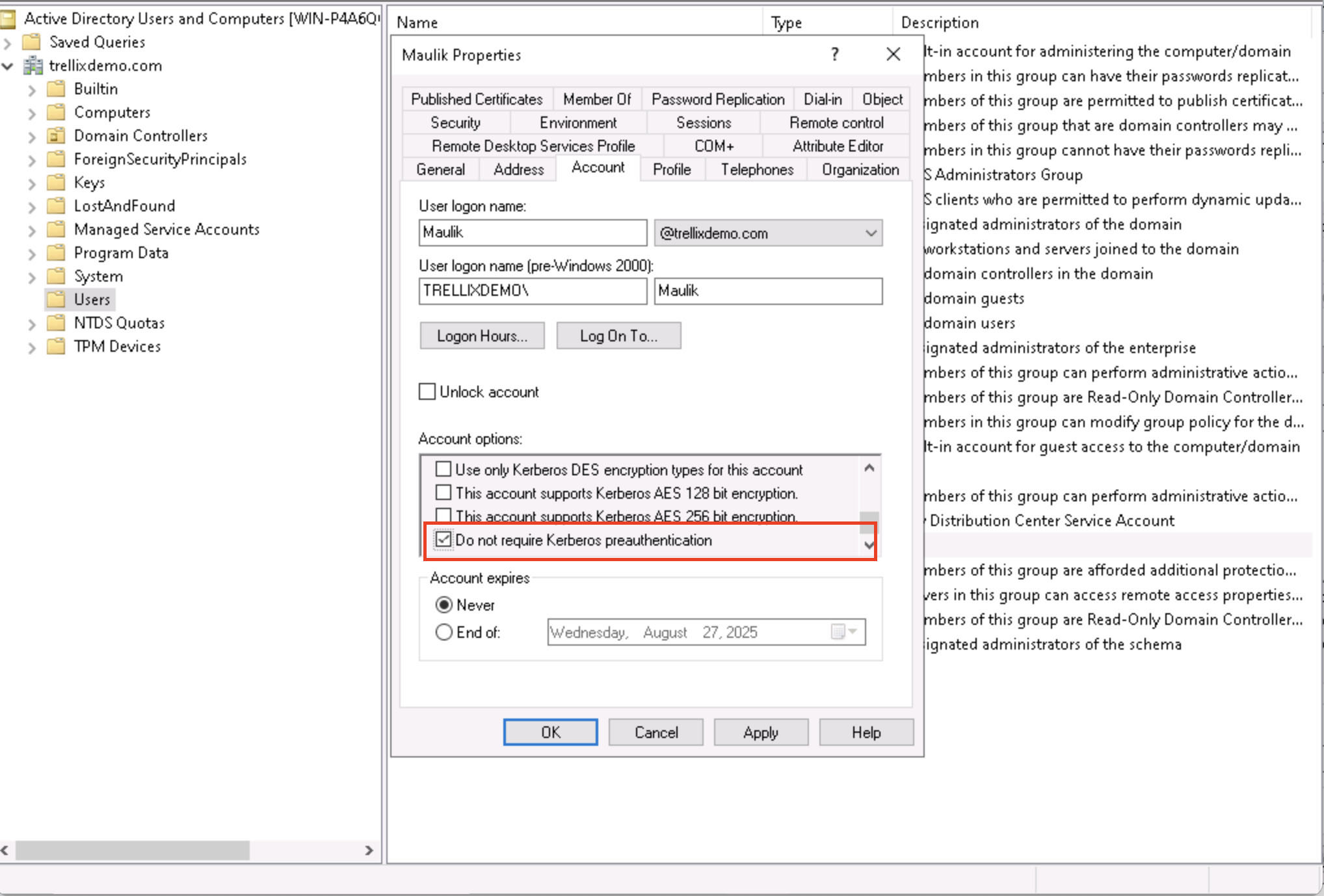
As you can see in the image above, accounts are configured in Active Directory with the "Do not require Kerberos preauthentication" setting. This configuration represents a critical security gap that allows the Key Distribution Center (KDC) to issue AS-REP responses containing password-encrypted data without identity verification. This opens the door for attackers to then perform offline cryptographic attacks.
