Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more
Malware-As-A-Service Redefined: Why XWorm is outpacing every other RAT in the underground malware market
By Boggavarapu R S S Srinivas Gupta and Ravishankar N C · March 12, 2026
Introduction
In the evolving landscape of cybercrime, threat actors are constantly pursuing the "perfect" weapon: malware that is lightweight, modular, and—most importantly—stealthy. The underground market eagerly adopts any tool that balances high functionality with low detection rates. XWorm has emerged as the premier example of this shift. Following the significant disruption caused by XWorm v6.X, the community is now grappling with the even more potent Version 7.x. In this blog, we will see how attackers have tried to target a Taiwan-based network security company.
This analysis dissects the active XWorm v7.1 kill chain, explores the market trends fueling its growth, and exposes the Telegram channels where this sophisticated RAT is sold as a high-tier commodity.
Market Trends
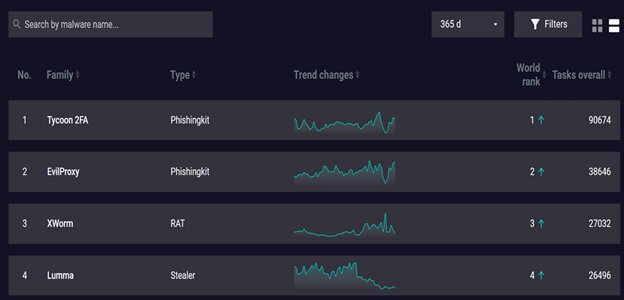
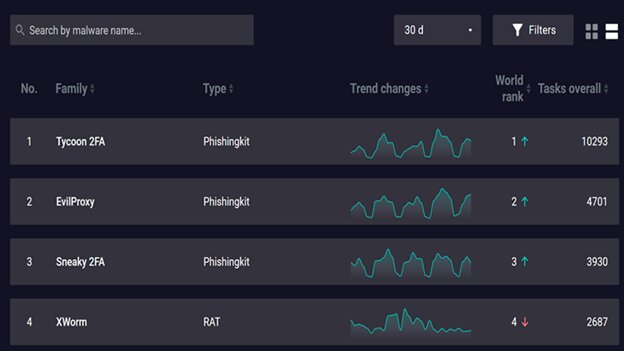
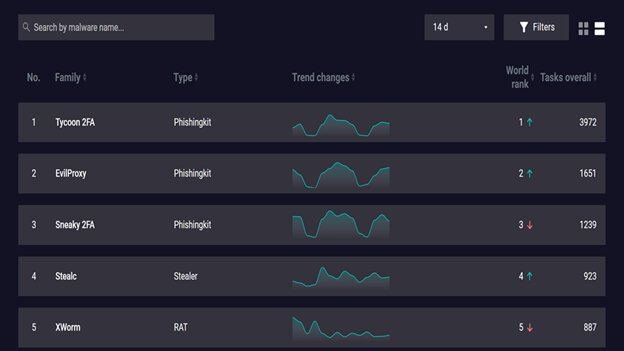
The underground market is currently witnessing competition among commodity malware for cybercrime. XWorm has emerged as the definitive commodity king by surpassing most notorious RAT tools like AsyncRAT and QuasarRAT. XWorm is even competing with emerging RATs like DCRAT in the underground market.
According to the ANY.RUN 2025 Annual Threat Report, XWorm saw a staggering 174% surge in detections over the last year. While legacy tools like Remcos and AgentTesla saw their market rankings drop to 7th and 10th, respectively, XWorm climbed to #3 in the 2025 threat report.
Winning the "RAT Race": Market dominance by the numbers
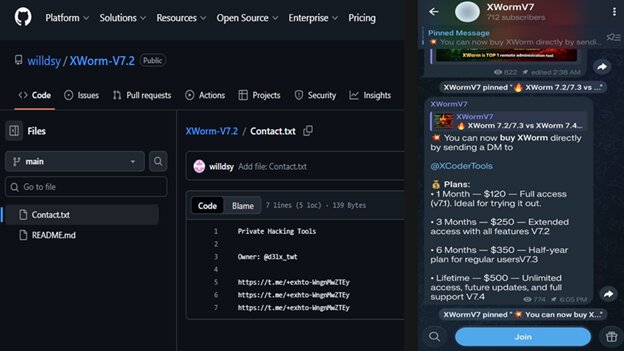
XWorm dominance isn’t just about the low price tag (averaging a $500 lifetime subscription). It is about market capture through "effective simplicity."
- Outpacing the giants: In 2025, XWorm detections were 4.3x higher than in 2024. It now accounts for a significant share of the 2 million+ sandbox sessions analyzed by security researchers annually.
