Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more
The Ghost SPN Attack: Catching Stealthy Kerberoasting Before It's Too Late Using Trellix NDR
By Maulik Maheta and Henry Bernabe · March 23, 2026
Executive summary
As organizations adopt an identity-first security posture, adversaries are increasingly exploiting the "identity fabric” using sophisticated, non-persistent techniques such as targeted Kerberoasting. This tactical evolution entails transient manipulation of service principal name (SPN) attributes to aid credential extraction, effectively avoiding traditional, volume-based detection models that lack cross-domain telemetry.
This study breaks down the “ghost SPN” vector, which uses delegated administrative permissions to create temporary exposure windows. Attackers avoid static monitoring by scrubbing identity artifacts immediately after extraction, allowing them to dwell undetected within infrastructure. This demonstrates a critical visibility gap in legacy security operations center (SOC) stacks that rely on disparate log analysis.
We look at how Trellix Network Detection and Response (NDR) mitigates this risk using identity-aware behavioral correlation. Trellix provides the necessary “adversarial path” visibility for modern exposure management by combining Active Directory attribute changes with real-time network authentication metadata.
As threat actors shift from software vulnerabilities to living-off-the-land (LotL) permission abuse, defenders must transition from reactive signature matching to continuous monitoring of identity-to-network relationships. This blog provides a blueprint for operationalizing detection against the next generation of hidden identity exploitation.
Kerberoasting: Setting the SPN out-of-band and covering their tracks
Kerberoasting is a post-exploitation technique in Active Directory environments that targets accounts with SPNs. When a ticket granting service (TGS) ticket is requested for an SPN, it is encrypted with the target account secret. Attackers can extract this ticket and crack offline passwords, potentially recovering plaintext credentials.
Historically, adversaries have focused on enumerating existing service accounts. However, a more stealthy variant takes a different approach: rather than targeting predefined service principals, attackers temporarily convert a normal user account into one.
Setting the SPN out-of-band
"Setting the SPN out-of-band" means assigning an SPN to an account outside of normal service configuration workflows. An attacker can modify another user's SPN attribute by abusing delegated directory permissions, such as object-level write access.
When the SPN is added, the Kerberos key distribution center (KDC) recognizes the account as a valid service principal and issues a TGS ticket when requested. From a protocol standpoint, nothing appears abnormal. The attacker creates their own Kerberoasting target without affecting known service accounts or triggering common enumeration-based detections.
