Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more
ICS Security for Australian Critical Infrastructure
By Anam Haque · March 20, 2026
From Risk to Response with Trellix
Executive Summary
Industrial control systems operate critical infrastructure, including electricity networks, water treatment plants, transportation systems, and manufacturing facilities.
According to the Trellix 2025 Year in Review Australia Threat Report, Australia experienced 118 publicly disclosed ransomware incidents during 2025 involving 44 different ransomware groups, demonstrating a fragmented and opportunistic threat ecosystem targeting enterprises and critical infrastructure operators.
High-profile incidents such as the Colonial Pipeline ransomware attack, the Russia-Ukraine Viasat outage, and the 2022 Ukraine power grid disruption demonstrate that cyber-attacks targeting industrial environments can cause widespread operational disruption and, in some cases, direct physical impact. These events also show how cyber operations can coincide with physical conflict and extend beyond the intended target, affecting organisations globally. More recent incidents like the 2025 Poland power grid attack by the ELECTRUM threat group highlight a shift in attacker focus toward distributed energy resources and edge infrastructure.
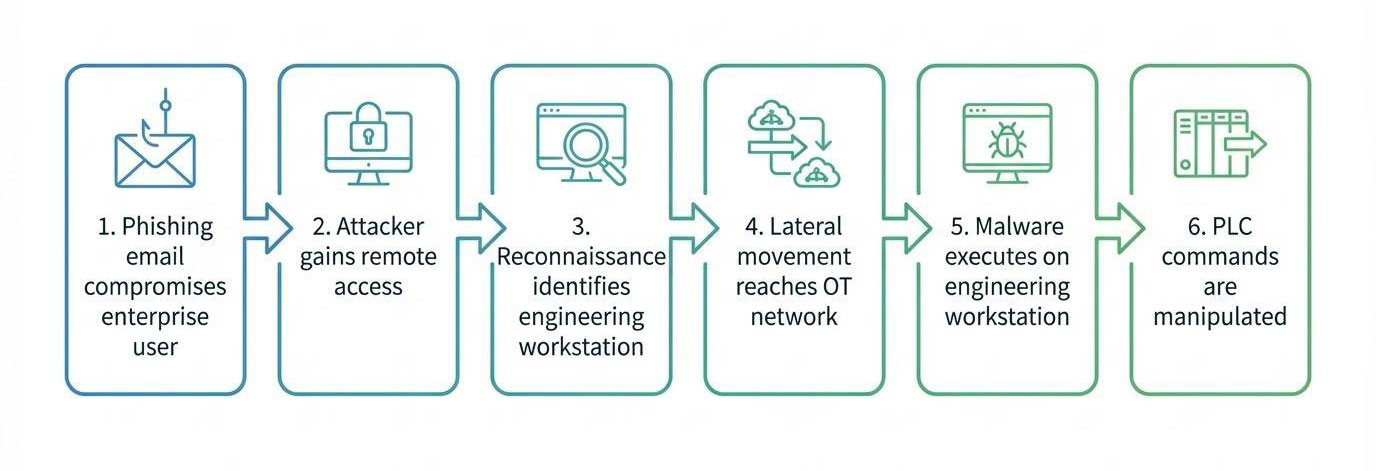
Most attacks targeting operational technology environments don’t begin inside OT networks. Instead, attackers typically compromise enterprise IT systems first and then move laterally toward engineering workstations and industrial control systems.
Recent Trellix CyberThreat reporting highlights a continued rise in advanced persistent threat (APT) activity targeting critical infrastructure sectors, with attackers increasingly focusing on long-term access and operational disruption.
Ransomware activity continues to dominate the threat landscape, with attackers expanding tactics to include data exfiltration and operational disruption, increasing pressure on critical infrastructure operators.
As industrial networks become increasingly connected to enterprise environments, cloud services, and remote vendor access systems, the cyber risk to critical infrastructure continues to grow.
In Australia, the Security of Critical Infrastructure (SOCI) Act requires operators of critical infrastructure to implement cyber risk management programs and report significant cyber incidents within strict timeframes.
To meet these obligations, organisations must gain visibility across both enterprise and operational environments while improving their ability to detect and respond to threats.