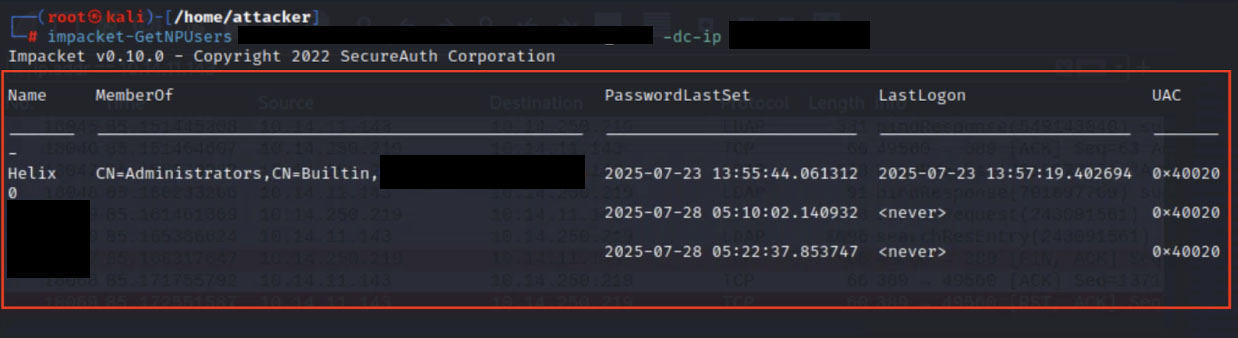
Phase 1: Identifying vulnerable domain accounts
In the image below, you can see the output that is generated by executing GetNPUsers.py against a target domain environment. The script's output reveals which user principals are susceptible to AS-REP roasting attacks. Adversaries leverage this intelligence to selectively target accounts, requesting Kerberos authentication responses that contain password-derived cryptographic material suitable for offline brute-force operations.
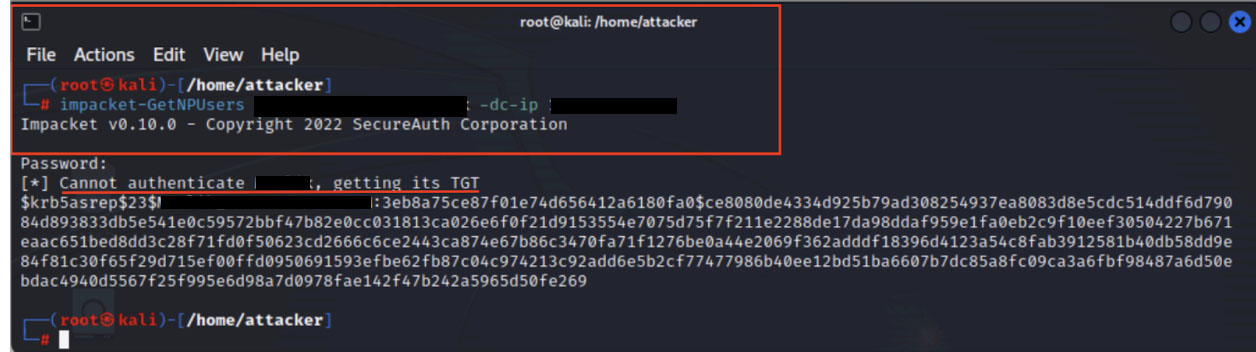
Phase 2: Kerberos TGT extraction and offline credential recovery
Following account enumeration, adversaries submit Kerberos AS-REQ packets to the domain controller for each vulnerable account. The domain controller returns AS-REP messages containing TGT data encrypted with the user's password hash. Adversaries then employ specialized password-cracking utilities, such as Hashcat, to perform offline brute-force attacks against this encrypted material. Successfully recovered credentials provide a foothold for subsequent lateral movement and privilege escalation activities.
AS-REQ packets are transmitted by the adversary to request tickets for the enumerated accounts. Because these specific accounts are configured to skip preauthentication validation, the resulting AS-REP messages carry TGT data encrypted using the account holder's password hash. This provides ideal material for offline cryptanalysis without triggering traditional authentication monitoring controls.
Detecting AS-REP roasting with Trellix Helix: Technique-centric threat identification
How can Trellix protect you from these forms of attack?
Trellix Helix employs its Advanced Correlation Engine (ACE) to identify and correlate AS-REP Roasting operations through behavioral analysis rather than tool-specific signatures. It recognizes suspicious Kerberos authentication patterns and enriches detections with contextual metadata, attack progression indicators, and tactical intelligence to enable rapid response.
