Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more
DCSync Detection Without Signatures: Trellix NDR and the Power of Technique-Based Defense
By Maulik Maheta and Chao Sun · April 14, 2026
Executive summary
A DCSync attack is one of the most formidable techniques an adversary can deploy after gaining a foothold in an Active Directory (AD) environment. Unlike traditional credential dumping from local systems, DCSync allows an attacker to impersonate a Domain Controller. By leveraging the Directory Replication Service Remote Protocol (MS-DRSR), they can silently pull sensitive data directly from the domain.
The ultimate prize of this technique is the master key of the Active Directory server - the krbtgt hash. Once captured, it grants the attacker golden ticket capabilities, providing near-permanent, absolute control over the entire domain. While often associated with tools like Mimikatz, attackers can execute DCSync via various platforms, including Meterpreter shells and custom scripts.
This blog explores how Trellix Network Detection and Response (NDR) moves beyond static signatures to detect these attempts by focusing on the attack technique’s underlying behavioral patterns.
How a DCSync attack unfolds step by step
Figure 1 shows the DCSync attack path in detail, from the initial compromise to total domain persistence. It demonstrates how an adversary can transform a single compromised system into a full domain hijack by silently extracting credential data from Active Directory via replication protocols. Figure 1 also shows key phases, including initial malware execution, credential dumping, the critical DCSync attack to retrieve the KRBTGT hash, and, finally, the forging of a Golden Ticket to gain unauthorized access to the AD Server. Golden ticket attacks were already covered in our previously published blog.
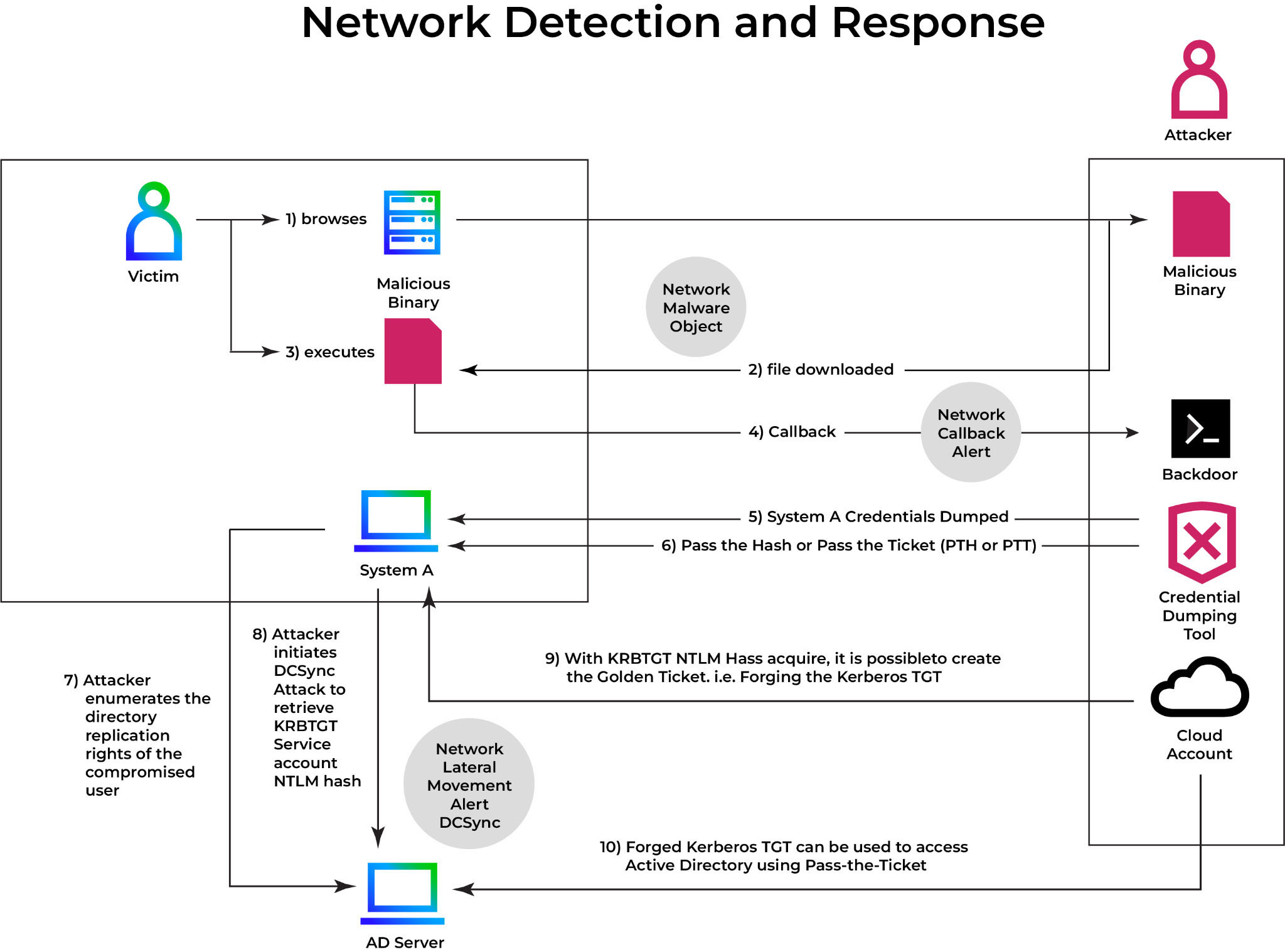
Figure 2 shows the attack's core being executed from within a Metasploit meterpreter shell. After gaining access to a machine with domain admin privileges, the attacker uses the dcsync_ntlm command to target the krbtgt account. The output shows that the account's NTLM hash was successfully extracted. This demonstrates that the DCSync technique does not rely on a single tool, such as Mimikatz, and can be initiated from a variety of attacker frameworks.