- Massive scale: A single 2025 builder campaign was recently linked to over 18,000 compromised devices, demonstrating its ability to cause "Enterprise-scale" damage at a "clearance bin" price.
- We have observed that a new Telegram channel is actively pushing updates to the XWorm v7.x version.
Anatomy of an infection: The 2026 XWorm kill chain
We have analysed a new XWorm7.1 infection chain using JavaScript to download secondary payloads instead of a typical LNK file. It performs a "Living off the Land" (LOTL) attack by abusing a legitimate Microsoft utility (Aspnet_compiler.exe) to hide its activity.
Recent telemetry has uncovered a sophisticated infection chain that weaponizes CVE-2025-8088, a high-severity, path-traversal vulnerability affecting WinRAR versions 7.12 and earlier. Threat actors are utilizing Discord as a primary delivery vector, distributing weaponized archives (MD5: 2074283c9ccc441185cba631fcc8a234) disguised as legitimate game modifications or community plugins.
Technically, the exploit leverages NTFS Alternate Data Streams (ADS). The attack does not require a complex multi-stage downloader. Instead, it relies on a crafted archive that abuses the :txt:stream syntax to write files to arbitrary system paths. According to Google Threat Intelligence, this specific vulnerability has become a staple for both state-sponsored and financially motivated actors due to its high reliability and ability to bypass standard user awareness. Organizations are urged to update to WinRAR 7.13+ immediately to mitigate this LOTL execution style.
Note on Analytical Scope: Trellix is actively monitoring this Discord-based WinRAR delivery vector (CVE-2025-8088) and conducting threat hunting to identify relevant data.
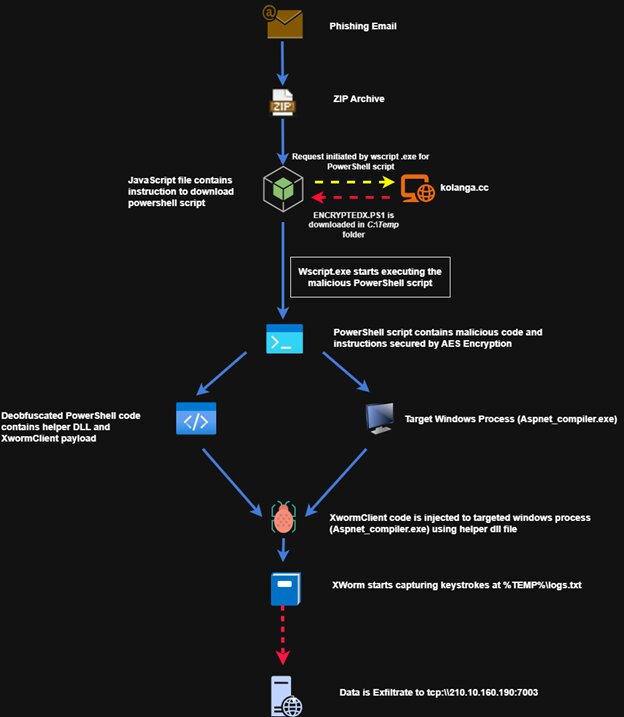
Anatomy view
The 7-stage execution flow
- Initial access: Victims receive a phishing email containing a ZIP attachment, such as "MFEQuotation Work request for NCSOCSO.zip".
- The JavaScript dropper: Double-clicking the enclosed .JS file triggers wscript.exe and attempts to connect to a remote server (e.g., kolanga[.]cc) to download the primary engine.
- Encrypted PowerShell staging: The downloaded PowerShell script serves as a secure container, carrying a large block of encrypted data and a hardcoded AES decryption key.
- Living-off-the-Land: The script executes with the -nop and -ep bypass switches to evade safety checks. It then launches the trusted Microsoft application Aspnet_compiler.exe.
- In-Memory execution: The script performs Reflective DLL Injection, carving space in the memory of the compiler process to insert the XWormClient Payload.
- Data capture: The malware captures every keystroke, saving data to a hidden log file in the %TEMP% folder.
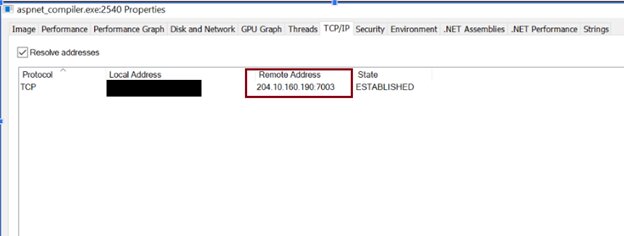
- Data exfiltration: At regular intervals, the encrypted logs are sent to the attacker's Command & Control (C2) server (e.g., 204.10.160.190) via TCP port 7003.