This greatly reduces noise and evades many traditional monitoring detection capabilities.
Extract, crack, and clean up
After obtaining the TGS ticket, the attacker begins offline cracking. Because this process takes place outside of the environment, it results in no additional authentication failures or suspicious login attempts.
The defining stealth element is as follows: the SPN is removed by clearing the attribute, and the account gets restored to its original state, which hides any persistent indicators of abuse. The brief SPN assignment may go unnoticed if directory changes are not audited on a regular basis and linked to Kerberos activity.
Why this matters
This variant calls into question detection models that consider only known service accounts or large volumes of ticket requests. It is possible that the targeted account has never been a service account. The SPN may exist for only a short time. When considered separately, the activity may appear administratively legitimate.
To detect this technique, identity manipulation must be correlated with authentication behavior. Behavioral analysis solutions, such as Trellix Network Detection and Response (NDR), bridge this gap by detecting unusual SPN assignments and linking them to suspect Kerberos activity.
As adversaries increasingly exploit legitimate permissions rather than software flaws, defenders must pay attention not only to access attempts, but also to how identity attributes are being modified, particularly when those changes are intended to disappear. Now we discuss in detail the attack scenario and the Trellix NDR detection.
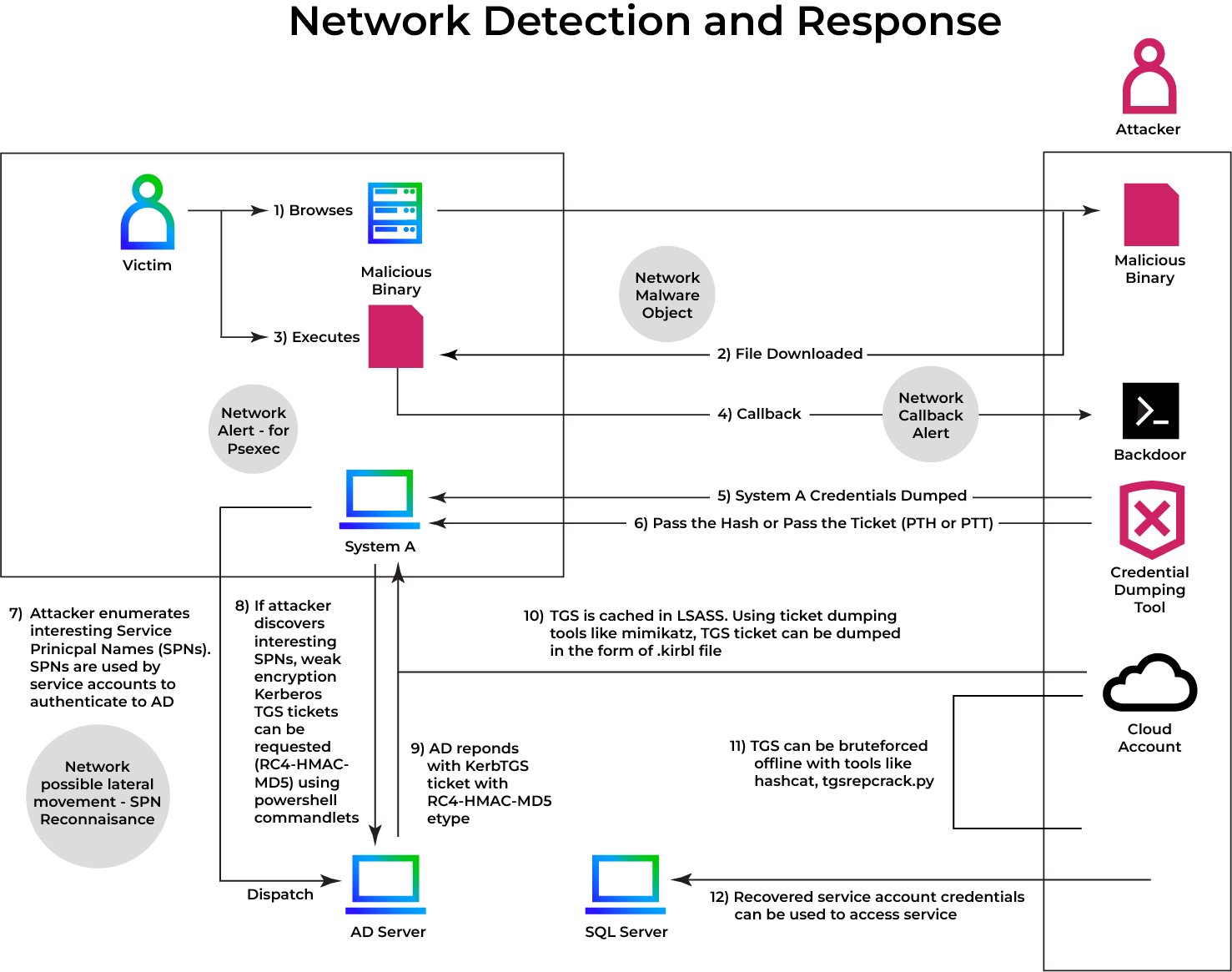
Figure 1 demonstrates the technique's stealth and efficiency, as attackers leave minimal log footprints while leveraging legitimate mechanisms.
In Figure 2, the attacker discovers that the compromised account has GenericAll access to another account (Trellix). This permission set, which is part of AD's access control model, provides complete control over the target object, including the ability to modify sensitive attributes like SPNs. Finding these connections is a typical post-compromise action and can lead to additional abuse, particularly in situations involving Kerberoasting, where the crucial piece is setting an SPN.
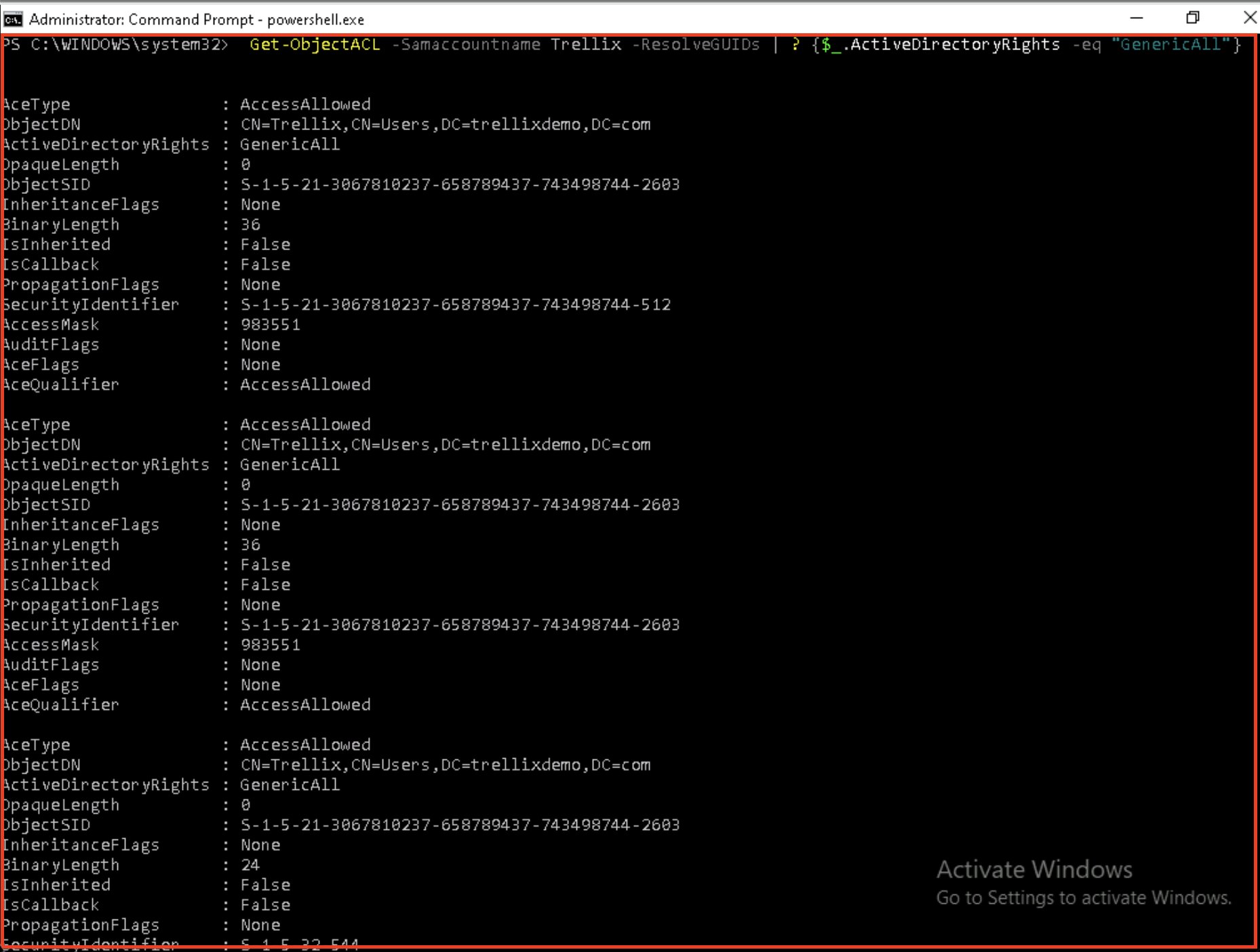
Figure 3 shows the attacker using a command to manually assign an SPN (e.g., http/webapp) to the targeted user account. This is achieved because the attacker has the requisite write access to the account as a result of the previously discovered GenericAll control. The attacker fools the Kerberos key distribution center (KDC) into producing a TGS ticket, which is generally reserved for valid service accounts, by assigning a fake or arbitrary SPN. This step effectively converts a typical user account into a lured target for Kerberoasting.