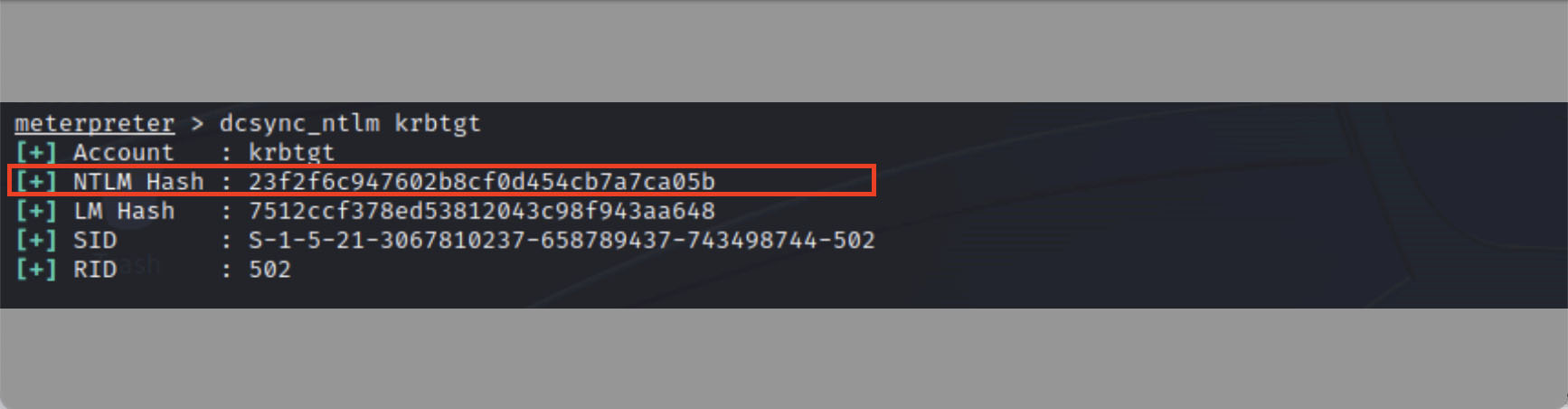
Figure 3 provides a more detailed view of the credential-harvesting process. The attacker uses the dcsync command in Meterpreter to impersonate a domain controller and request user credentials. The terminal output shows a large amount of sensitive data being replicated from the domain controller, including the target username, SID, and critical NTLM hash. This is the raw data an attacker requires to escalate privileges and forge Kerberos tickets.