Comprehensive details of kill chain
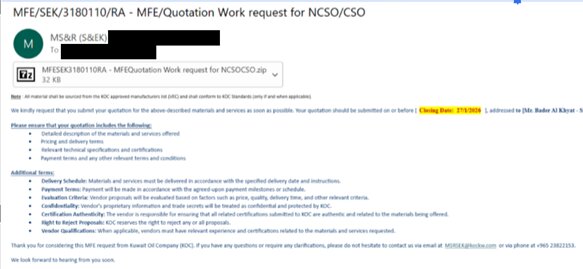
1. Initial access: Phishing mail (The zip-and-script trap)
In 2025 and 2026, XWorm operators have largely moved away from bulky .EXE attachments, which are easily flagged by modern mail gateways. Instead, they favor a multi-stage delivery designed to exploit user trust and system defaults. During our analysis, we observed the victim receiving a phishing email containing a file named "MFEQuotation Work request for NCSOCSO.zip" as an attachment and other information.
2. The JavaScript dropper
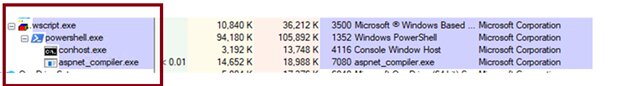
If the victim is duped into opening the attachment and its enclosed file, the JS file executes via wscript.exe and attempts to connect to a remote server to download a PowerShell script, which serves as the primary engine for the second stage of the infection.

The JavaScript file contains obfuscated code and junk data. The file also contains instructions to download a PowerShell script and execute it using special flags like “-nop -ep bypass.”
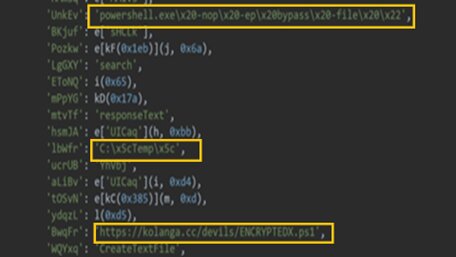
Upon execution of the Javascript file, it is performing network activity for downloading a malicious PowerShell script from hxxps[://]kolanga[.]cc/devils/ENCRYPTEDX[.]ps1.
At the time of publication, the download of hxxps[://]kolanga[.]cc/devils/ENCRYPTEDX[.]ps1 is still available. The threat actor is active and potentially infecting additional machines.
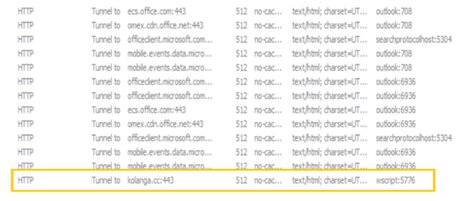
Following a successful connection, wscript.exe downloads the malicious PowerShell script and stores it in the "C:\Temp" directory before execution:
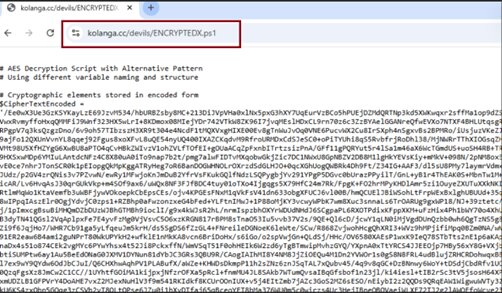
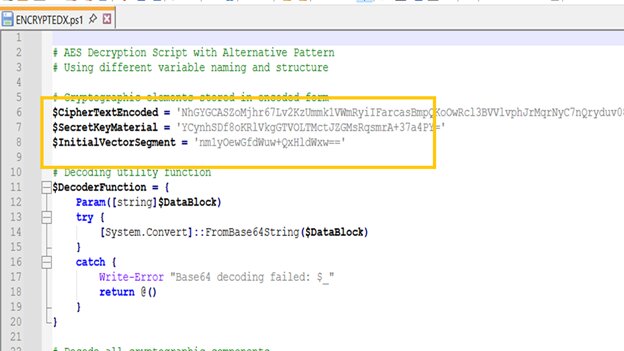
3. Encrypted PowerShell staging
The downloaded PowerShell isn't just a script—it's a secure container.
- Encryption: The script contains a large block of encrypted data and a hardcoded decryption key.
- Instructional logic: Once decrypted, it carries instructions to target a legitimate system binary (Aspnet_compiler.exe).