Signature-independent detection framework
Trellix Helix's primary defensive advantage lies in its capability to identify AS-REP roasting operations independent of the specific attack tool or framework employed. Whether adversaries utilize GetNPUsers.py, Rubeus, Impacket libraries, or custom-developed scripts, Helix identifies the attack through multiple detection layers:
- Behavioral pattern analysis examining Kerberos authentication request characteristics Identification of TGT request patterns targeting accounts with preauthentication disabled Multi-source telemetry fusion combining endpoint detection data with network traffic analysis
- Identification of TGT request patterns targeting accounts with preauthentication disabled
- Multi-source telemetry fusion combining endpoint detection data with network traffic analysis
This methodology ensures sustained detection efficacy even as adversaries modify their toolchains or develop novel attack utilities, since the underlying technique’s behavior remains consistent and observable.
Consolidated alert intelligence
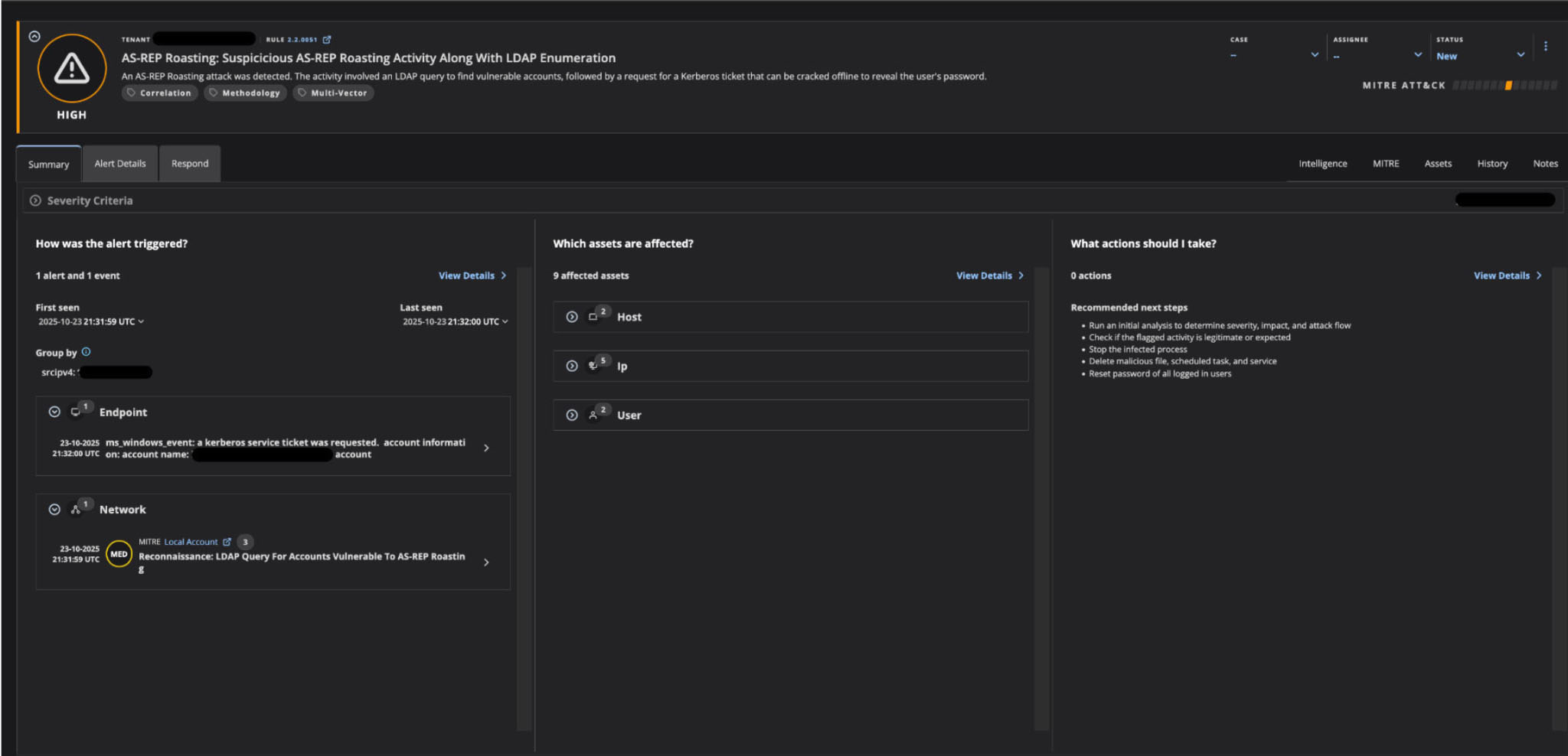
Trellix Helix also helps to simplify the story for incident responders through a consolidated view of alerts. The Advanced Correlation Engine synthesizes multiple detection signals into a unified summary with actionable intelligence. ACE correlates diverse indicators including:
- Preliminary reconnaissance operations such as LDAP queries searching for vulnerable account configurations
- Kerberos protocol anomalies observed in AS-REQ and AS-REP traffic flows
- Endpoint security telemetry from compromised or targeted systems
- Network behavioral deviations from established authentication baselines
In this case, the alert receives a HIGH severity classification and delivers immediate situational awareness. Helix details the attack scope, compromised assets, adversary source addresses, and targeted users. This sophisticated correlation capability transforms disparate security events into a threat narrative that accelerates investigation and response activities.