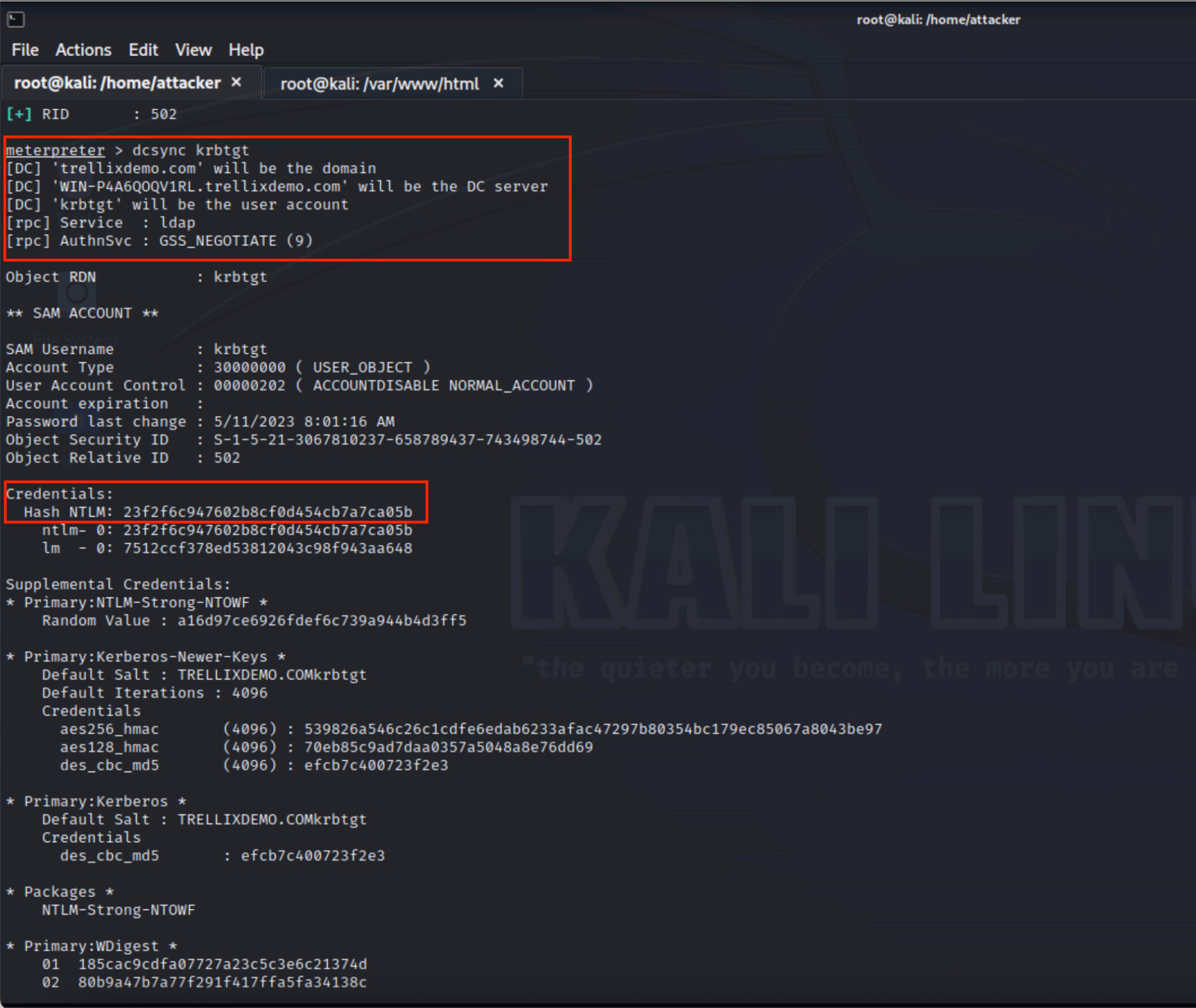
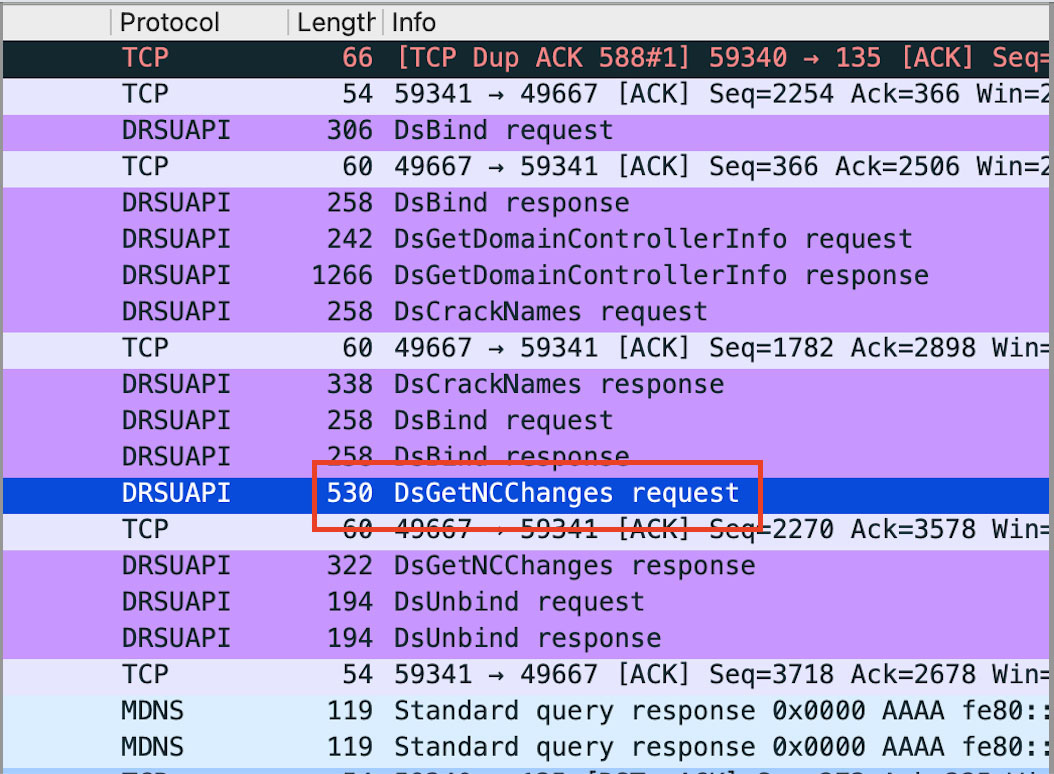
Figure 4 shows network-level evidence of the DCSync attack in progress. The Wireshark capture shows the DsGetNCChanges request, which is a valid function of the Directory Replication Service Remote Protocol (MS-DRSR). In this case, however, the request is malicious if it comes from a non-domain controller. It is the technical fingerprint of an unauthorized system impersonating a domain controller in order to trick the legitimate DC into synchronizing sensitive credential data. This is the specific behavior that technique-based detection systems seek.