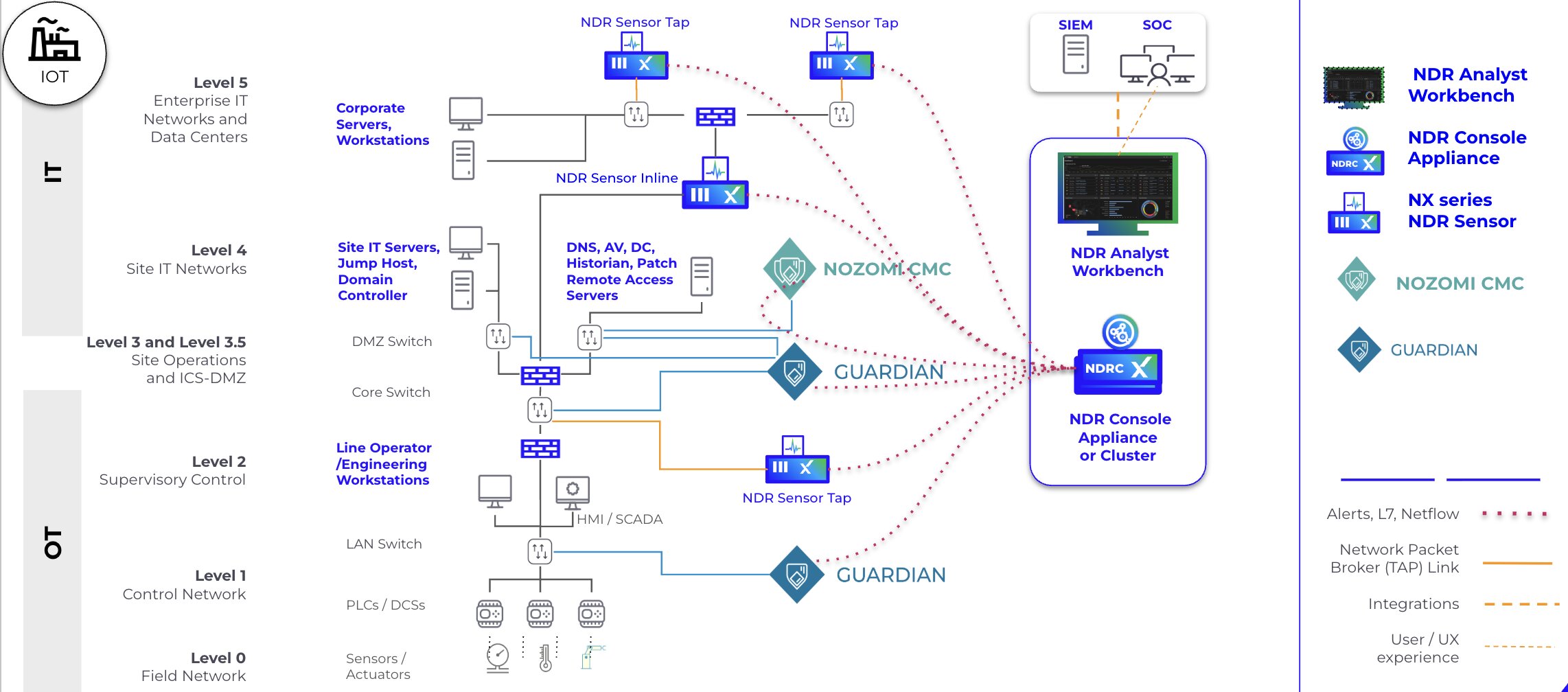
This article presents a security architecture that combines OT visibility from Nozomi with the Trellix security portfolio, enabling detection and response capabilities across the industrial attack lifecycle.
Key Takeaways
- Industrial attacks commonly follow an IT-to-OT attack path
- Engineering workstations represent a critical security control point
- Network visibility is essential because many OT devices can’t run endpoint agents
- SOC teams require cross-domain telemetry correlation
- Security architectures should align with MITRE ATT&CK for ICS and IEC 62443
Security Architecture Overview
Protecting critical infrastructure requires a layered security architecture that aligns detection and response capabilities across both enterprise IT and operational technology environments. Rather than relying on isolated controls, organisations must implement integrated capabilities that detect attacker behaviour across the full attack lifecycle—from initial compromise to OT impact.
Figure 1 below illustrates how Trellix capabilities map to key security layers and support detection, protection, and response across industrial environments.
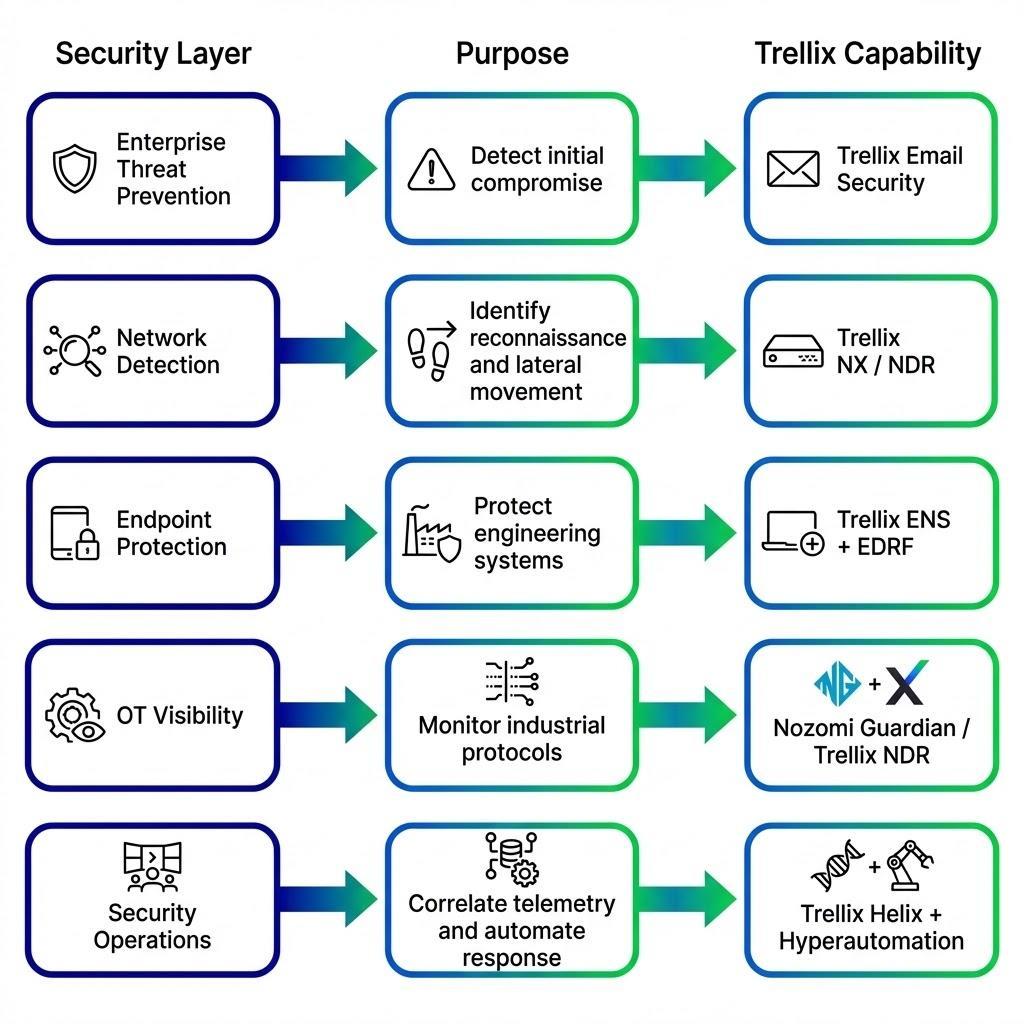
This architecture highlights how different security layers work together:
- Enterprise Threat Prevention
Trellix Email Security detects and blocks phishing and initial compromise attempts. - Network Detection
Trellix NX and NDR identify reconnaissance activity and lateral movement across IT and OT networks. - Endpoint Protection
Trellix ENS and Trellix EDR with Forensics (EDRF) protect engineering workstations and critical systems from malware and unauthorised activity. - OT Visibility
Nozomi Guardian and Trellix NDR provide visibility into industrial protocols and OT asset behaviour. - Security Operations
Trellix Helix and Hyperautomation correlate telemetry and enable coordinated detection and response.
This layered approach ensures that attacks can be detected and disrupted at multiple stages rather than relying on a single control point. From my experience, a layered approach not only improves detection but also gives teams more breathing room to respond effectively.
Threat Landscape for Industrial Control Systems
Industrial organisations face a rapidly evolving cyber threat environment. Nation-state actors, financially motivated ransomware groups, and opportunistic attackers increasingly target operational technology environments (ENISA, 2023; Dragos, 2023; ACSC, 2024).
Recent Trellix threat intelligence highlights increased activity targeting industrial environments, including ransomware campaigns and OT-focused intrusion attempts across critical sectors (Trellix, 2025). Major incidents demonstrating these risks include:
- Ukraine Power Grid Attack (2015–2016)
- Triton / Trisis Malware (2017)
- Colonial Pipeline Ransomware (2021)