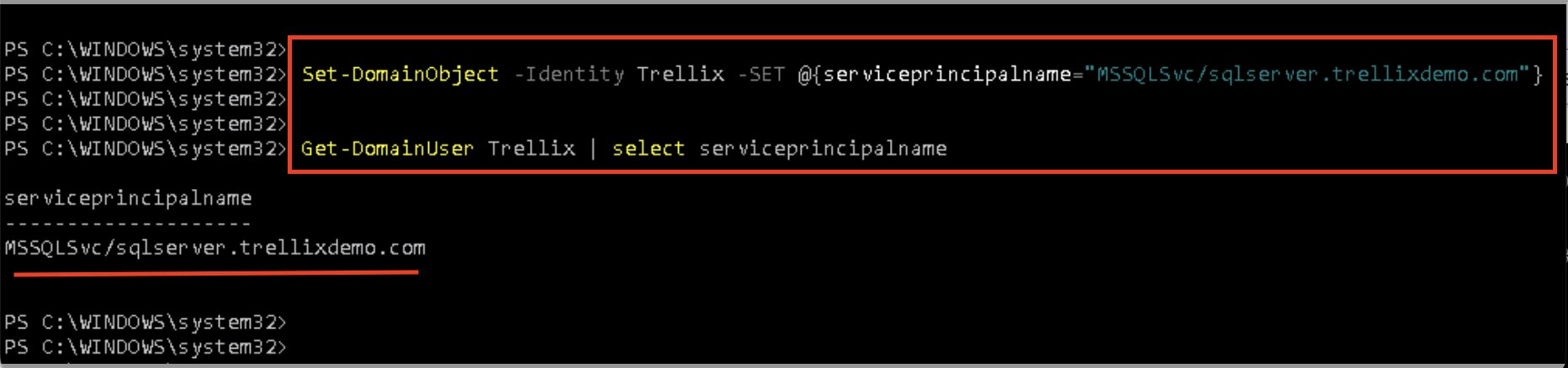
Figure 4 shows how the attacker confirms that the SPN was appropriately applied to the target account. This assures that the Kerberos service will now recognize this account as a valid service principal. After successful verification, the attacker can request a TGS ticket for the newly issued SPN, which will be encrypted with the NTLM hash of the target account's password. Offline cracking of this hash might potentially expose plaintext credentials.