Detection - Trellix Network Detection and Response (NDR)
Trellix NDR utilizes Trellix Wise, which acts as an AI-powered investigation assistant, to enhance threat detection and response capabilities. Trellix Wise automates many aspects of alert investigation, reducing false positives and accelerating the time to resolution for security teams. Wise allows organizations to gain greater threat detection accuracy, automate complex tasks, and focus on strategic defense.
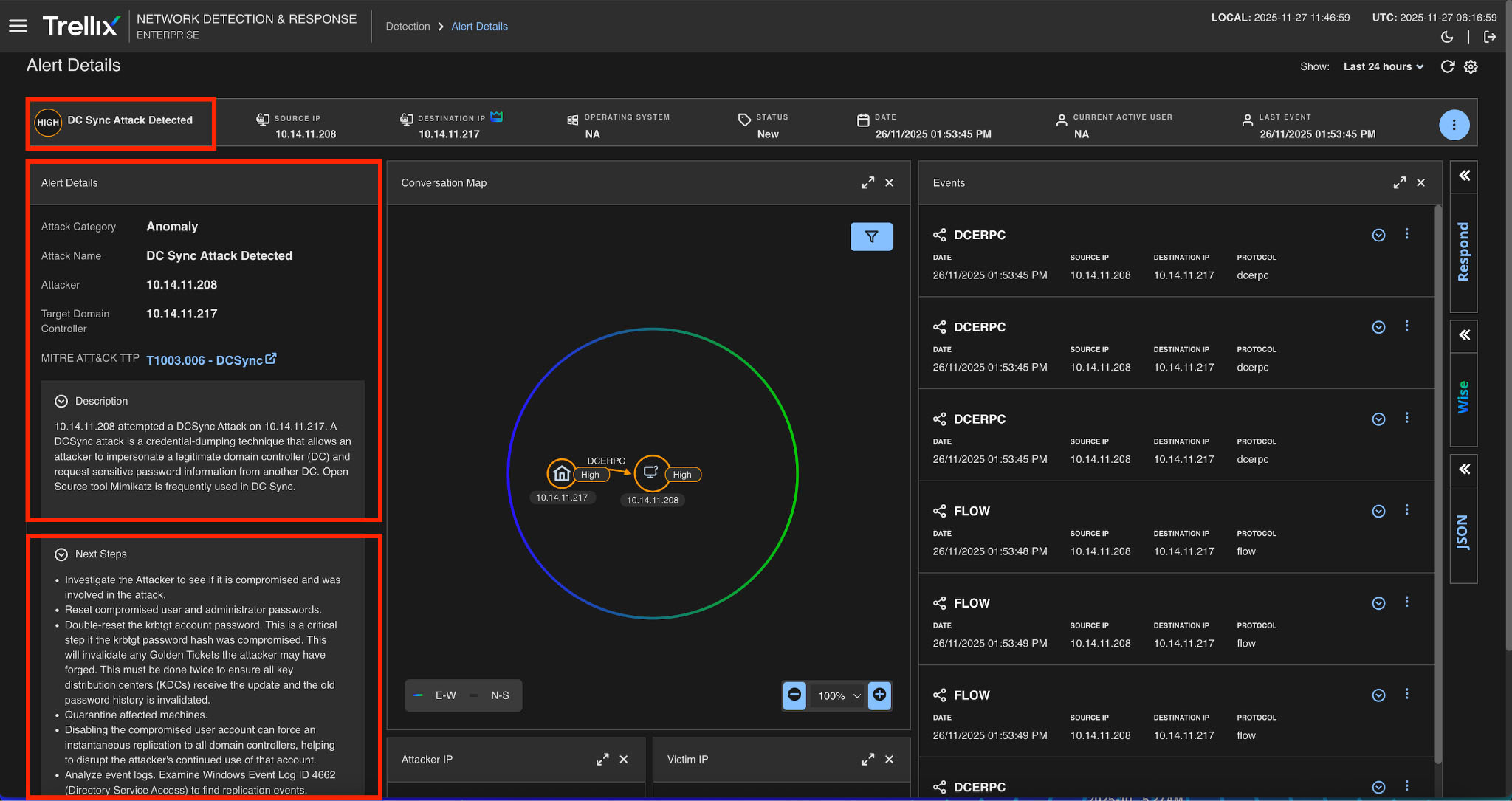
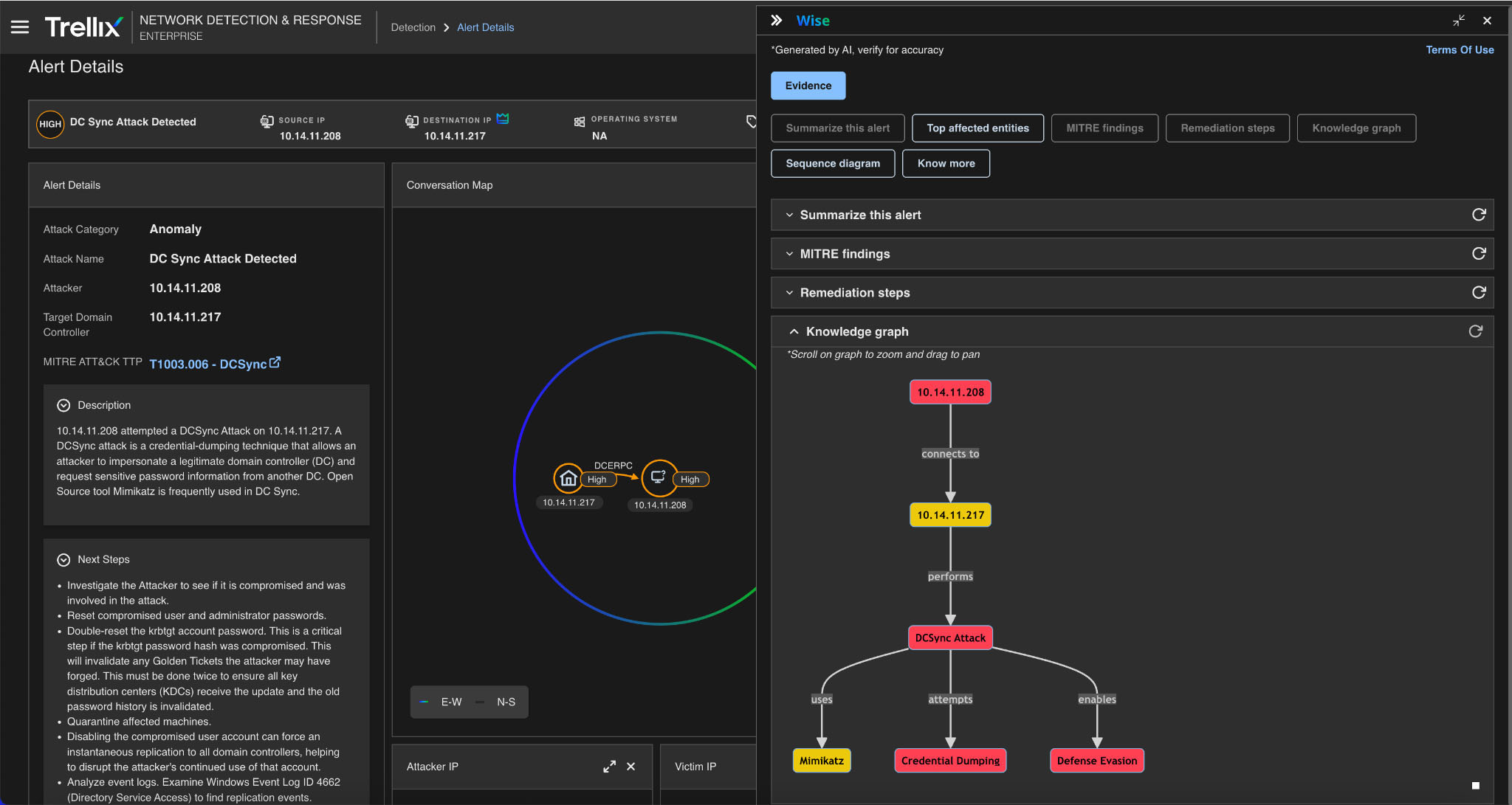
Figure 5 shows the initial moment of detection in the Trellix NDR security dashboard. A high-level alert, "DCSync Attack Detected," was issued in near real time. Trellix NDR detected this threat by analyzing network traffic and identifying the replication request as unusual since it originated from a non-domain controller host. This demonstrates the solution's ability to detect malicious uses of legitimate protocols.