- Volt Typhoon activity (2023–2024) demonstrating long-term persistence in critical infrastructure environments (CISA et al., 2024)
If you’re running a plant or utility, these examples might feel uncomfortably close to home.
Why Now More Than Ever
Recent threat intelligence highlights the growing urgency for stronger security controls across industrial environments. According to Trellix threat intelligence, Australia experienced over 100 publicly disclosed ransomware incidents involving dozens of ransomware groups, demonstrating a fragmented and opportunistic threat ecosystem targeting enterprises and critical infrastructure operators (Trellix, 2026).
Ransomware campaigns have evolved toward multi-stage extortion models, combining data encryption, data theft, and operational disruption to increase pressure on victims. Some groups are now targeting industrial systems, including SCADA environments and process control networks.
Threat actors are also increasingly abusing legitimate administrative tools such as remote monitoring and management (RMM) platforms to maintain persistent access while blending malicious activity with normal IT operations (Trellix, 2025). Generative artificial intelligence is accelerating cybercrime activity, enabling attackers to create convincing phishing campaigns at scale and automate social engineering attacks.
These trends illustrate a shift in the threat landscape, where attackers combine automation, legitimate tools, AI-driven techniques, and ransomware ecosystems to conduct highly effective attacks against critical infrastructure environments.
Understanding ICS Environments and Components
Industrial control systems are designed to monitor and control physical processes across sectors including energy, water, transportation, and manufacturing. These environments rely on specialised systems that operate in real time and are often designed for availability and safety rather than security.
Typical ICS Components
Common components include:
- PLCs (Programmable Logic Controllers)
- RTUs (Remote Terminal Units)
- SCADA (Supervisory Control and Data Acquisition) systems
- HMIs (Human Machine Interfaces)
- EWS (Engineering Workstations)
These components form interconnected systems that manage industrial operations and control physical processes. To put it simply, think of PLCs and RTUs as the ‘nervous system’ of a modern factory.
SOCI Act Requirements for Critical Infrastructure
Australia’s Security of Critical Infrastructure (SOCI) Act requires organisations to implement cyber risk management programs and meet strict incident reporting obligations. Figure 2 summarises the SOCI Act incident reporting requirements for critical infrastructure operators.

These requirements reinforce the need for timely detection and response capabilities across both IT and OT environments. For many Australian operators, meeting these obligations can feel overwhelming in practice.