- DLL reflective loading: Powershell also prepares a DLL payload in memory:
4. Living-off-the-Land: Abusing Aspnet_compiler.exe
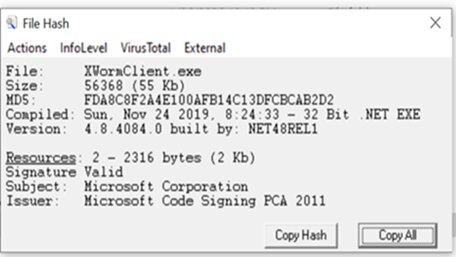
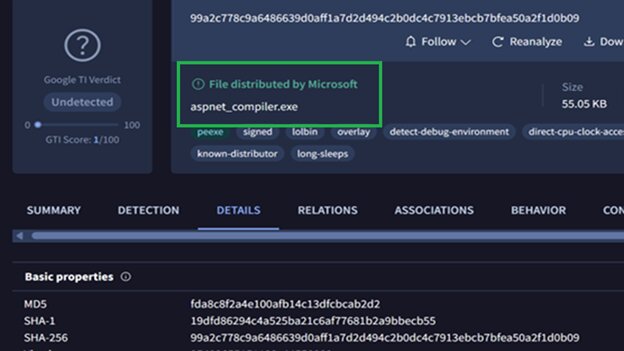
In the next stage, the downloaded PowerShell script in the C:\Temp folder will be executed using execution parameters “-nop -ep bypass”. To stay "Silent," the PowerShell script launches the legitimate Microsoft utility:
“C:\Windows\Microsoft.NET\Framework\v4.0.30319\Aspnet_compiler.exe”
As this is a trusted Windows process, most security tools will let it run. The PowerShell script then performs Reflective DLL Injection, carving out space in the memory of the Aspnet_compiler.exe process and then inserting the malicious XWorm DLL directly.
Dissecting the PowerShell script
The decrypted PowerShell script listed below confirms the malicious DLL loads the final payload:
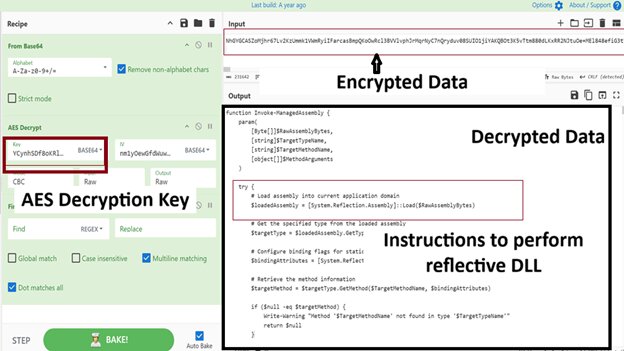
The helper DLL is stored in a variable called “$decodedAssemblyBytes” during decryption:
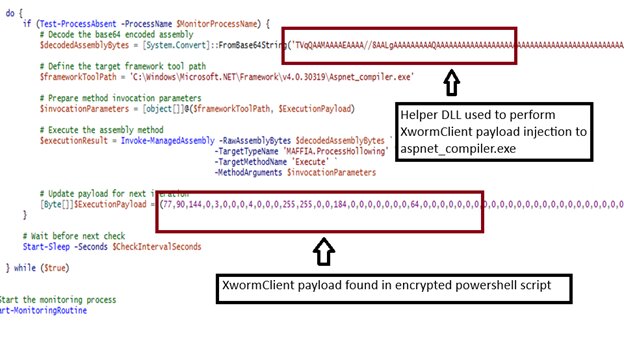
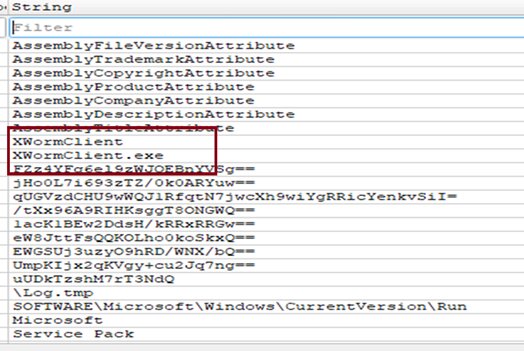
After applying a series of de-obfuscation and cleaning steps, the following strings in the helper DLL file can be seen:
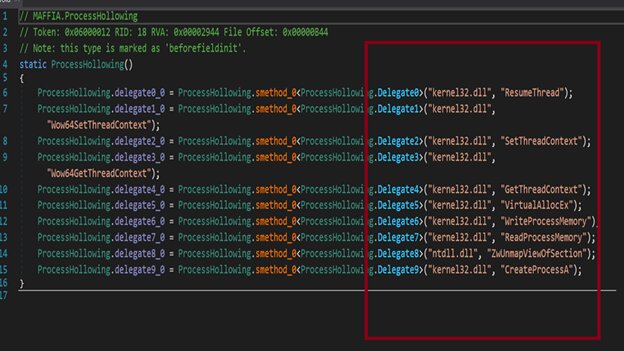
API’s found in the helper DLL file confirm that the DLL is used to inject the malicious XWorm payload to Aspnet_compiler.exe
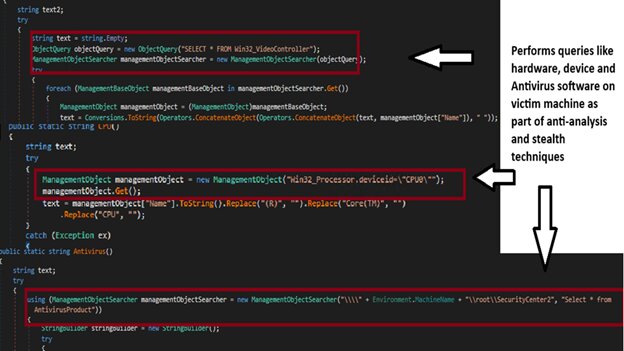
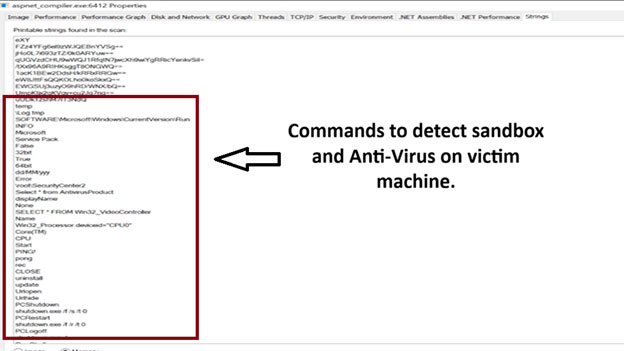
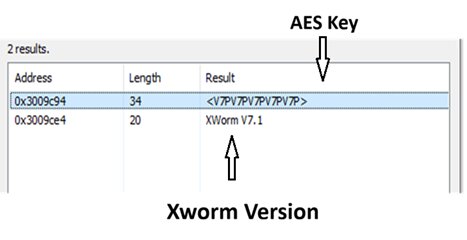