Temporal attack flow reconstruction
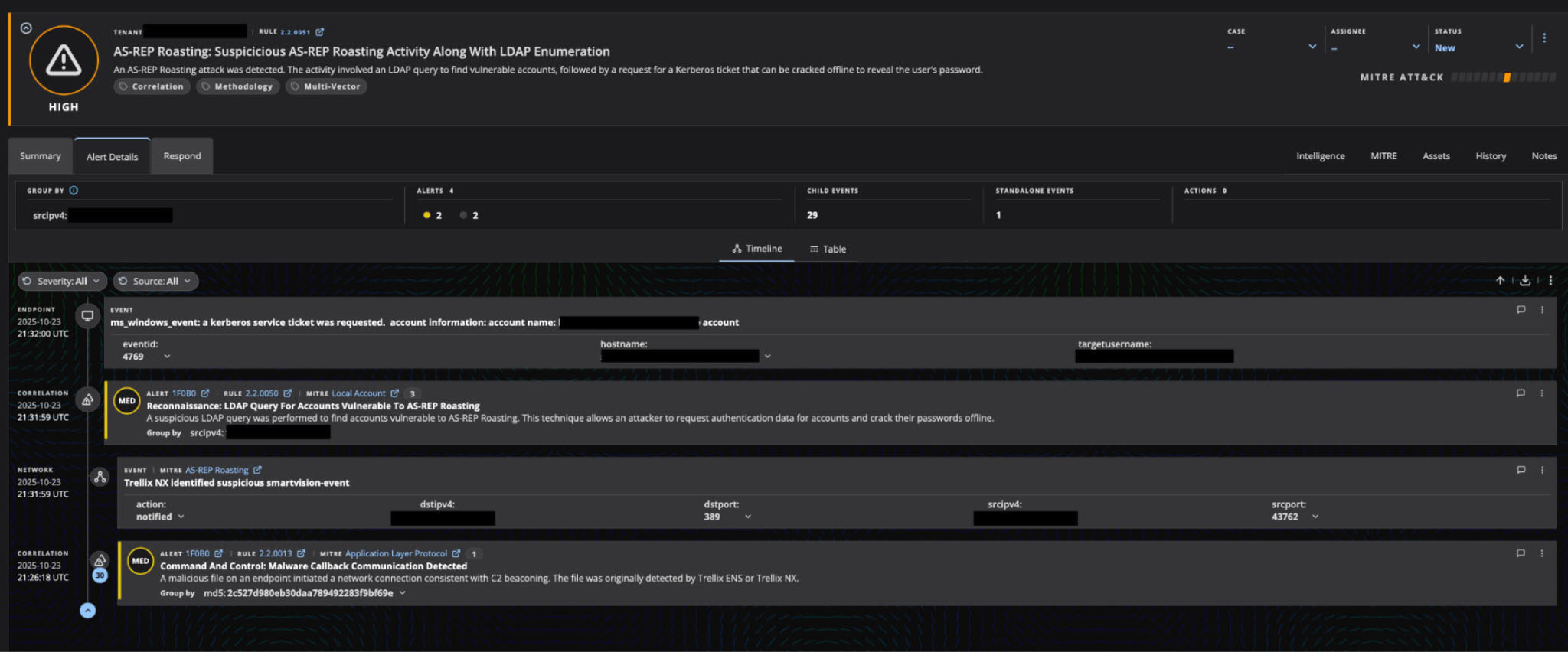
Helix provides a timeline of alerts chronologically sequencing attack events, reconstructing the complete kill chain of the AS-REP roasting operation. This temporal perspective is essential for understanding adversary progression across multiple security data sources. The timeline reveals:
- Initial LDAP enumeration operations identifying misconfigured accounts via network telemetry data
- Subsequent waves of Kerberos AS-REQ transmissions targeting discovered vulnerabilities and corresponding AS-REP responses delivering encrypted password hash material
This empowers security analysts to reconstruct adversary tradecraft from initial reconnaissance through active exploitation, maintaining detection visibility regardless of which specific tools facilitated the attack.