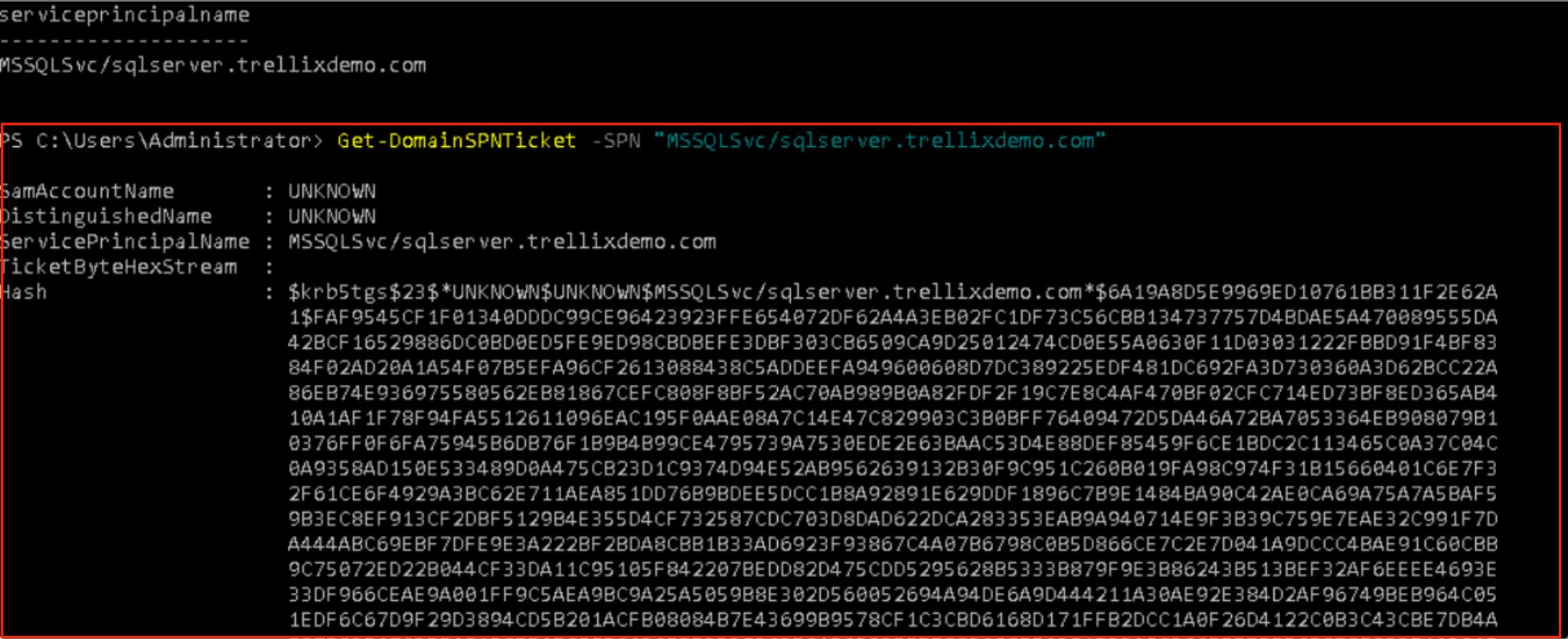
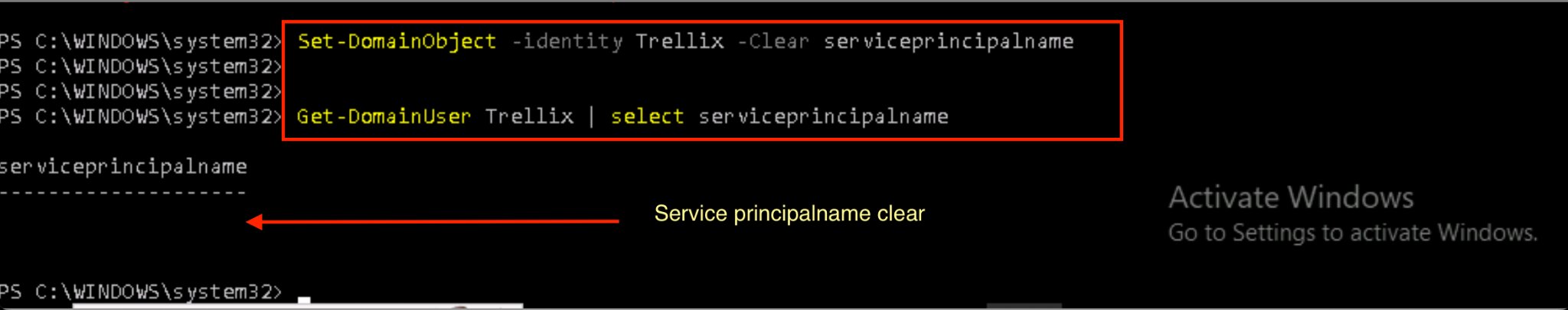
Figure 5 displays the critical cleanup phase of the attack. After obtaining the TGS ticket, the attacker deletes the SPN from the victim account using the same access credentials that were previously exploited. This intentional deletion serves to limit detection opportunities and forensic evidence. Without the SPN in the directory, defenders may be unable to link the TGS request to malicious behavior, especially if logs are minimal or not maintained. This anti-forensic strategy makes the attack more difficult to attribute and substantially stealthier.