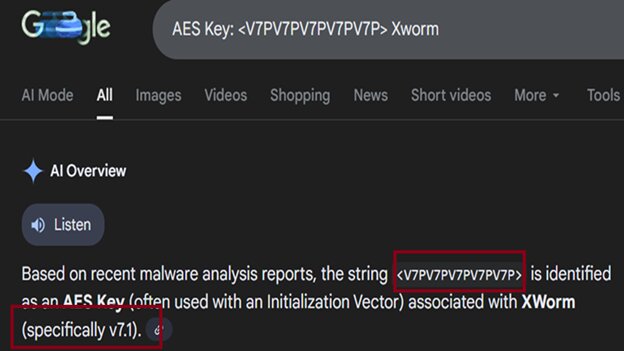
Following the reconstruction of the core XWorm v7.1 payload from raw data, our analysis reveals a sophisticated .NET-developed component engineered for stealth and persistence. This payload is equipped with dedicated logic to conduct environmental fingerprinting, utilizing WMI queries such as SELECT * FROM AntiVirusProduct and SELECT * FROM Win32_VideoController to verify the host’s hardware profile and security posture. Furthermore, it features a robust cryptographic suite employing hardcoded AES keys to secure outbound exfiltration and decrypt incoming Command-and-Control (C2) instructions. The integration of the AES-256 algorithm effectively masks malicious activities from standard network-based detection systems.
5. In-memory execution & keylogging
XWorm version 7.1 payload is used with helper DLL for this attack. The decrypted malicious payload is not stored on disk and runs entirely in the memory space of the compiler. This payload performs Anti-Virus checks using “SELECT * FROM AntiVirusProduct” and Anti-VM checks using “SELECT * FROM Win32_VideoController”. Although the XWorm payload used in the attack is not fully equipped with plugins, it is capable of performing data capturing through keystrokes, modifying the \drivers\etc\hosts files, encrypting and decrypting using the AES algorithm, initiating and stopping DDOS attacks, downloading and executing files, logging, and is capable of logging off, restarting, and shutting down the victim machine.