Response and remediation guidance
Upon confirming AS-REP roasting activity through Trellix Helix detections, security teams should execute the following response procedures:
- Conduct an immediate triage assessment, evaluating severity, business impact, and attack progression stage
- Validate whether the detected activity represents authorized security testing or adversary operations
- Implement network isolation for affected systems to contain potential lateral movement
- Terminate suspicious processes and services associated with attack indicators
- Remove malicious artifacts, including files, persistence mechanisms, and scheduled tasks
- Enforce mandatory password resets for all compromised or potentially exposed user accounts
- Audit and remediate Kerberos preauthentication configuration across all domain accounts
- Conduct a comprehensive review of accounts configured with the "DONT_REQ_PREAUTH" attribute
- Proactively hunt for threats using ACE correlation rules to identify similar attack patterns
- Review privileged access controls and service account security configurations
Multi-dimensional threat context and asset impact analysis
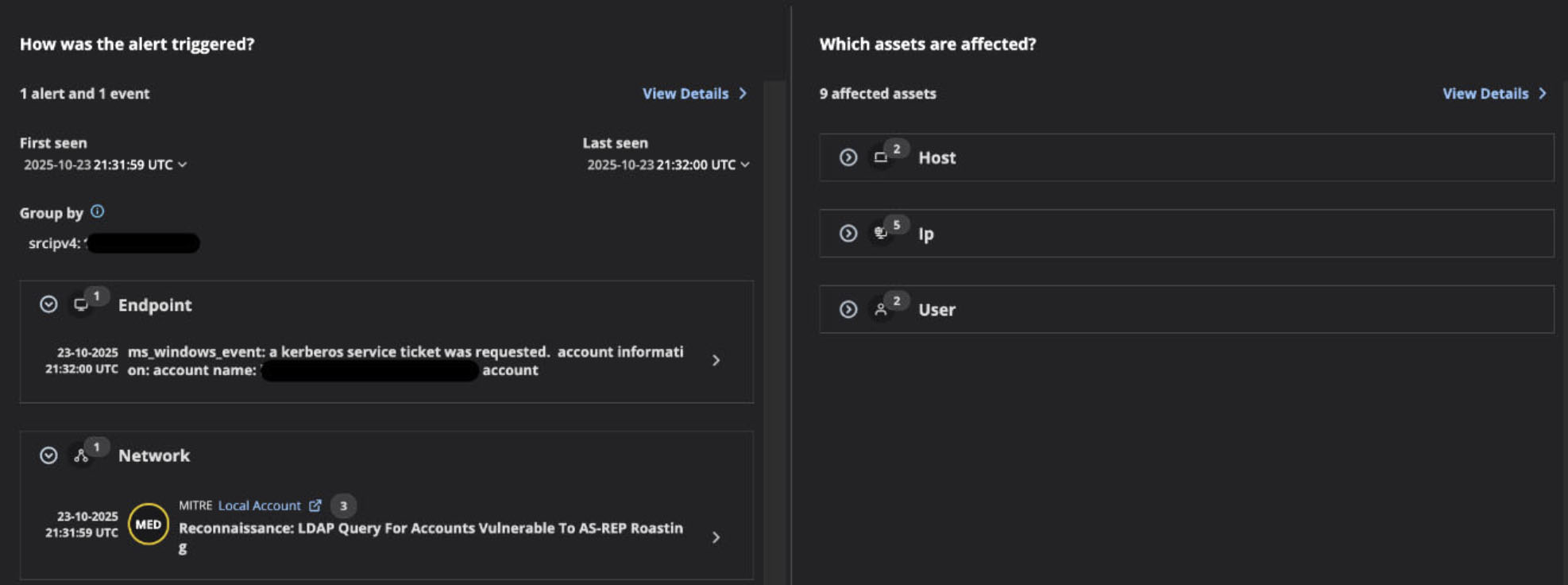
The alert visualization is divided into two critical intelligence panels:
The left panel, "How was the alert triggered?", reveals the multi-source detection that identified the AS-REP roasting activity. This view shows the correlation of alert and event, with detection spanning two distinct telemetry sources:
- Endpoint Detection: Captured through Windows event monitoring, specifically identifying "a Kerberos service ticket was requested" along with detailed account information. This endpoint-level visibility provides insight into the Kerberos AS-REP response being delivered to the adversary.
