Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more

Blogs | Perspectives
Preparing for the AI Tidal Wave: Securing Critical Enterprise Data
By Laurie Robb · April 8, 2026
The AI data risk tipping point has arrived. Learn how to transform AI from a potential data risk into a secure productivity engine./p>
RECENT BLOG POSTS
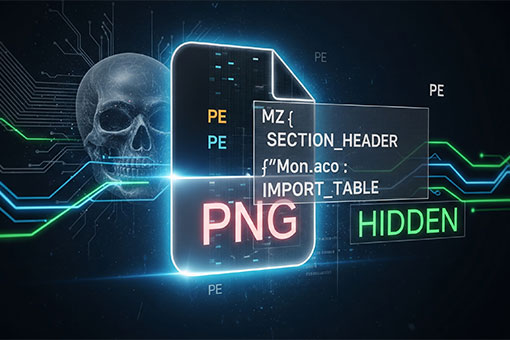
PureRAT: A Multi-Stage, Fileless RAT Utilizing Image Steganography and Process Hollowing
By Prashanth A N and Mallikarjun Wali · April 20, 2026
PureRAT is an advanced Remote Access Trojan (RAT) characterized by its complex infection stages. The intrusion sequence is initiated by a malicious .LNK file that triggers a concealed PowerShell command to retrieve a heavily obfuscated VBS loader.

DCSync Detection Without Signatures: Trellix NDR and the Power of Technique-Based Defense
By Maulik Maheta and Chao Sun · April 14, 2026
This blog explores how Trellix Network Detection and Response (NDR) moves beyond static signatures to detect these attempts by focusing on the underlying behavioral patterns of the attack technique itself.

A CISO’s Compliance Playbook: Navigating the Complexity of NIS2, DORA, and CRA
By Chris Hutchins · April 13, 2026
Guide for CISOs: Master the EU's NIS2, DORA, and CRA cyber regulations to boost cyber resilience and enforce continuous risk management.

How A Simple Misconfiguration Can Fuel Offline Attacker Tools
By Grant McDonald · April 9, 2026
In this blog, our researchers describe how a single script allows a compromise without authentication credentials.

Preparing for the AI Tidal Wave: Securing Critical Enterprise Data
By Laurie Robb · April 8, 2026
The AI data risk tipping point has arrived. Learn how to transform AI from a potential data risk into a secure productivity engine.
RECENT PRESS RELEASES
-
May 19, 2026
Trellix Appoints Joe Chen as Chief Technology Officer
-
Apr 08, 2026
Trellix prevents enterprise data exposure in sanctioned and shadow AI
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
More from Trellix
The
CyberThreat Report
October 2025
Trellix Portfolio
Explore our security products
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.