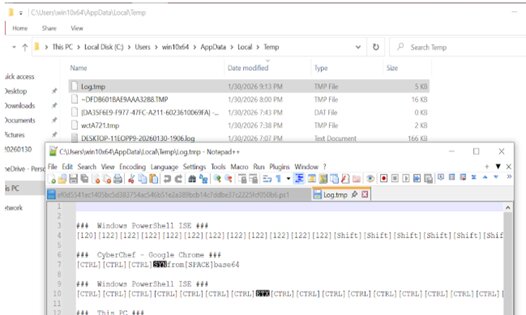
The primary goal of the malware is keylogging. The malware records every keystroke and saves the data to a hidden log file in the %TEMP% folder.
The following image contains strings of the legitimate Aspnet_compiler.exe file:
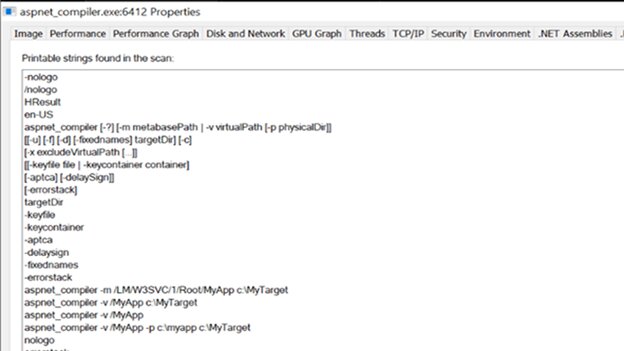
The following image lists the malicious strings in memory of Aspnet_compiler.exe after Reflective dll injection:
The following image shows the AES key and XWorm version used in the attack:
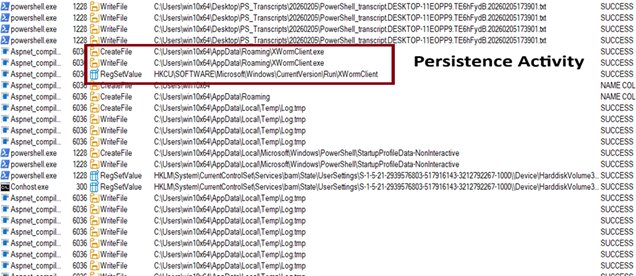
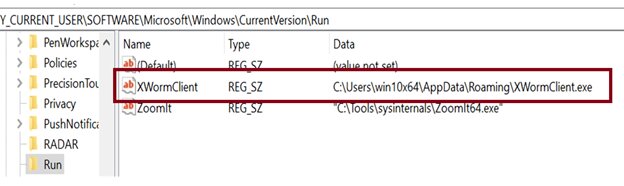
6. Persistence mechanism (Managing registry-based persistence)
Aspnet_compiler.exe is renamed to XWormClient.exe and is used as a host process during persistence through the Windows Run registry key:
Abusing Microsoft binaries
We can see the file in the location ‘C:\Users\win10x64\AppData\Roaming\XWormClient.exe’ is actually a legitimate Microsoft file which was earlier present in 'C:\Windows\Microsoft.NET\Framework\v4.0.30319\Aspnet_compiler.exe'
7. Data exfiltration
The malware logs user keystroke activity in a log file in the %temp% folder
Finally, the malware encrypts the collected log file and sends it back to the attacker's Command & Control (C2) server at specified time intervals. We have seen port 7003 used for this process via the TCP protocol.
- C2 IP address: 204.10.160.190
- Network tactic: The data is exfiltrated via an encrypted channel to prevent Network Intrusion Detection Systems (NIDS) from seeing the raw passwords or sensitive data being stolen.
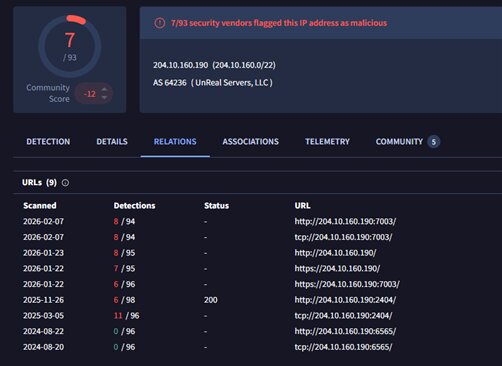
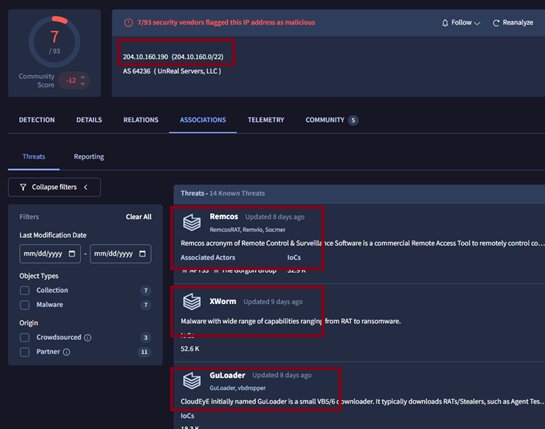
8. Hunting the malware infrastructure
When analysing the IP address used for data exfiltration, we found the same IP address associated with other malware campaigns and different malware families.