How Attackers Gain Initial Access via Phishing and Identity Abuse
Most attacks against critical infrastructure begin in IT environments, typically through phishing, credential theft, or exploitation of internet-facing services. Email remains one of the primary initial access vectors for attackers targeting enterprise and industrial environments.
Trellix Email Security provides advanced threat detection to identify phishing attempts, malicious attachments, and embedded threats before they reach users.
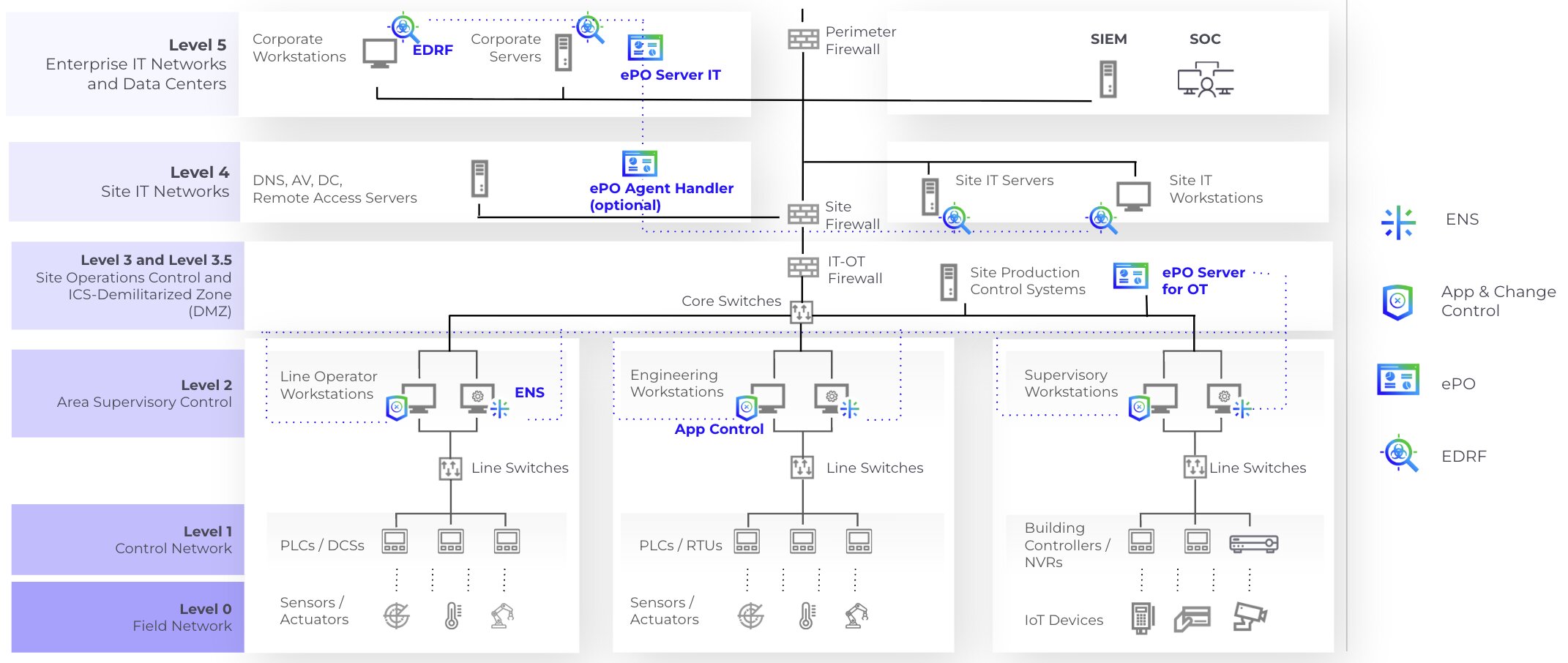
Stopping Initial Compromise on Engineering Workstations and OT Systems
Once initial access is established, attackers target engineering workstations and OT-connected endpoints to establish persistence and expand access. Key Trellix protections include:
- Trellix ENS
- Trellix EDRF
- Trellix Application and Change Control
- Trellix Device Control
Application Control prevents unauthorised execution, while Device Control restricts removable media usage, a common infection vector in air-gapped OT environments. These controls are particularly important in OT environments where legacy applications and end-of-life systems can’t be regularly patched.
By enforcing strict allow-listing and controlling external media, organisations can significantly reduce the attack surface on critical OT assets without impacting system stability.
Detecting Lateral Movement and Persistence Across IT and OT
After gaining a foothold, attackers move laterally across IT systems and attempt to pivot into OT networks while maintaining persistence using legitimate tools and stolen credentials. Threat actors increasingly abuse legitimate administrative tools such as RMM software to maintain persistence and evade detection (Trellix, 2025). Trellix EDRF provides deep visibility into endpoint activity and enables detection of anomalous behaviour.
NDR Deployment in OT Environments
Network detection provides visibility into attacker activity across both enterprise and industrial environments. Trellix NX and NDR enable detection of lateral movement, command-and-control activity, and suspicious network behaviour. In OT environments, passive monitoring is critical due to limited ability to deploy agents.
By integrating with Nozomi Guardian, organisations gain visibility into industrial protocols such as Modbus, DNP3, IEC-104, and OPC.