Alert summary
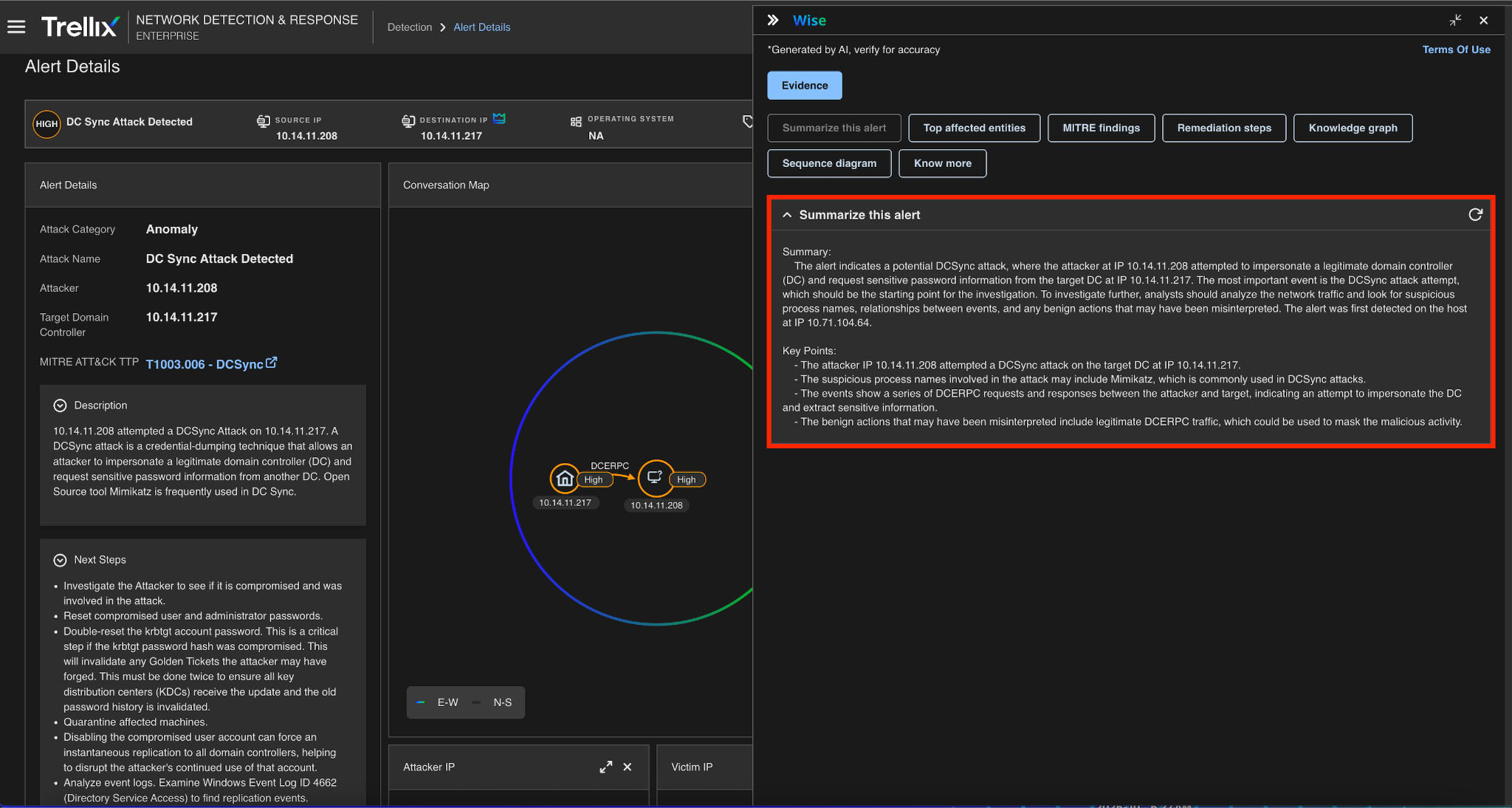
Trellix NDR uses Trellix Wise, to accelerate incident response (Figure 6). When the threat is detected, the system automatically generates a plain-language summary of the attack, explaining that a DCSync attack was detected between specific hosts, with suspicious DCE/RPC traffic as the underlying cause. This enables a SOC analyst to quickly understand the context of the alert without extensive manual investigation.