XWorm v7.1 Plugins:
Post-exploitation modules: Assessing post-compromise tools
- Monitoring of files, registry, screen, web browser tabs, WebCam and microphone
- Modify processes, services, startup, and clipboard managers
- Password stealer
- DDOS Attack
- Power on and off
- UAC bypass
- Commands and file execution
- Install programs
- Anti-decompile (Dnspy, .Net Reflector, DotPee)
- TCP connections
Conclusion
XWorm’s emergence as a top-tier global threat represents a fundamental shift in the cybercrime economy. With the release of Version 7.1, the malware has transcended its "script-kiddie" origins, demonstrating that modern commodity tools now integrate APT-level deceptive tactics. By pivoting from predictable file-based execution to memory-resident, "Living off the Land" (LOTL) techniques, XWorm effectively neutralizes signature-reliant defenses. The strategic abuse of legitimate utilities—such as Aspnet_compiler.exe—combined with reflective DLL injection, enables attackers to remain invisible to legacy security stacks. Furthermore, by weaponizing trusted platforms like Discord and exploiting critical vulnerabilities such as CVE-2025-8088 (WinRAR), XWorm has successfully bridged the gap between low-cost accessibility and high-impact enterprise disruption. For security leaders, the "commodity" label no longer implies simplicity; it now signifies a highly optimized, modular, and relentlessly evolving adversary.
XWorm’s rapid ascent to the #3 global threat ranking necessitates an immediate transition toward a proactive, behavior-based security posture. Resilience against this modular threat is predicated on the following technical pillars:
- The human layer remains the most exploited attack surface — treat it accordingly: Phishing remains the preeminent vector for initial access in modern cyber-operations. Given that XWorm’s delivery mechanism exploits sophisticated, business-contextualized social engineering—exemplified by the "MFEQuotation" lure—organizations must transcend traditional, compliance-mandated awareness training. Personnel should be conditioned to maintain a posture of heightened scrutiny toward compressed or encrypted attachments, irrespective of the perceived legitimacy of the sender’s corporate identity.
- Upstream threat interdiction: Deploy high-fidelity mail and web filtering to intercept malicious ZIP/RAR stagers. Particular attention must be paid to the remediation of CVE-2025-8088, which serves as a critical entry point for path-traversal-based deliveries.
- Advanced behavioral detection: Beyond signature-based prevention, EDR must be tuned to alert on the "Living off the Land" (LotL) tactics identified in the 7.1 kill chain. Focus on process hollowing and credential-theft functions initiated by legitimate .NET binaries.
- Accelerated vulnerability lifecycle management for peripheral software: The weaponization of path-traversal vulnerabilities, such as CVE-2025-8088, underscores the acute risk profile of "N-day" exploits targeting ubiquitous third-party utilities. Security leadership must mandate an expedited patching cadence for archive management software (e.g., WinRAR 7.13+) and other peripheral applications that frequently reside outside the scope of automated enterprise patching workflows. Strengthening the governance of this software tier is critical to preventing adversaries from exploiting the "patch gap" to gain persistent footholds.
- Exfiltration suppression: Utilize continuous network monitoring to pinpoint the exfiltration of keylogs and stolen credentials. By identifying the specific AES-masked communication patterns on Port 7003, organizations can significantly reduce the "dwell time" of the XWorm agent.
To mitigate the risks posed by modular threats like XWorm, Trellix employs a multi-layered defensive strategy that secures the enterprise perimeter and internal assets alike. This orchestrated approach utilizes Trellix Email Security to thwart initial delivery, while Trellix EDR and Trellix Endpoint Security (ENS/HX) provide deep-visibility detection of obfuscated command execution and persistence mechanisms. Visibility into the command-and-control (C2) stage is maintained through specialized network and cloud security modules, supported by the MVX engine for the isolated analysis of evasive samples. By synthesizing data from disparate vectors through an AI-enhanced correlation engine, Trellix bridges the gap between isolated alerts and a unified view of the adversary lifecycle. This intelligence-led framework ensures that security teams can outpace the rapid evolution of global threats, shifting the paradigm from simple detection to durable resilience.