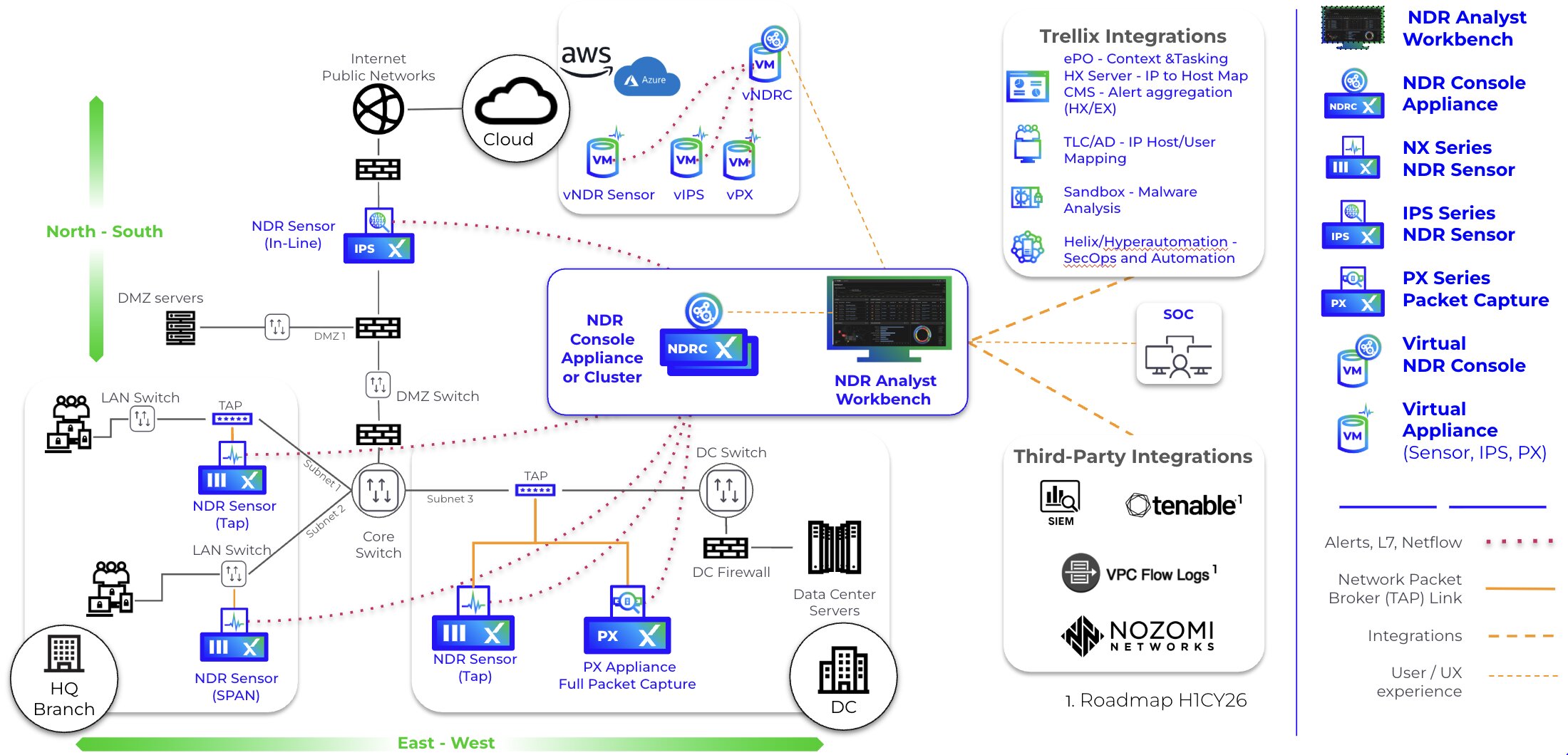
Connecting Weak Signals to Real Attacks in SOC Operations
Detection depends on correlating signals across multiple systems before operational impact occurs. Many advanced attacks don’t trigger traditional alerts, requiring proactive threat hunting to identify anomalous behaviour and identity misuse (Trellix, 2026). Trellix Helix enables cross-domain telemetry correlation.
Using Threat Intelligence to Prioritise Real-World Risk
Threat intelligence enables prioritisation of alerts based on real adversary behaviour, including tactics, techniques, and active campaigns. Trellix threat intelligence capabilities, such as Trellix Insights and Threat Intelligence Exchange, correlate global telemetry and map threats to endpoints, campaigns, and indicators in real time, allowing organisations to predict and prioritise relevant risks (Trellix, 2025).This supports risk-based vulnerability prioritisation by focusing on exposures actively exploited in the wild rather than relying solely on severity scores. By aligning prioritisation with current threat activity and intelligence reporting, organisations can make faster and more effective response decisions in both IT and OT environments (Trellix, 2025; Trellix, 2026).
Responding to Attacks Without Disrupting Critical OT Operations
Response in OT environments must balance speed with safety, as incorrect actions can disrupt physical processes. Trellix Hyperautomation enables automated response in enterprise IT environments to contain threats quickly. In OT environments, however, response actions must be carefully validated due to the risk of operational disruption. This distinction requires SOC teams to apply automation selectively, balancing speed in IT with safety in OT systems.
In addition to platform capabilities, incident response is supported through Trellix Managed Detection and Response (MDR), which provides 24/7 monitoring, threat hunting, and expert-led response. We can also offer on-demand IR support through our Professional Services Consultants. Private Global Threat Intelligence further enhances this by delivering real-time intelligence, including in air-gapped environments, enabling faster and more informed response decisions.