- Network Detection: Flagged through Trellix network telemetry with a MITRE-tagged alert for "Reconnaissance: LDAP Query For Accounts Vulnerable To AS-REP Roasting." This network-level detection identifies the preliminary reconnaissance phase, during which the adversary enumerated accounts with preauthentication disabled.
The right panel, "Which assets are affected?", delivers immediate situational awareness regarding the attack's footprint across the environment. This consolidated asset view shows 9 affected assets categorized across three dimensions:
- 2 Host assets - Endpoints involved in the attack activity
- 2 User accounts - Identity principals targeted or compromised during the operation
- 5 IP addresses - Network infrastructure elements connected to the attack chain
This dual-panel correlation interface exemplifies Trellix Helix's capability to synthesize endpoint behavior, network reconnaissance patterns, and identity targeting into a single actionable alert. Security analysts gain an immediate understanding of both the attack methodology (how it was detected across multiple telemetry sources) and the business impact (which critical assets are affected). This enables rapid containment decisions, prioritizes investigation workflows, and informs escalation procedures based on the criticality of affected hosts, networks, and user principals.
Advanced correlation engine: Advantages for tool-independent detection
Trellix Helix's Advanced Correlation Engine delivers multiple strategic advantages over specific attack tools:
- Technique-centric pattern recognition: ACE identifies the behavioral characteristics inherent to AS-REP Roasting methodology regardless of the implementation tool. It focuses on immutable technique properties rather than mutable tool artifacts.
- Cross-platform telemetry fusion: ACE brings endpoint detection data, network traffic intelligence, and identity authentication logs together. This allows it to construct complete attack narratives instead of individual tool-based detections.
- False positive suppression: Through multi-indicator correlation across heterogeneous data sources, ACE differentiates legitimate administrative operations from adversary activity. This helps analysts to stay focused on high-confidence threats.
- Immutable technique detection: Detection logic targets adversary objectives and methodologies (the "what" and "why") rather than implementation details (the "how"). This ensures detection resilience against tool modifications, obfuscation techniques, and novel attack variants.
Conclusion
This blog covers just one implementation vehicle for AS-REP roasting attacks. Despite the tool's apparent simplicity, it facilitates a sophisticated threat requiring swift action by analysts.
Trellix Helix maintains the level of visibility into AS-REP Roasting threats required to capture the full spectrum of attack tools and frameworks used by attackers. This technique-centric defensive approach is a foundational requirement for attacks designed to evade detection. As adversaries continue to evolve their tradecraft, develop novel attack utilities, and adapt existing frameworks, security platforms must focus on detecting the persistent techniques that underpin successful attacks. Trellix Helix's multi-layered correlation ensures that whether adversaries employ GetNPUsers.py, Rubeus, custom PowerShell implementations, or future attack frameworks yet to be developed, the underlying AS-REP Roasting technique remains consistently detectable and actionable for security operations teams.
To explore more about the Trellix Helix platform, take our product tour to see it in action or visit this page.
Discover the latest cybersecurity research from the Trellix Advanced Research Center: https://www.trellix.com/advanced-research-center/
RECENT NEWS
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
-
Dec 11, 2025
Trellix Finds 97% of CISOs Agree Hybrid Infrastructure Provides Greater Resilience
-
Oct 29, 2025
Trellix Announces No-Code Security Workflows for Faster Investigation and Response
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.