Indicators of Compromise (IOCs)
| FileType | Name | SHA256 |
| Temp[82].eml | c6739ae299cde3ba604886f86df328ecdeb5ddad440d05b22b71580483a358b3 | |
| ZIP | MFESEK3180110RA - MFEQuotation Work request for NCSOCSO.zip | a699b2b370023fe9a77e6297fae942271debdc8f2a6589f701e5cc84239f2446 |
| JavaScript | MFESEK3180110RA - MFEQuotation Work request for NCSOCSO.js | 2310a8c9c8c8d27053e63afc6ab66e1b2143e36c9e347368850eab5ba7b9dacf |
| PowerShell | ENCRYPTEDX.ps1 | ef0d5541ec1405bc5d383754ac546b51e2a389bcb14c7ddbe37c2225fcf050b6 |
| Helper DLL | Mafia.dll | 3e7d97d4896130e2150f79e685dde01f26ed2f0882b9829b385b142c982c9176 |
| Payload | XWormClient.exe | 3ce1c96dd324e2485328c23eaa9d4bb17a7ee14d06f73de899d5bede07ffb3f1 |
| URL | hxxps[://]kolanga[.]cc/devils/ENCRYPTEDX[.]ps1 |
| IP Address and Port | tcp://204[.]10[.]160[.]190:7003 |
| Mutex | uUDkTzshM7rT3NdQ |
| AES Key | <V7PV7PV7PV7PV7P> |
Trellix Detection coverage
| Product | Detections |
| Trellix Endpoint Security (ENS) | JS/Downloader.jar Trojan-JARM!E4DB390D4E3A Trojan-FWBP!7D273DB94231 |
| Trellix Endpoint Security (HX) | Trojan.Generic.39452305 Trojan.GenericKDS.61382503 Trojan.GenericKDS.61382503 Gen:Variant.Application.Tedy.52869 Trojan.Generic.39454977 Generic.mg.7d273db94231ebe5 |
| Trellix Network Security Trellix VX Trellix Cloud MVX Trellix Malware Analysis Trellix Email Security Trellix Detection As A Service Trellix NX |
Trojan.JS.Heuristic Trojan.Win32.Kepavll Trojan.Generic FE_Backdoor_MSIL_XWORM_ Malicious.LIVE.DTI.URL |
| Trellix EDR | Wrote PE header into remote process (PE file DOS header) [T1106 T1055.002 T1620] runtimebroker.exe has been executed by an unusual process [T1059.003] Suspicious Process Execution (File Creation + Autorun entry) [T1547.001 T1105] Browsed suspicious domain weblink [T1566.002 T1204.001] Suspicious process created a file at a commonly abused path [T1105] Persistence (file to startup or run keys in registry) [T1547] Startup entry registered through services execution [T1547.001 T1112] External network connection was initiated via COM API [T1071 T1559.001] Performed native API call used to capture keyboard input [T1106 T1056.001 T1056.004] Process hollowed [T1106 T1055.012] Modified registry run keys under suspicious context [T1547.001 T1112] Deleted directory in quiet mode [T1070.004 T1485] Added content to registry executed at next Windows logon [T1547.001 T1112] Removed file from the system via Command-Line utility DEL command [T1059.003 T1070.004] |
IP and URL Trellix coverage
| URL | Trellix coverage |
| hxxps[://]kolanga[.]cc/devils/ENCRYPTEDX[.]ps1 | High Risk Malicious Sites Phishing PUPs (potentially unwanted programs) |
| C2 server IP | Trellix coverage |
| 204[.]10[.]160[.]190 | Medium-Risk PUPs (potentially unwanted programs) |
References:
- https://any.run/malware-trends/
- https://medium.com/@anyrun/malware-trends-overview-report-2025-8aba11baacd3
- https://www.cloudsek.com/blog/no-honour-among-thieves-uncovering-a-trojanized-xworm-rat-builder-propagated-by-threat-actors-and-disrupting-its-operations
- https://cloud.google.com/blog/topics/threat-intelligence/exploiting-critical-winrar-vulnerability
Discover the latest cybersecurity research from the Trellix Advanced Research Center: https://www.trellix.com/advanced-research-center/
RECENT NEWS
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
-
Dec 11, 2025
Trellix Finds 97% of CISOs Agree Hybrid Infrastructure Provides Greater Resilience
-
Oct 29, 2025
Trellix Announces No-Code Security Workflows for Faster Investigation and Response
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.