MITRE finding
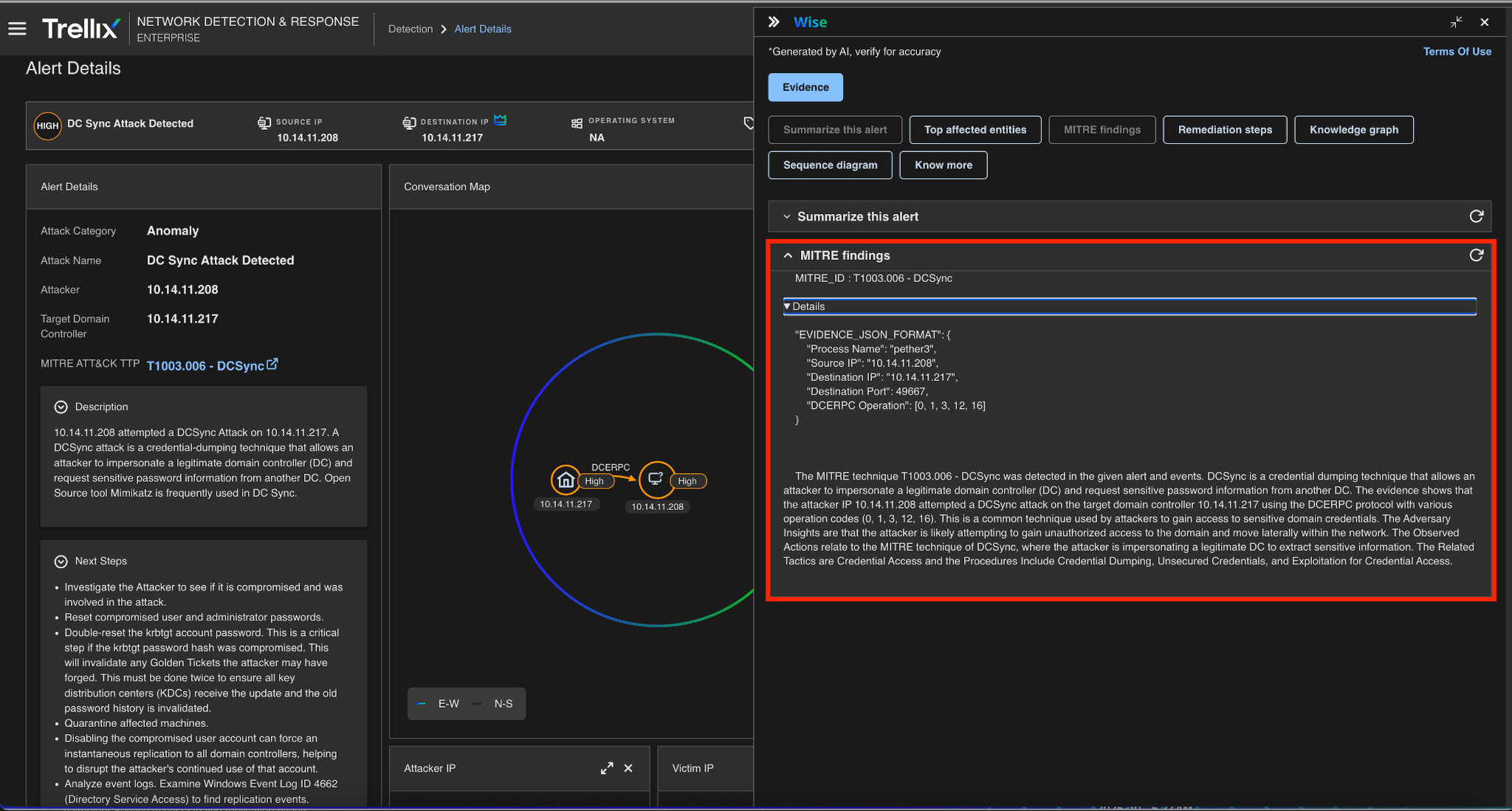
See how Trellix NDR enriches alerts by mapping them to a globally recognized framework in Figure 7. The detected DCSync activity is automatically assigned to MITRE ATT&CK Technique T1003.006. This provides critical context, allowing security teams to categorize the threat using a standard lexicon and determine that it is a type of OS Credential Dumping intended to exploit domain controller replication.