Reducing Exposure in Legacy OT Systems
Legacy OT systems remain highly vulnerable due to limited patching and outdated software. Application Control provides protection where patching is not feasible.
How Attacks Progress from IT to OT in Critical Infrastructure
This architecture reflects how attacks move from enterprise IT into OT environments and how Trellix solutions disrupt this path.
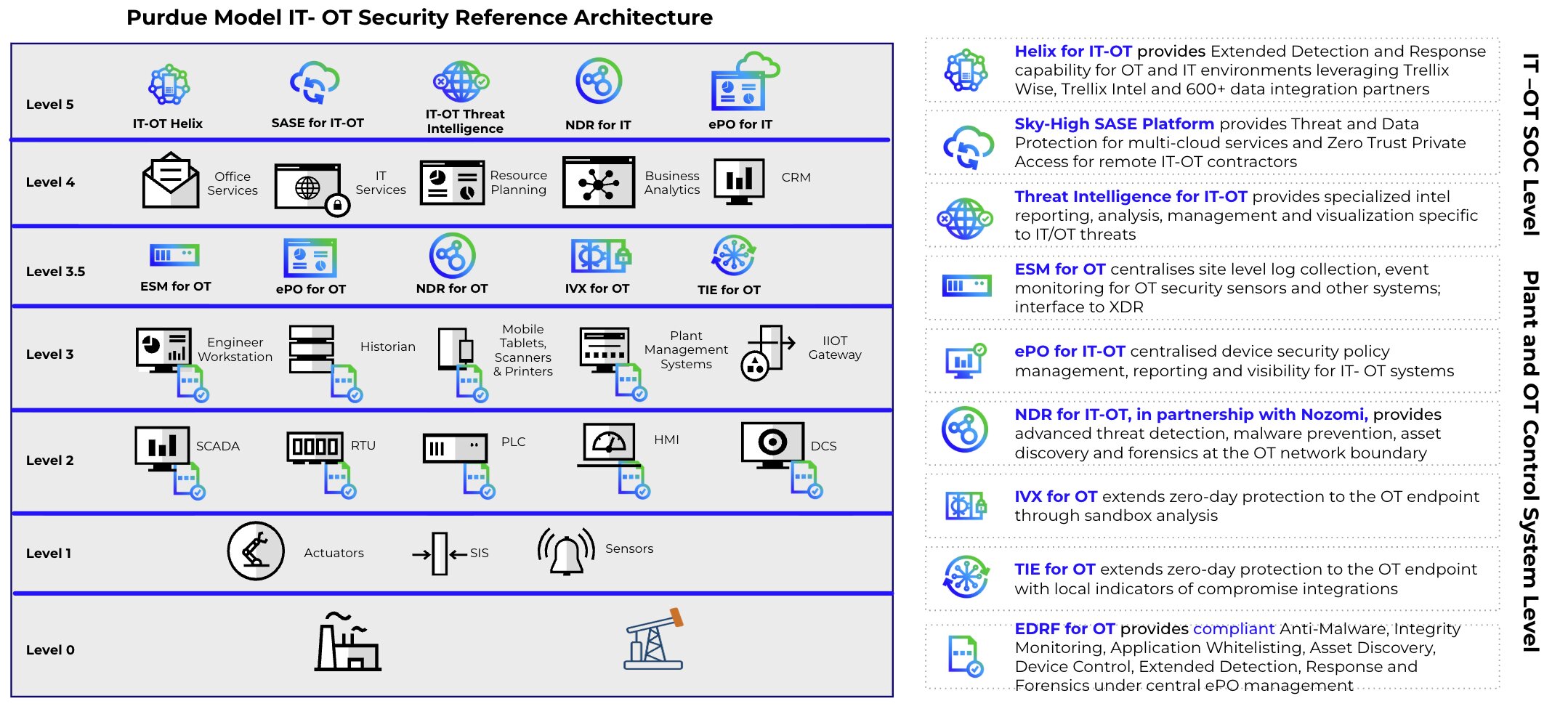
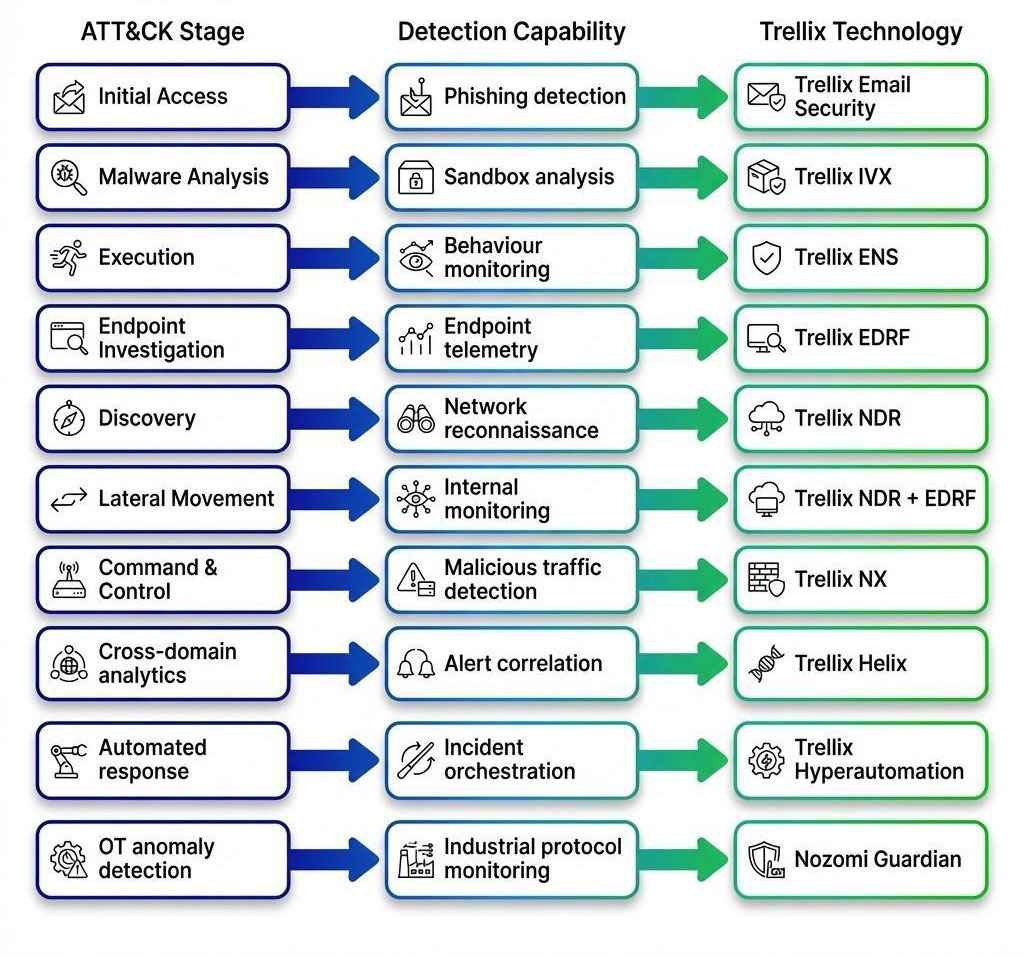
Mapping Trellix Solutions to MITRE ATT&CK for ICS
Trellix technologies align with MITRE ATT&CK for ICS to detect attacks across multiple stages. Let’s break down how these solutions work in real environments. Solutions such as Email Security, IVX, ENS, NDR, and EDRF identify phishing, malware activity, and lateral movement, while Helix and Hyperautomation correlate alerts and automate response, supported by Nozomi Guardian for OT monitoring.
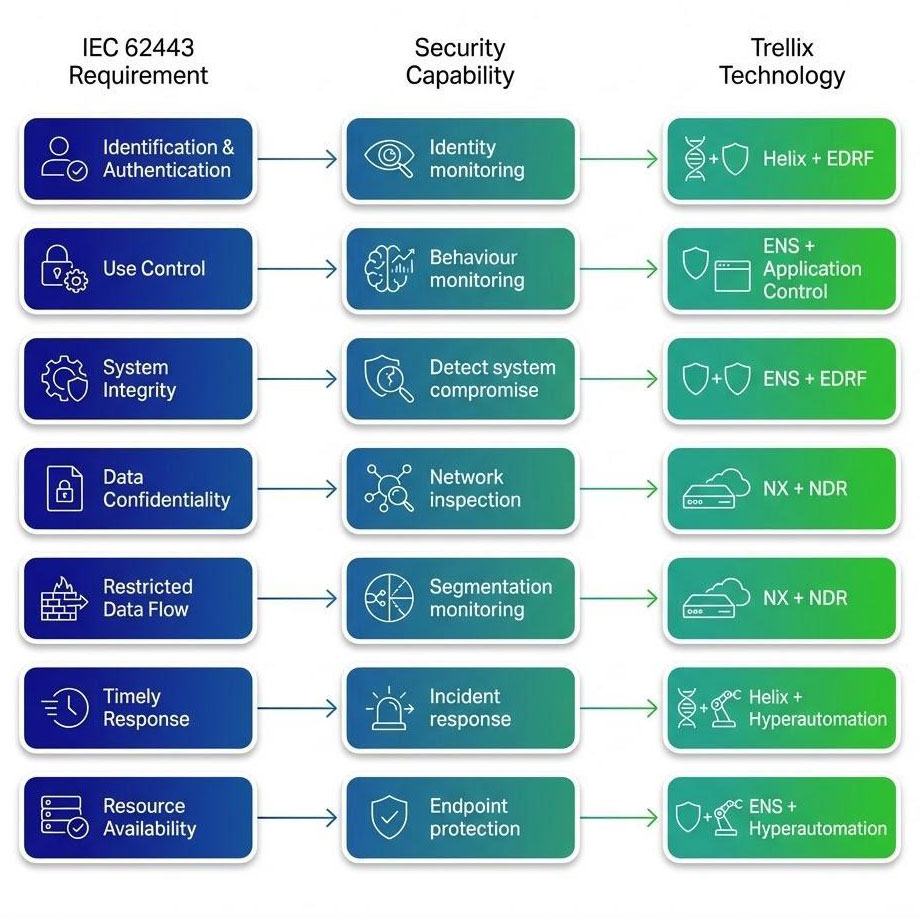
Alignment with IEC 62443 Security Principles
IEC 62443 defines a series of standards for securing operational technology (OT) in industrial automation and control systems. Australia has adopted this framework as AS IEC 62443 to strengthen the protection of critical infrastructure. The standard outlines foundational security requirements, but organisations must implement these through a combination of architecture, processes, and technology. Trellix solutions, alongside integrations such as Nozomi for OT visibility, support this by providing capabilities for identity and behavioural monitoring, system integrity validation, and network inspection across IT and OT environments. Solutions including ENS, EDRF, NX, NDR, Helix, and Hyperautomation help detect compromise, monitor data flows, and improve incident response while supporting system availability, forming a practical layer aligned to IEC 62443 requirements rather than full compliance.