Detection: Trellix NDR
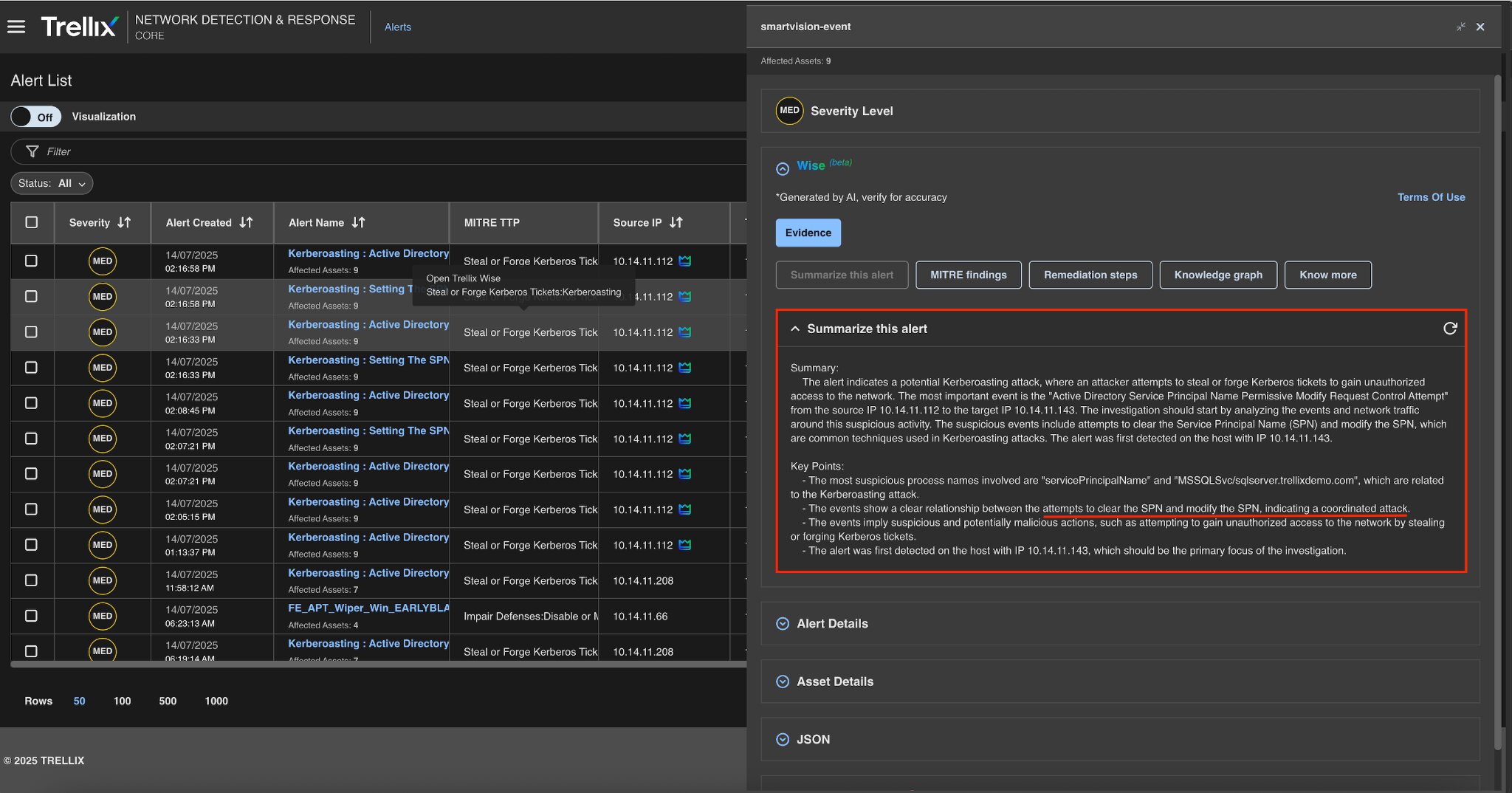
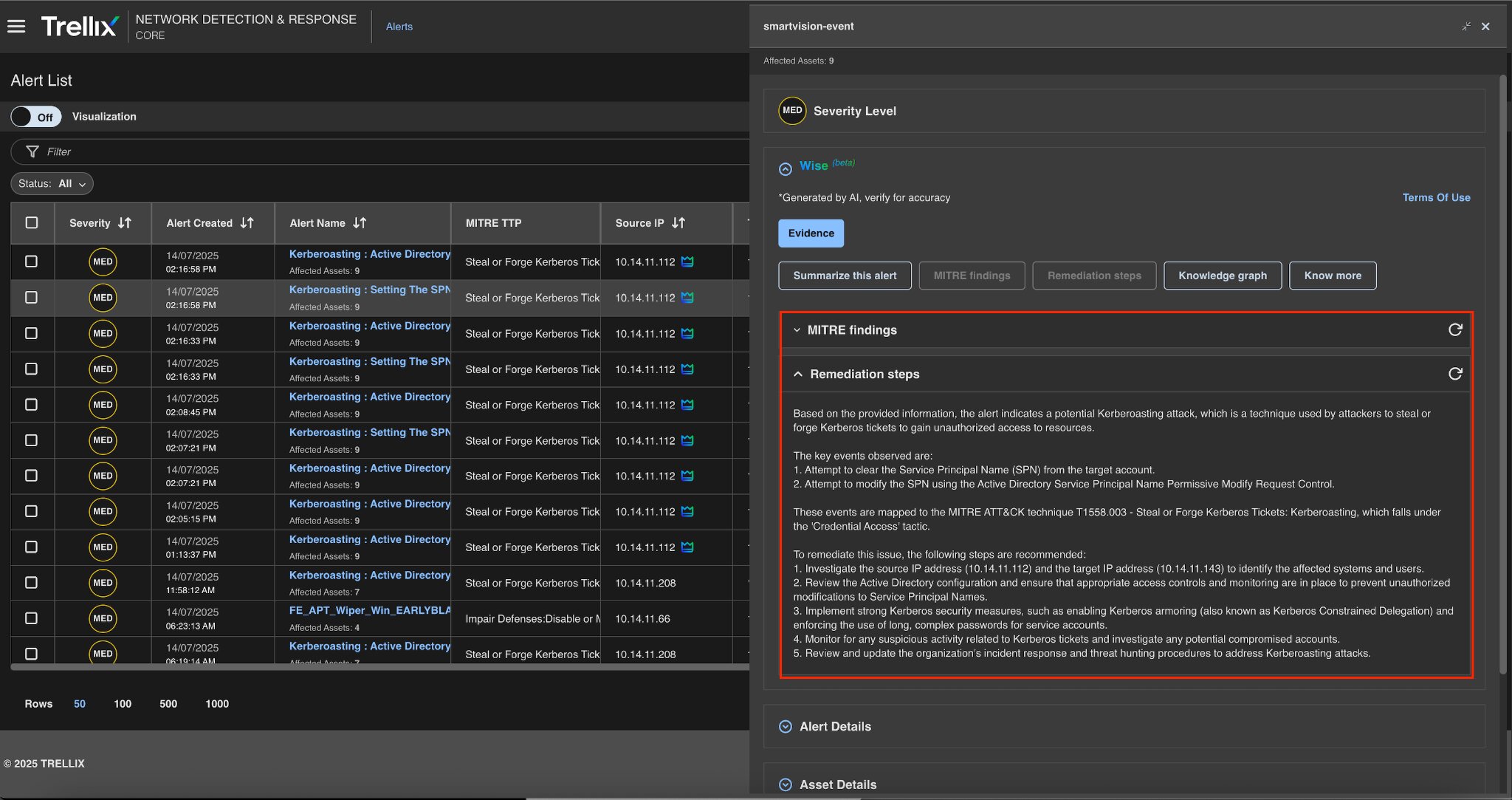
Trellix NDR utilizes Trellix Wise, an AI-powered investigation assistant, to enhance threat detection and response capabilities. Trellix Wise automates many aspects of alert investigation, reducing false positives and accelerating the time to resolution for security teams. This integration allows organizations to gain greater threat detection accuracy, automate complex tasks, and focus on strategic defense.