Remediation action
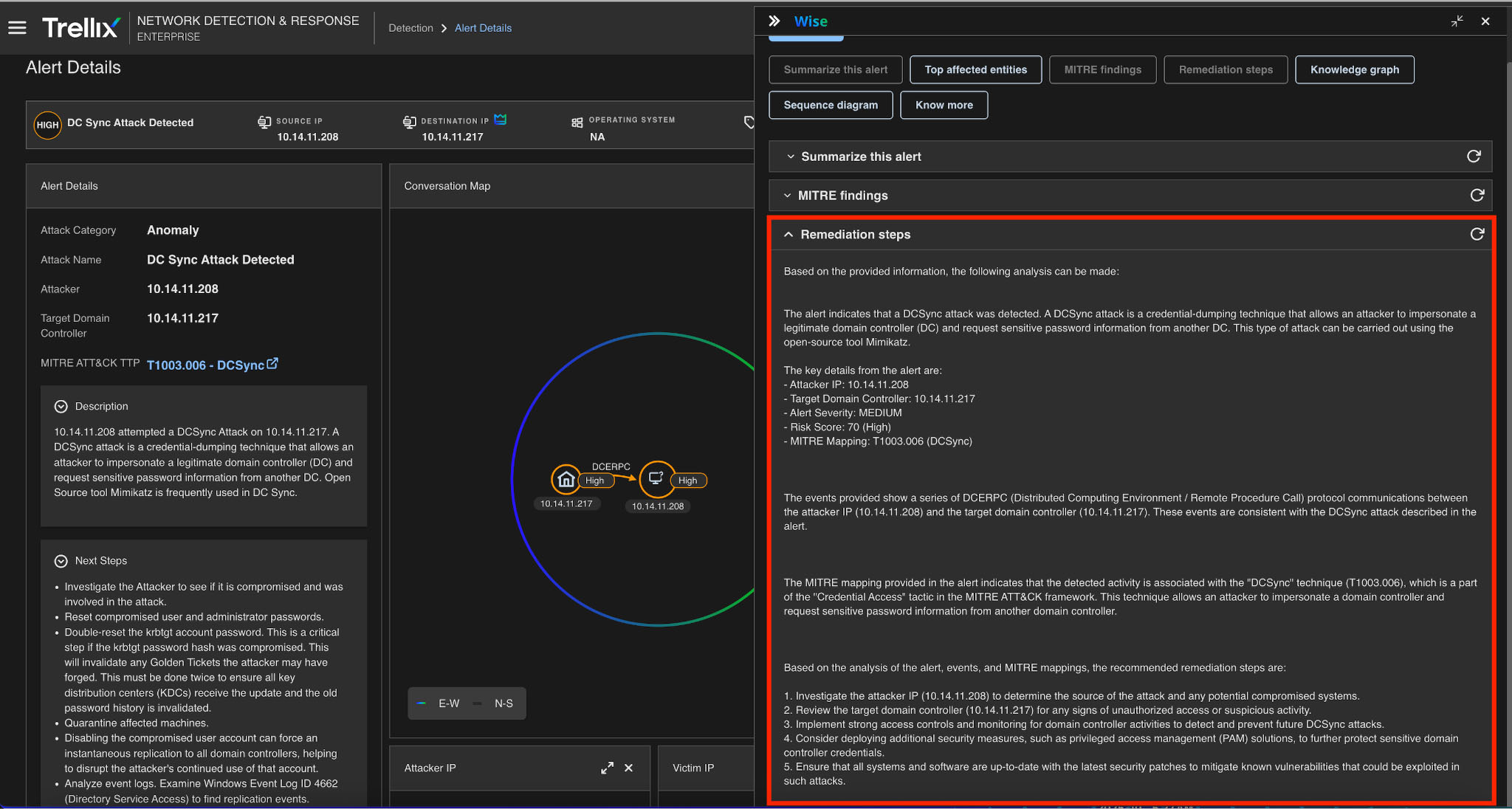
Moving from detection to action, Figure 8 shows Trellix NDR's guided remediation steps. The solution provides a set of actionable recommendations based on the specific DCSync alert. These steps guide the security team on how to investigate the compromised hosts, strengthen account and network security configurations, and improve domain controller monitoring to prevent future attacks.
Knowledge graph
The Trellix NDR Knowledge Graph depicts the connections between compromised users, command activity, network behavior, and credential flows. It enables analysts to understand the attack's footprint across users and systems.
Conclusion
The DCSync attack remains one of the most important post-exploitation techniques, allowing adversaries to achieve full domain compromise with stealth and precision. An attacker can steal the most sensitive credentials by exploiting legitimate Active Directory replication protocols, including the krbtgt hash required to create Golden Tickets for indefinite persistence.
As demonstrated, this powerful technique is not dependent on a single tool. Whether executed with the well-known Mimikatz utility or integrated into a framework such as the Metasploit meterpreter shell, the underlying behavior of malicious replication is consistent. For this reason, contemporary defenses need to move past tool-based signatures and concentrate on identifying the attacker's core methods.
Trellix Network Detection and Response (NDR) is specifically designed to address this challenge. Trellix NDR detects DCSync activity by analyzing network traffic for behavioral anomalies such as replication requests coming from non-domain controller hosts, regardless of the attacker's toolkit. The solution enhances these detections with critical context by mapping the activity to the MITRE ATT&CK framework, providing actionable remediation steps, and visualizing the attack's entire footprint using the knowledge graph.
To learn more about Trellix NDR, take our product tour to see it in action or visit this page.
RECENT NEWS
-
May 19, 2026
Trellix Appoints Joe Chen as Chief Technology Officer
-
Apr 08, 2026
Trellix prevents enterprise data exposure in sanctioned and shadow AI
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.