AI-Driven Security Operations - Trellix Wise
Security operations teams must analyse large volumes of alerts across IT and OT environments, making manual investigation inefficient. Trellix Wise applies artificial intelligence to help analysts prioritise alerts, correlate events, and accelerate investigations.
By reducing noise and guiding analysis, Trellix Wise improves response speed and enables more effective handling of complex IT–OT threats.
Conclusion
Cyber-attacks targeting industrial organisations are increasing in frequency and sophistication. Most attacks begin in enterprise IT environments before impacting operational technology systems. As threat actors evolve—leveraging AI, legitimate tools, and targeting operational disruption—security architectures must reflect real attacker behaviour.
By combining enterprise security telemetry, network detection, endpoint protection, and OT monitoring, organisations can detect and disrupt attacks before they impact industrial processes. In an environment where IT compromise leads to OT impact, a proactive and intelligence-driven security approach is essential. Ultimately, our goal should be to stay one step ahead of attackers, not just react after the fact.
The Trellix platform enables this approach by providing integrated visibility, detection, and response across both IT and OT environments, supporting security teams in identifying and disrupting attacks across the full lifecycle.
References
Australian Cyber Security Centre. (2024). Annual cyber threat report 2023–2024.
https://www.cyber.gov.au/about-us/view-all-content/reports-and-statistics/annual-cyber-threat-report-2023-2024
Australian Government Department of Home Affairs. (2022). Security of Critical Infrastructure Act 2018 guidance.
https://www.homeaffairs.gov.au/national-security/critical-infrastructure-security/security-of-critical-infrastructure-act
Cybersecurity and Infrastructure Security Agency. (2023). Industrial control systems cybersecurity resources.
https://www.cisa.gov/topics/industrial-control-systems
Cybersecurity and Infrastructure Security Agency, Federal Bureau of Investigation, National Security Agency, & international partners. (2024). PRC state-sponsored actors compromise and maintain persistent access to U.S. critical infrastructure (AA24-038A).
https://www.cisa.gov/news-events/cybersecurity-advisories/aa24-038a
Dragos. (2023). ICS/OT cybersecurity year in review 2023.
https://www.dragos.com/year-in-review/
European Union Agency for Cybersecurity. (2023). ENISA threat landscape 2023.
https://www.enisa.europa.eu/publications/enisa-threat-landscape-2023
Gartner. (2023). Market guide for extended detection and response.
Greenberg, A. (2019). Sandworm: A new era of cyberwar and the hunt for the Kremlin's most dangerous hackers. Doubleday.
International Society of Automation. (2013). IEC 62443 industrial communication networks and system security standards.
https://www.iec.ch/dyn/www/f?p=103:85:0::::FSP_LANG_ID:25
Mandiant. (2022). M-Trends 2022: Insights into today’s cyber attack trends.
https://www.mandiant.com/resources/m-trends
MITRE. (2023). ATT&CK® for industrial control systems.
https://attack.mitre.org/matrices/ics/
National Institute of Standards and Technology. (2015). Guide to industrial control systems (ICS) security (SP 800-82 Rev. 2).
https://csrc.nist.gov/publications/detail/sp/800-82/rev-2/final
Trellix. (2025). 2025 year in review: Australia threat landscape report.
Trellix. (2025). CyberThreat report (April 2025). Trellix Advanced Research Center.
https://www.trellix.com/advanced-research-center/threat-reports/april-2025/
Trellix. (2025). CyberThreat report (October 2025). Trellix Advanced Research Center.
https://www.trellix.com/advanced-research-center/threat-reports/october-2025/
Trellix. (2025). Healthcare cybersecurity threat intelligence report. Trellix Advanced Research Center.
https://www.trellix.com/assets/reports/trellix-healthcare-cybersecurity-threat-intelligence-report.pdf
Trellix. (2025). Operational technology threat report. Trellix Advanced Research Center.
https://www.trellix.com/en-au/advanced-research-center/threat-reports/
Trellix. (2026). Iran cyber update and geopolitical threat brief.
Trellix. (2026). SecondSight threat hunting report. Trellix Advanced Research Center.
https://www.trellix.com/en-au/advanced-research-center/threat-reports/
Trellix. (2025). Trellix threat intelligence platform.
https://www.trellix.com/en-au/platform/threat-intelligence/
Verizon. (2024). 2024 data breach investigations report.
https://www.verizon.com/business/resources/reports/dbir/
RECENT NEWS
-
Apr 08, 2026
Trellix prevents enterprise data exposure in sanctioned and shadow AI
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
-
Dec 11, 2025
Trellix Finds 97% of CISOs Agree Hybrid Infrastructure Provides Greater Resilience
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.