Trellix Wise can provide a user with comprehensive details such as additional information on the alert, remediation steps, MITRE information, etc.
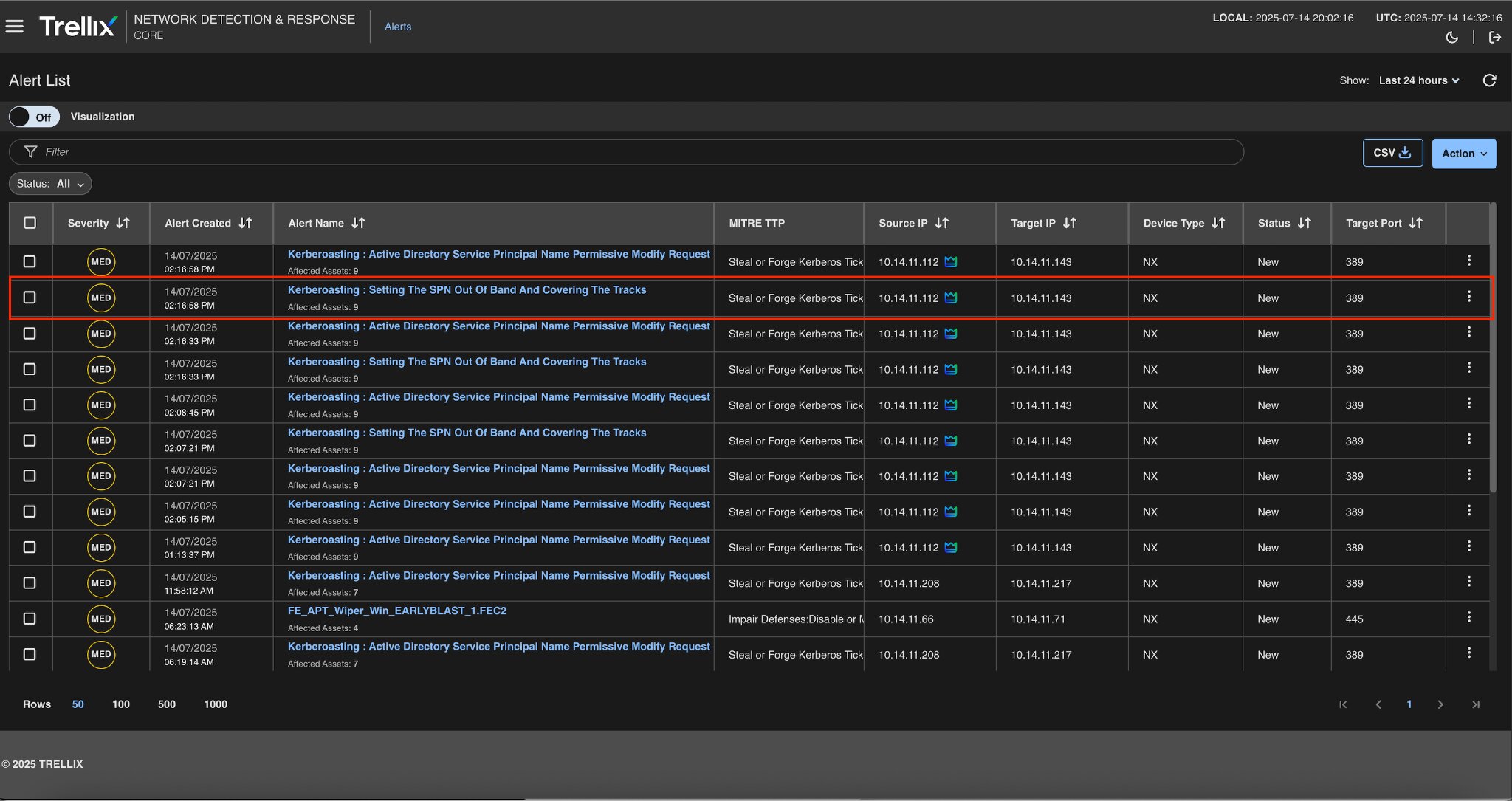
Figure 6 displays a near real-time alert from Trellix Network Detection and Response (NDR), triggered by suspicious SPN activity. The system identifies the unusual behavior of SPN assignment by a user that typically doesn’t manage service accounts. Since legitimate SPN modifications are relatively rare and mostly performed by specific admin accounts or scripts, this deviation is a strong signal for compromise.
Alert summary
Figure 7 shows a full description of Trellix NDR's alert. The metadata includes the IP address, modified object (user account with associated SPN), and activity type.
The detection signature or behavioral rule is triggered. This level of detail helps analysts during triage by allowing them to immediately understand the context and extent of the event.
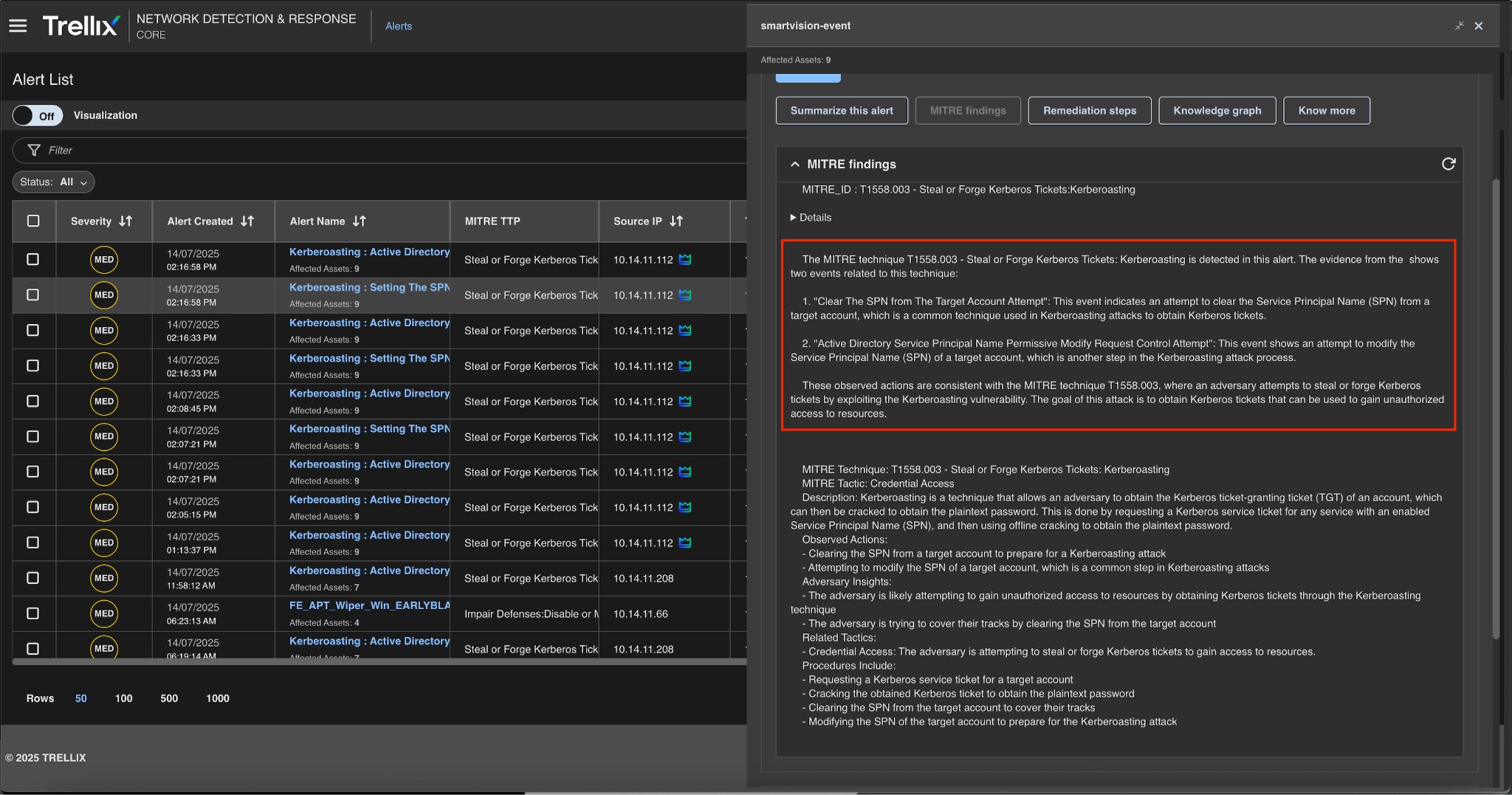
MITRE findings
This mapping has two purposes. First, it helps to connect detection with defined threat models for reporting and response. Second, it helps security teams understand how this activity ties with larger adversary objectives such as lateral movement or credential theft. The mapping enhances analyst visibility and facilitates purple team exercises to test detection gaps.
Remediation action
Figure 9 shows Trellix's remediation steps for addressing SPN abuse. These consist of quick elimination of unapproved SPNs and overpermissive ACLs (such as GenericAll), which should be reviewed and restricted. The target account's password was reset. Here the guidance ensures that defenders not only put an end to current abuse but also harden the environment to prevent it from happening again. The remediation steps highlight the significance of AD hygiene and proactive access control reviews.
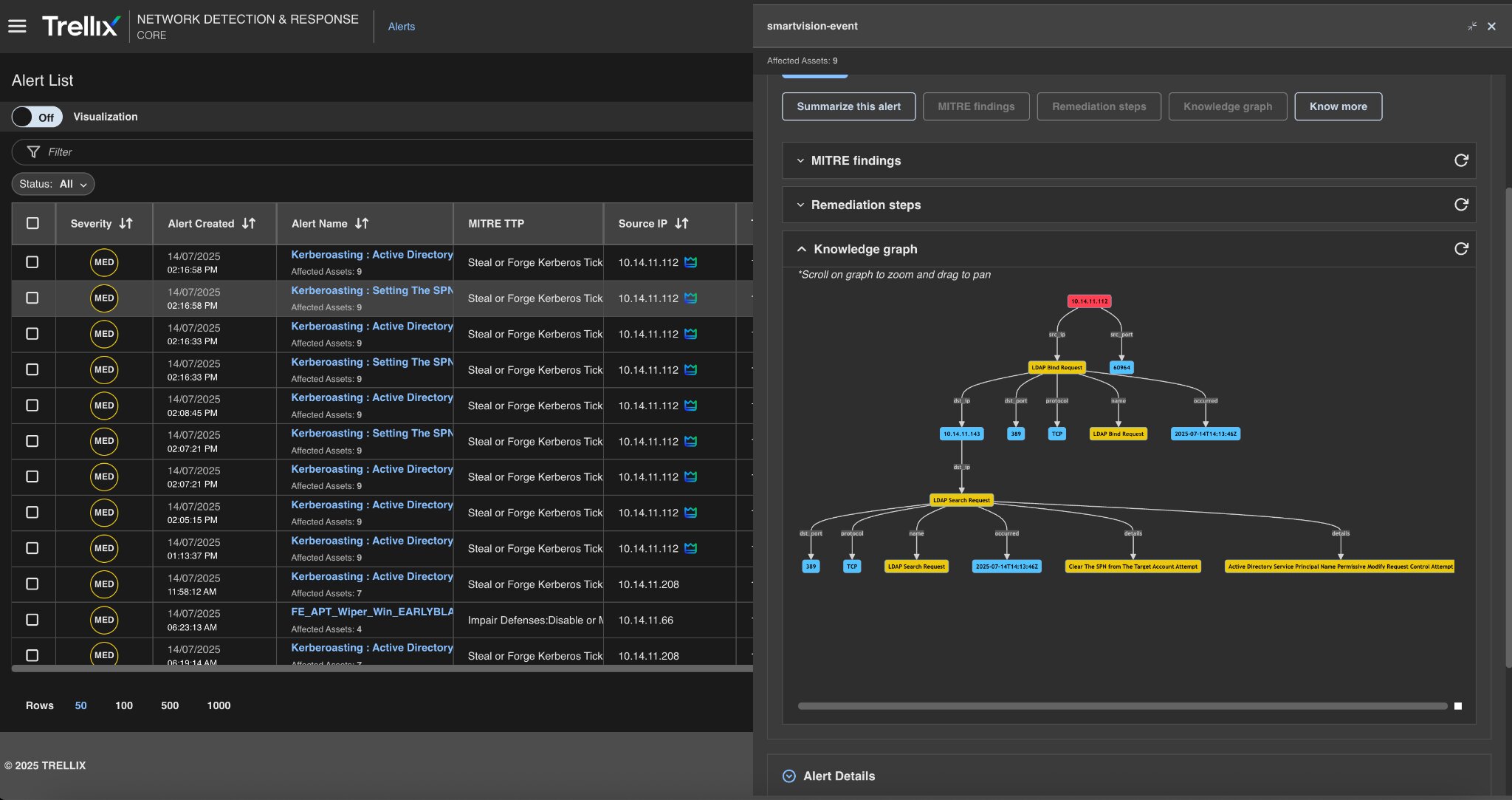
Knowledge graph
Figure 10 shows the Trellix Knowledge Graph, a powerful visualization tool for connecting entities like users, assets, attack techniques, and detection signals.
Conclusion
This blog discusses a stealthier variant of the Kerberoasting attack in which adversaries use directory-level write permissions to manually set SPNs on user accounts, circumventing traditional enumeration and targeting methods. Attackers reduce their footprint in logs and avoid standard detection techniques by operating out-of-band, explicitly assigning, abusing, and then erasing SPNs, making the attack difficult to detect in mature environments.
Such tactics emphasize the importance of defenders going beyond basic SPN monitoring and instead focusing on behavioral anomalies, privilege abuse, and unusual account modifications. Trellix Network Detection and Response (NDR) helps identify these nuanced threats by correlating events.
To learn more about Trellix NDR, take our product tour to see it in action or read more by visiting this page.
Discover the latest cybersecurity research from the Trellix Advanced Research Center: https://www.trellix.com/advanced-research-center/
RECENT NEWS
-
Apr 08, 2026
Trellix prevents enterprise data exposure in sanctioned and shadow AI
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
-
Dec 11, 2025
Trellix Finds 97% of CISOs Agree Hybrid Infrastructure Provides Greater Resilience
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.
